漏洞概要
关注数(24)
关注此漏洞
漏洞标题:电玩巴士后台管理系统SQL注入泄露多个重要数据库
提交时间:2015-03-30 10:16
修复时间:2015-05-14 10:58
公开时间:2015-05-14 10:58
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
Tags标签:
无
漏洞详情
披露状态:
2015-03-30: 细节已通知厂商并且等待厂商处理中
2015-03-30: 厂商已经确认,细节仅向厂商公开
2015-04-09: 细节向核心白帽子及相关领域专家公开
2015-04-19: 细节向普通白帽子公开
2015-04-29: 细节向实习白帽子公开
2015-05-14: 细节向公众公开
简要描述:
电玩巴士后台管理系统登录存在sql注入漏洞,泄露多个库
详细说明:
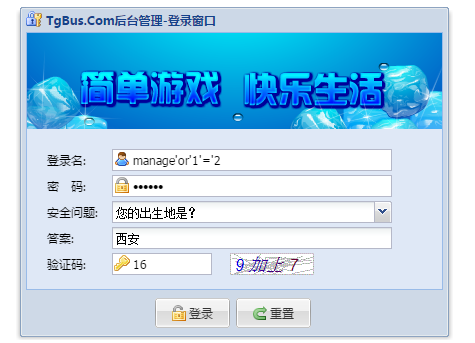
漏洞地址:http://superman.tgbus.com/login.shtml
这里的验证码不变,也为校验你的问题答案,导致可以直接进行工具注入
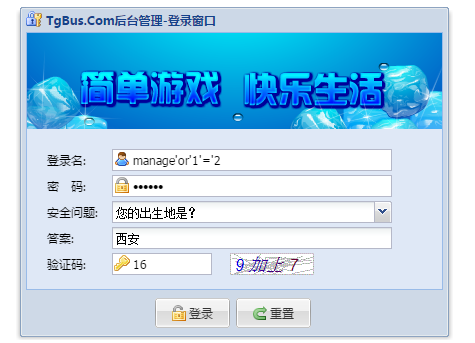
sqlserver 数据库,基于时间的,而且时间延迟的比较大,所以只列几个库说明情况,因为是后台管理系统,所以影响可想而知
漏洞证明:
看manage库出来了,未深入了,太慢了
修复方案:
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2015-03-30 10:56
厂商回复:
感谢白帽"Aug0st"对我站的热心关注.此漏洞现已确认是由于后台程序对登陆参数过滤不严格导致.现已提交到相关部门进行修复.再次感谢!
最新状态:
暂无