漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0109417
漏洞标题:看我如何进入17WO网站某后台并且拿下内网服务器
相关厂商:中国联通
漏洞作者: 金枪银矛小霸王
提交时间:2015-04-21 14:02
修复时间:2015-06-08 13:56
公开时间:2015-06-08 13:56
漏洞类型:成功的入侵事件
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-04-21: 细节已通知厂商并且等待厂商处理中
2015-04-24: 厂商已经确认,细节仅向厂商公开
2015-05-04: 细节向核心白帽子及相关领域专家公开
2015-05-14: 细节向普通白帽子公开
2015-05-24: 细节向实习白帽子公开
2015-06-08: 细节向公众公开
简要描述:
感谢 @scanf 兄弟。
详细说明:
说来也巧合的,你们联通一条短信就让我进去服务器。
一开始一条短信飞过来了
唔~ 访问下。一眼过去感觉有Struts2漏洞,可惜主站没有,搜下二级域名
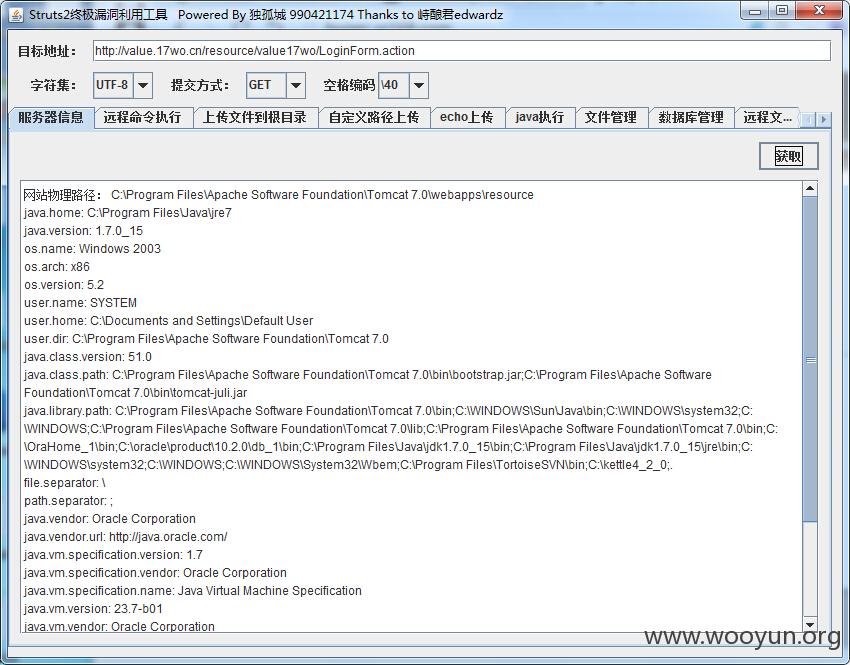
然后发现了这个
检测下。唔~这么老的洞还存在 struts2 05的
直接上传一句话,菜刀拿shell
查看下ip。原来是内网
然后使用getpass.exe获取到管理员的账号密码
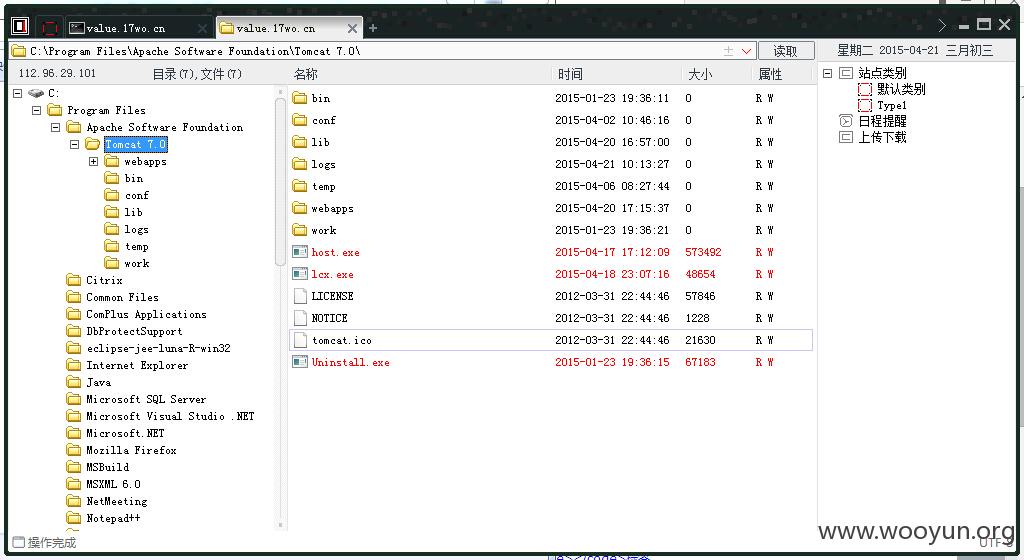
尝试用lcx.exe进行转发,但是失败了。@scanf 发了我一个工具 reDuH ,不错
开始GUI一连就崩,然后改用jar包进行转发,用nc进行监听
上传xx.jsp转发文件
本地执行执行java命令
再开启nc监听1010端口
再输入
帮内网服务器的3389经过1010端口转发到1234端口
本机mstsc连接输入127.0.0.1:1234即可连入
一连撸了几天,本来打算把整个段入侵的,谁知道你们服务器不给力。一扫就宕机了。。
在桌面找到一份文件
就这样你们懂的
漏洞证明:
修复方案:
升级
版权声明:转载请注明来源 金枪银矛小霸王@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:14
确认时间:2015-04-24 13:54
厂商回复:
CNVD未复现所述情况,已经转由CNCERT向中国联通集团公司通报,由其后续协调网站管理部门处置.
最新状态:
暂无




![315%B~`0T9{]T[)KWPWRAT9.jpg](http://wimg.zone.ci/upload/201504/211348158d250bf806ecfa406978968d291c9f15.jpg)