漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0153818
漏洞标题:中国邮储银行某内部系统多个漏洞(可直接获取内部敏感文件)
相关厂商:中国邮政储蓄银行
漏洞作者: 路人甲
提交时间:2015-11-17 09:15
修复时间:2015-11-25 09:00
公开时间:2015-11-25 09:00
漏洞类型:成功的入侵事件
危害等级:高
自评Rank:20
漏洞状态:漏洞已经通知厂商但是厂商忽略漏洞
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-11-17: 细节已通知厂商并且等待厂商处理中
2015-11-25: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
中国邮政储蓄银行某分行系统多个逻辑问题(可直接获取内部敏感文件),可获取到IOS客户端源代码
详细说明:
中国邮政储蓄银行四川省分行综合信息管理系统
http://118.112.186.175:2222/
#1 系统可任意注册(未校验内部邮箱等信息,只有审核机制)
注册一个账号为:测试,随意填入身份证号码和手机号码
提交后等待管理员审核,实际不需要审核就可以绕过登录认证进入系统
首先进行一次登录操作(密码为身份证后6位)
提示账号未审核
直接访问链接(自己输入,页面里没有)http://118.112.186.175:2222/super/index.php?c=welcome&m=index
成功进入系统
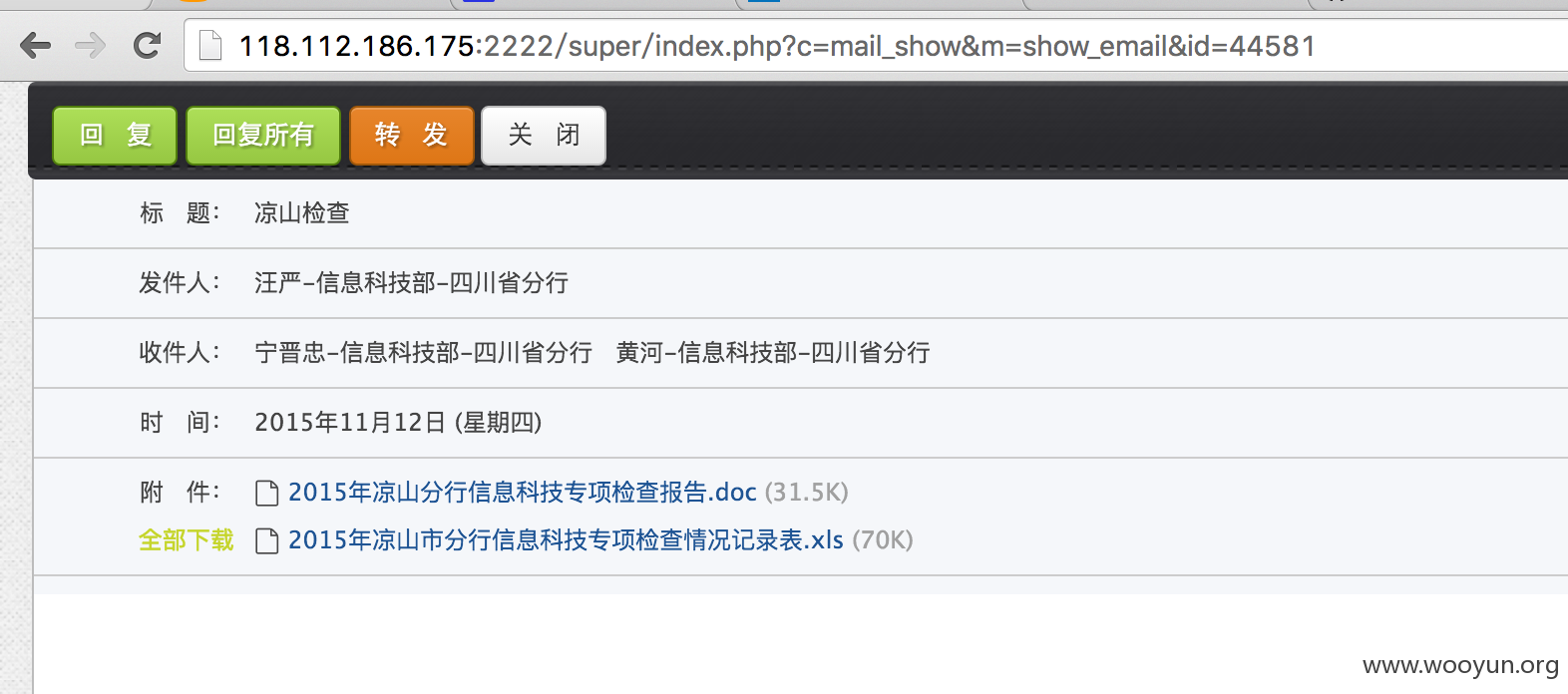
#2越权读取邮件(邮件中包含大量敏感的附件)
修改id,试验1-44581都行,以下为证明:
#3 越权下载任意附件
直接遍历attachments_id即可,不做过多证明。
#4注入,MYSQL数据库
equipment_id存在注入
