URL:http://brandbase.mama.cn/yikexin.php?ctype=*&mod=growth&op=detail&pgcount=12&tid=1520677
POST参数: page=20
存在问题参数ctype:
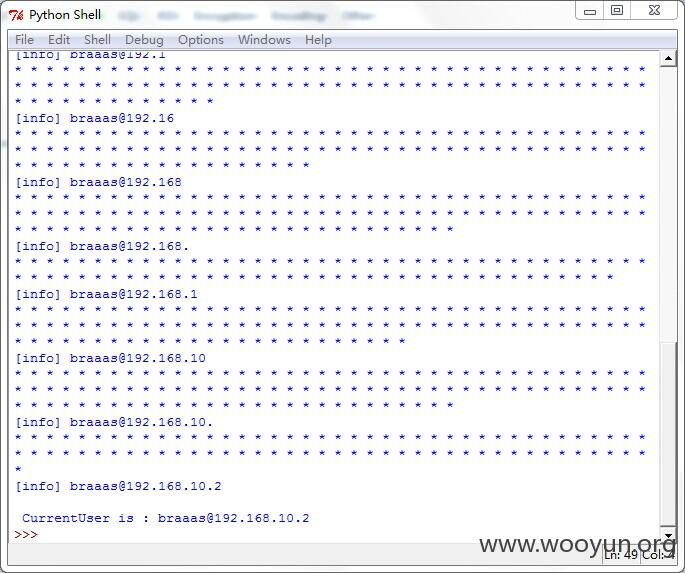
sqlmap跑不出来这个点,借助 lijiejie的脚本修改了下,不想自己造轮子。
本来因该是两个的,还有一个是主站,由于换了个网络环境,访问不到该URL了,不过我记得部分是
当前用户开头是hr什么什么的,长度是36,
URL:http://www.mama.cn:80/photo/index.php?a=Search&d=index&g=Search&gotosearch=yes&keyword=*&num=25&page=1&searchtype=photo
存在问题参数是keyword,
poc: