首先是通过搜索引擎大法找到后台:http://120.31.131.166:82/
发现是应用汇的后台,里面各种操作完全无权限限制,各种数据



发现数据量还是蛮大的。
接着找到注入一枚:http://120.31.131.166:82/soft_series_cps.php?series_id=-1
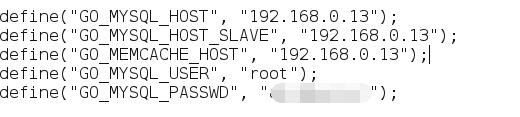
权限:root

好多数据库,不过想来想去只能脱裤子,什么都做不了,上不了马。
这边卡住了。
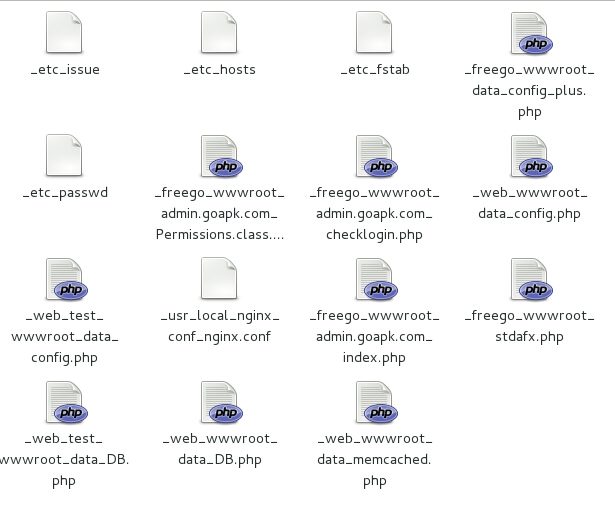
接着去尝试读取文件,发现系统的权限也挺高,什么文件都能读取。
但是不知道项目的目录,没办法读取他的项目文件。
又卡住了。。。
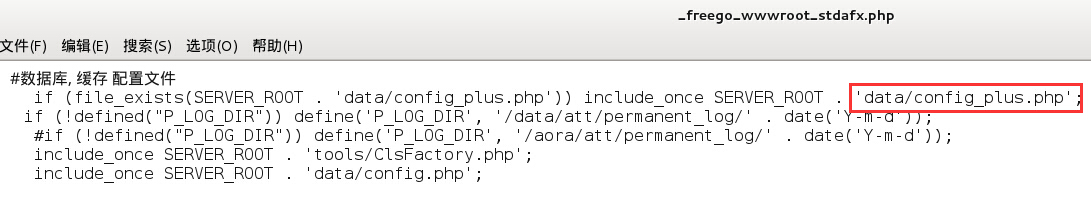
忽然我头顶的灯泡闪了两下,他的服务器是nginx的。那我是不是可以读取nginx的配置文件呢,这样我就可以知道他的项目都放在哪里,就可以写文件了。
于是去读取nginx的配置,发现也不知道他的nginx配置在哪里,,,
不过nginx配置放在哪里应该跟系统有关系,服务器是linux系统,读取/etc/issue文件,是centos。
然后百度了一下,知道centos的nginx配置放在/usr/local/nginx/conf/nginx.conf
ok go!
哇,果然读出了nginx的配置。
看到了好多项目,但是具体不知道哪个项目。
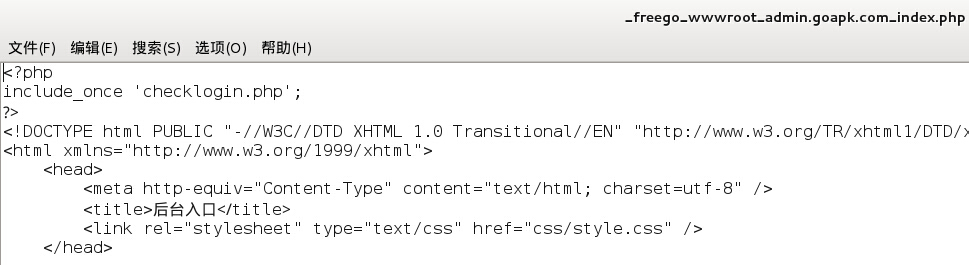
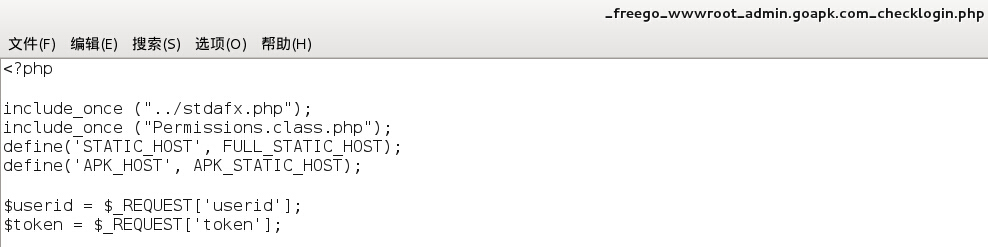
又通过一遍遍的测试发现,我访问的后台放在/freego/wwwroot/admin.goapk.com/
至此,服务器能不能拿下已经显而易见了。只需要sqlmap传一个马到上面的路径下就可以了。
由于我是好学生,以及种种原因,我不想往上面放马。权限都有了,放马只差一个点击。如果非要放马才能证明严重性,请私信我,送大马一只,服务器shell。