漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-073215
漏洞标题:投注网伪静态sql注入、短信轰炸、前端绕过
相关厂商:投注网
漏洞作者: 路人甲
提交时间:2014-08-21 10:50
修复时间:2014-10-05 10:50
公开时间:2014-10-05 10:50
漏洞类型:SQL注射漏洞
危害等级:低
自评Rank:3
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-08-21: 细节已通知厂商并且等待厂商处理中
2014-08-21: 厂商已经确认,细节仅向厂商公开
2014-08-31: 细节向核心白帽子及相关领域专家公开
2014-09-10: 细节向普通白帽子公开
2014-09-20: 细节向实习白帽子公开
2014-10-05: 细节向公众公开
简要描述:
投注网伪静态sql注入、短信轰炸、前端绕过
详细说明:
1、sql注入:80 8080 8888端口均有此问题
以80端口的一个链接为例
http://goucai.touzhu.cn/actinfo/news_39692.html
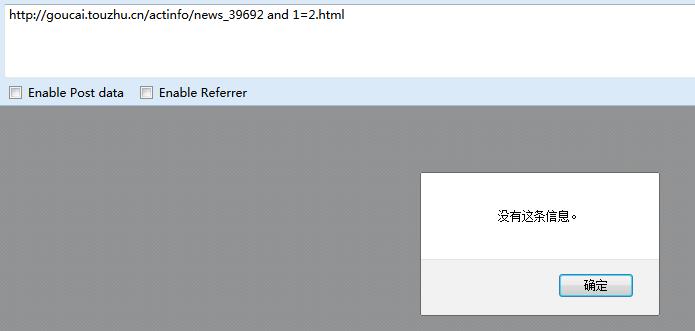
http://goucai.touzhu.cn/actinfo/news_39692 and 1=1.html
http://goucai.touzhu.cn/actinfo/news_39692 and 1=2.html
2.短信轰炸
只以一个发短信接口为例,其他可能还有,需要自查。
3.div浮层绕过
http://goucai.touzhu.cn/customer/toUserEmail.php 修改验证邮箱,没实名认证会弹div浮层。
审查元素,删除<div style="display:block" id="pzzceng"></div>,可绕过限制
漏洞证明:
1、sql注入:80 8080 8888端口均有此问题
以80端口的一个链接为例
http://goucai.touzhu.cn/actinfo/news_39692.html
http://goucai.touzhu.cn/actinfo/news_39692 and 1=1.html
http://goucai.touzhu.cn/actinfo/news_39692 and 1=2.html
2.短信轰炸
只以一个发短信接口为例,其他可能还有,需要自查。
3.div浮层绕过
http://goucai.touzhu.cn/customer/toUserEmail.php 修改验证邮箱,没实名认证会弹div浮层。
审查元素,删除<div style="display:block" id="pzzceng"></div>,可绕过限制
修复方案:
修复吧
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2014-08-21 10:55
厂商回复:
十分感谢.大牛的关注.已经安排技术处理.
最新状态:
暂无