刚下了个74cms_v3.5.1_20141027.zip,diff了一下发现了下面的改动:
注释调了checkSignature(),是为了啥?????
WooYun: 74CMS最新版绕过继续任意文件读取(通用性分析)到任意文件删除 曾经分析过这里的XXE漏洞以及SQLI,不过,被次利用的是另外两个BUG。
先看code.
对整个POST_DATA做了addslashes。
然后:
$fromUsername从simplexml_load_string()后就直接进入了SQL中,addslashes($GLOBALS["HTTP_RAW_POST_DATA"])就解决了所有问题么?答案是否定的。因为XML中特殊字符也可以编码:
也就是说在XML中使用&apos就把'号注入进去了,并且这里post data没有任何过滤,可以注入任何SQL语句,所以我们可以导出整个数据库,甚至getshell.
看到下面的代码,也许有人会说,这里是有条件的,因为这里判断了$_CFG['weixin_apiopen']=='0')。
不过,这里的$_CFG['weixin_apiopen']真的有效么?下面的代码可以告诉我们:
在浏览器访问一下http://127.0.0.1:8081/74cms/test.php,结果为:
也就是在class object里面访问$_CFG是无效的。
那么,那么,
这个条件就是永远都不会成立的,不管你后台开不开weixin_api。
好了,所有条件限制都排除了,可以直接注入了。
一下为74cms_v3.5.1_20141027默认安装测试:
UNION SELECT:
获取支付相关的key:
错误信息里面的
就是表里面的数据。
管理员表:
getshell:
返回错误:
这是因为写shell.php需要有写权限,data目录不行。
但是,但是,我们也可以找一个肯定有写权限的目录:
注册一个普通用户,长传一个头像,这是会建立0777权限的目录:'data/avatar/100/2014',shell就传到这个目录吧。
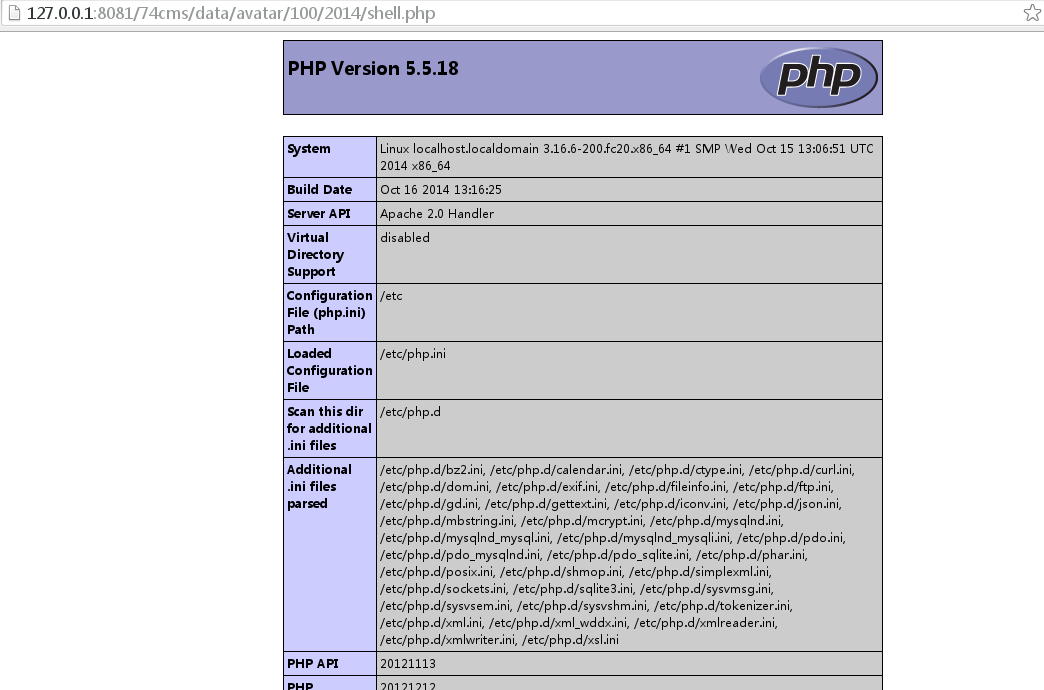
浏览器访问:
http://127.0.0.1:8081/74cms/data/avatar/100/2014/shell.php
获取支付相关的key:
管理员表:
getshell: