系统地址:**.**.**.**/
管理员用户名admin 密码admin

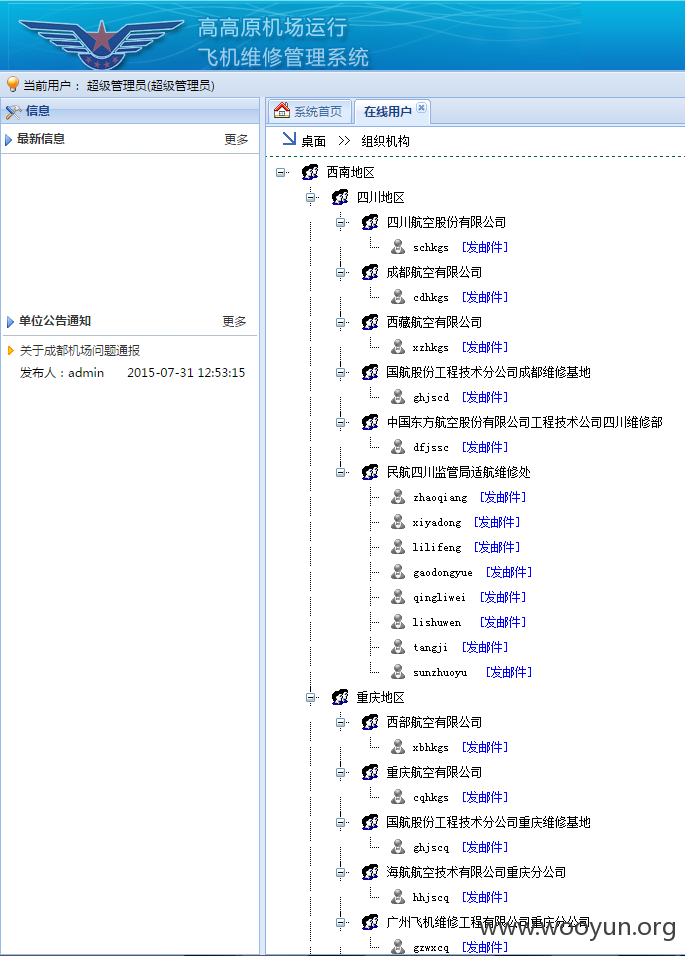
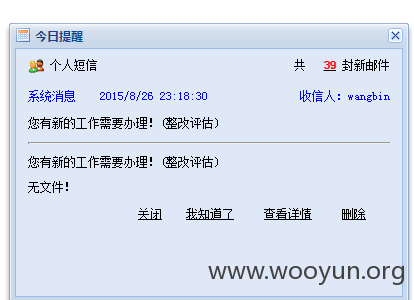
可给内部人员发邮件~:
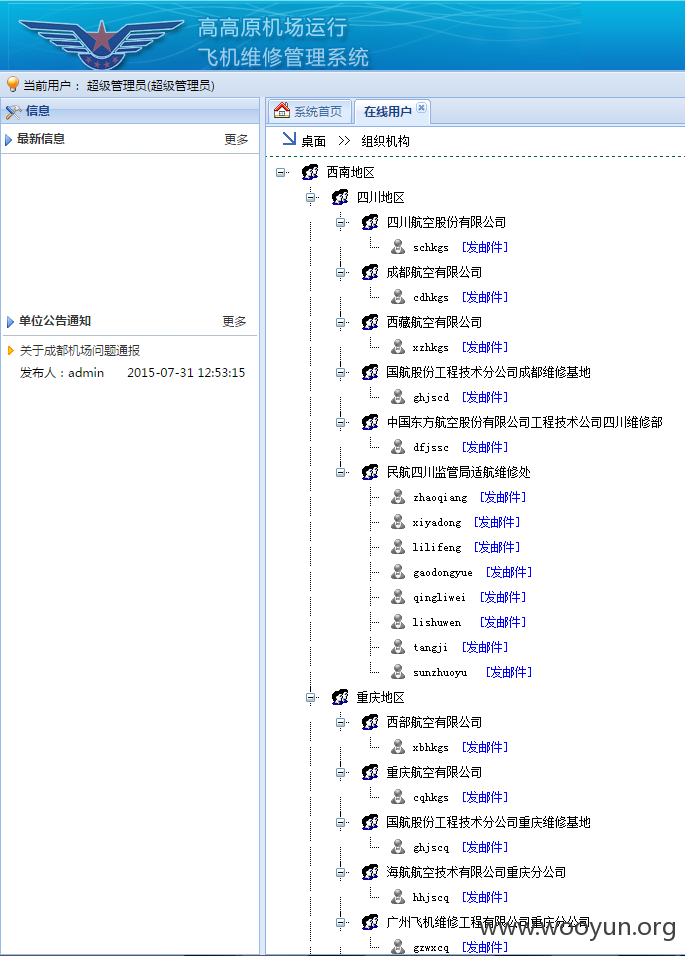
登陆页面无验证码,可爆破,爆破出来的密码是123456的用户:libo liuxin wangbin
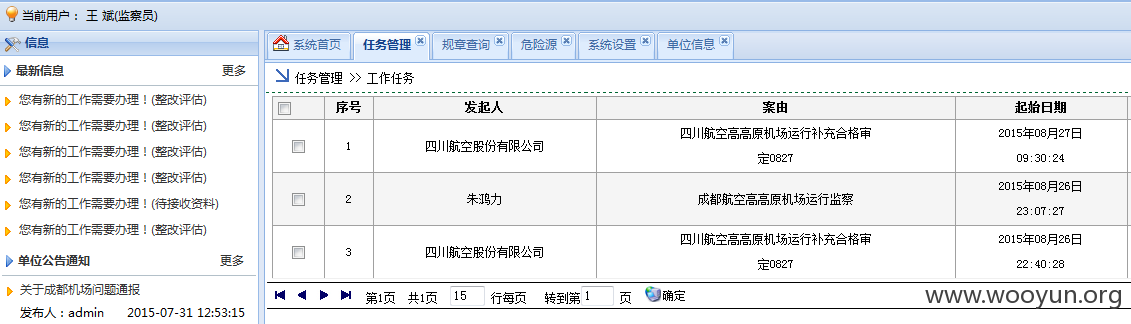
登陆一个看看~
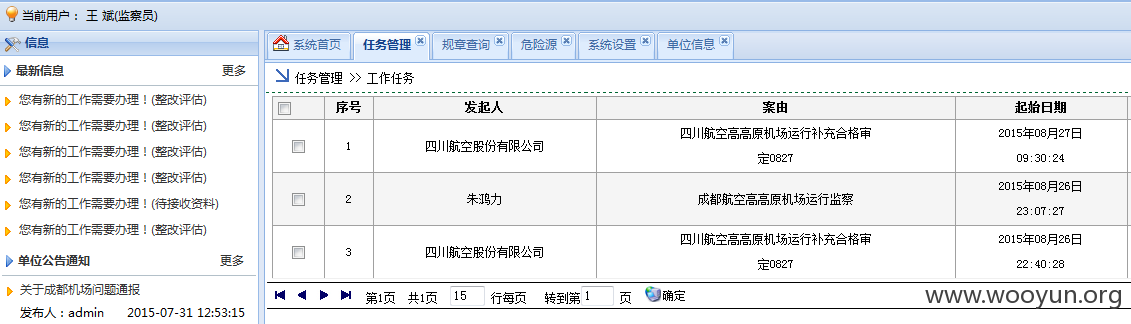
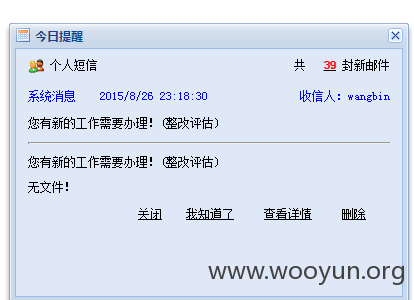
可查看内部邮件~
在后台逛了一圈,发现了3个注入点,测了下又是站库分离的~
1、**.**.**.**/BBS/BanKuaiView.aspx?ID=6
2、**.**.**.**/SystemManage/SystemJiaoSeUser.aspx?JiaoSeName=%B9%AB%CB%BE
(可执行系统命令)
3、**.**.**.**/PlanWorkFlow/PlaneFlowLCLB.aspx?ID=122
数据库
表~:
整个系统没有过滤参数,也没关报错,应该还有注入点