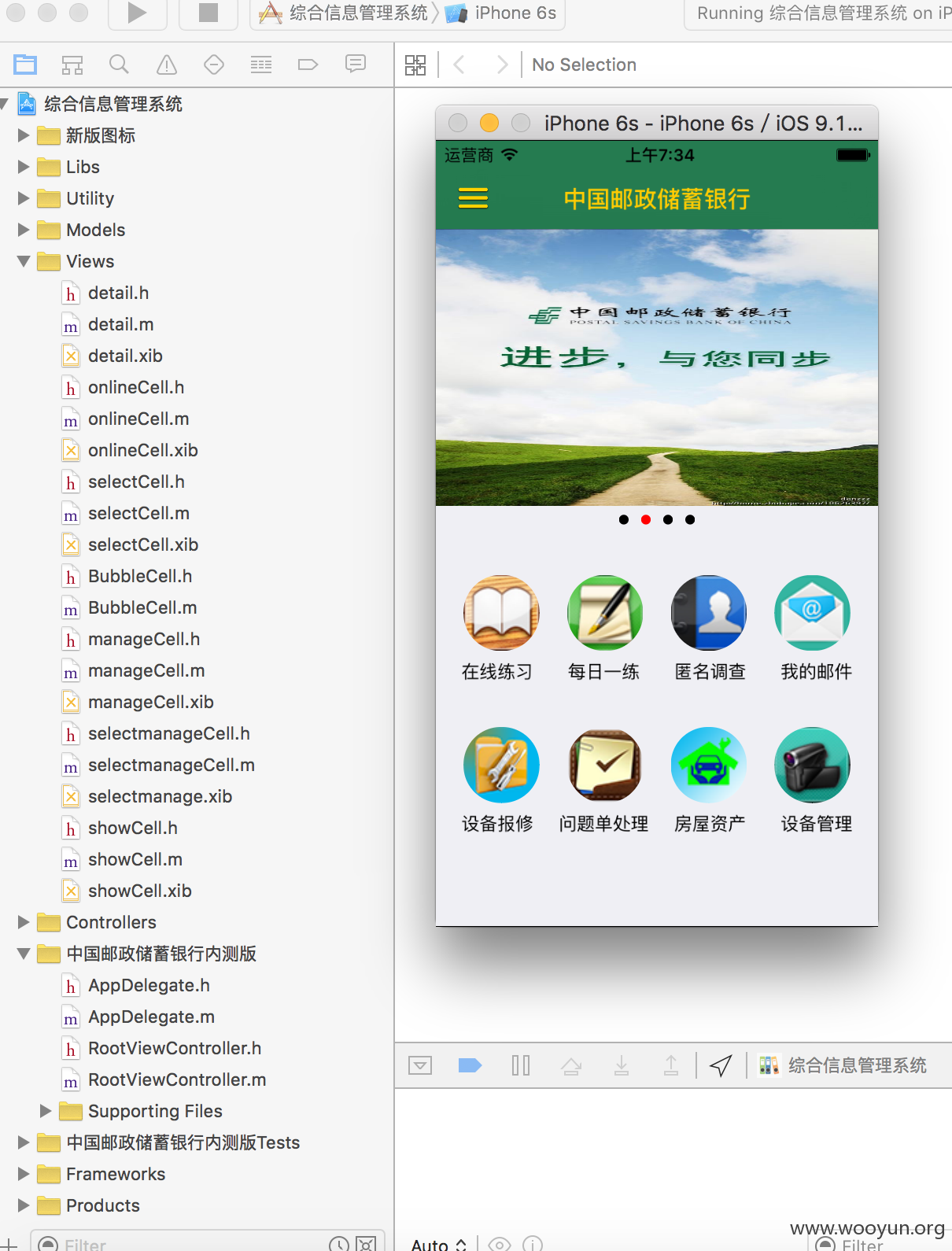
#5 邮储银行某手机客户端源代码直接泄露在github,可直接用Xcode编辑代码、重建工程(完整代码)
https://github.com/DevenZhao/ManageSystem/tree/5271f2bc2223c822aa0e4acd3a2c3a9200921cc8/%E4%B8%AD%E5%9B%BD%E9%82%AE%E6%94%BF%E5%82%A8%E8%93%84%E9%93%B6%E8%A1%8C%E5%86%85%E6%B5%8B%E7%89%88
以下是证明
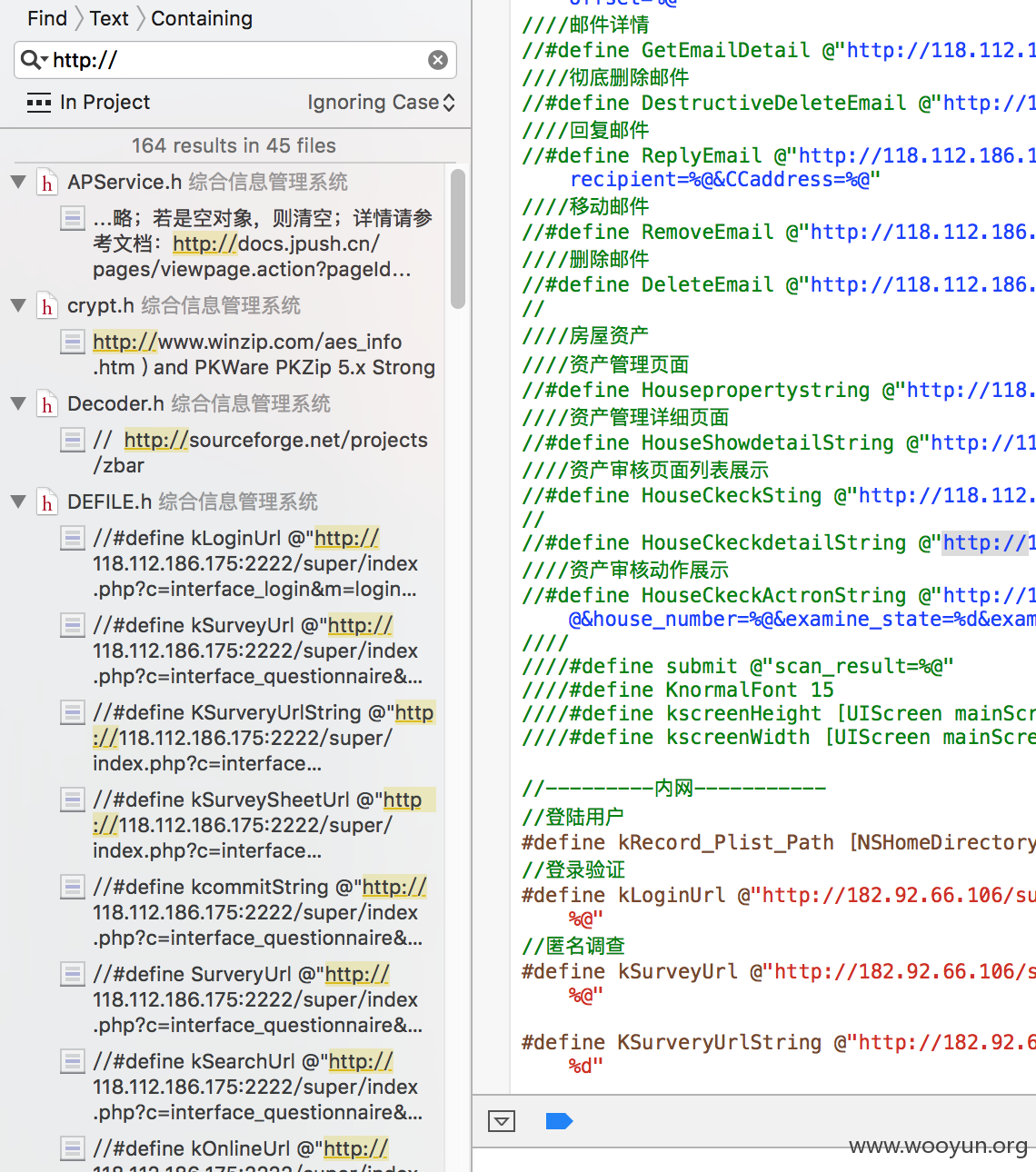
源代码中各种接口
漏洞证明:
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2015-11-25 09:00
厂商回复:
漏洞Rank:15 (WooYun评价)
最新状态:
暂无