.....
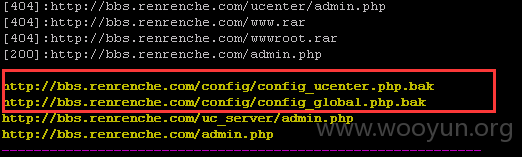
漏洞网站:http://bbs.renrenche.com/
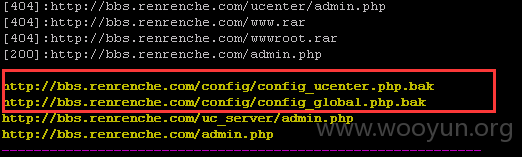
http://bbs.renrenche.com/config/config_global.php.bak
http://bbs.renrenche.com/config/config_ucenter.php.bak
http://bbs.renrenche.com/uc_server/admin.php
参考 WooYun: 途牛网某服务配置失误 导致论坛敏感文件泄露(致使百万用户信息告急)
一步一步将管理员帐号(“车车”和“renrenche”)都重置了,密码为123123。




至于shell就不拿了,dz3.2后台getshell基本无悬念。。。。