漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0104654
漏洞标题:广西师范大学网络基础架构和出校控制器的漏洞可能导致大范围拒绝服务攻击风险
相关厂商:广西师范大学
漏洞作者: 路人甲
提交时间:2015-10-03 12:52
修复时间:2016-01-11 15:32
公开时间:2016-01-11 15:32
漏洞类型:设计不当
危害等级:高
自评Rank:15
漏洞状态:已交由第三方合作机构(CCERT教育网应急响应组)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-10-03: 细节已通知厂商并且等待厂商处理中
2015-10-13: 厂商主动忽略漏洞,细节向第三方安全合作伙伴开放(绿盟科技、唐朝安全巡航)
2015-12-07: 细节向核心白帽子及相关领域专家公开
2015-12-17: 细节向普通白帽子公开
2015-12-27: 细节向实习白帽子公开
2016-01-11: 细节向公众公开
简要描述:
学校的网络架构和出校控制器存在漏洞,有存在拒绝服务攻击的风险
详细说明:
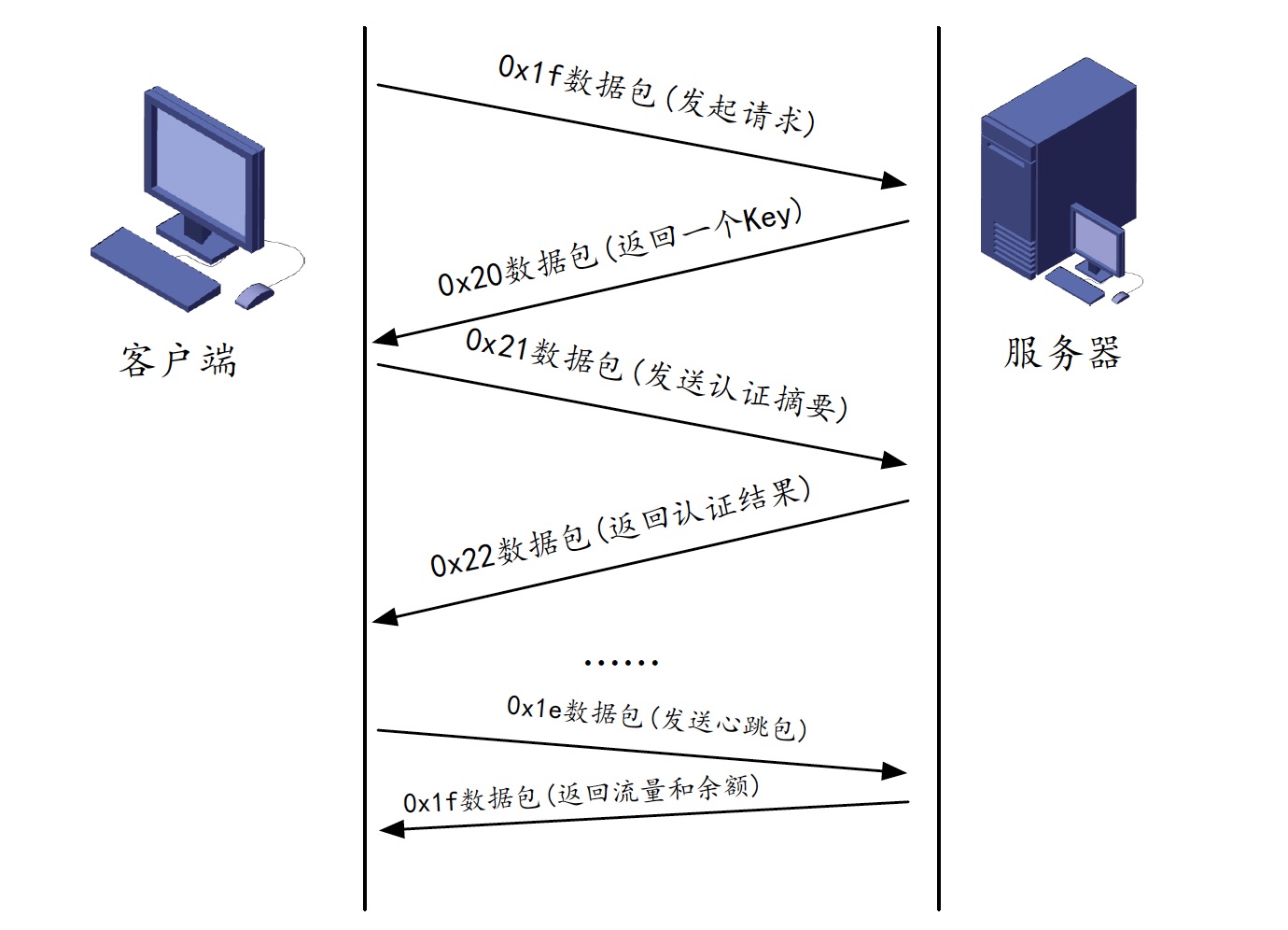
学校出校控制器的握手流程如下图所示:首先机器发出请求数据包,接下来服务器返回一个key,接下来本机再根据key计算出摘要,最后再返回一个认证结果。
但是学校最关键的问题在于
1、学校的路由器不做源地址认证
2、服务器收到错误的用户名和密码即进行掉线
所以A可以伪造任何B机器ip地址向**.**.**.**这个服务器发起请求,虽然伪造包的机器A收不到服务器返回的key,但是伪造包的机器A可以继续发送一个错误的认证摘要,这样就直接导致B机器掉线。通过自己机器试验,该方法测试有效。Python脚本见附件。
Python代码
漏洞证明:
路由器对源地址不作校验,所以发出错误的用户名和密码可以直接导致断网
修复方案:
1、路由器全部加上源地址认证(工作量比较大)
2、服务器修改策略,需要认证成功后才记录已经发出的key,作为后期心跳包校验的依据,同时单纯的密码错误不会掉线(工作量最小)
3、再返回认证摘要时,需要附带0x20的key,如果与0x20发出的key不一致则忽略该包(需要更新软件)
4、出校认证一律采用https网页认证
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2016-01-11 15:32
厂商回复:
漏洞Rank:15 (WooYun评价)
最新状态:
暂无